USENIX Security '20: How Automation is Revolutionizing Chosen Ciphertext Attacks 🔐
Discover how researchers Gabrielle Beck, Maximilian Zinkus, and Matthew Green from Johns Hopkins University are advancing the automation of chosen ciphertext attacks, revealing new insights into cryptographic vulnerabilities.

USENIX
272 views • Sep 14, 2020
About this video
Automating the Development of Chosen Ciphertext Attacks
Gabrielle Beck, Maximilian Zinkus, and Matthew Green, Johns Hopkins University
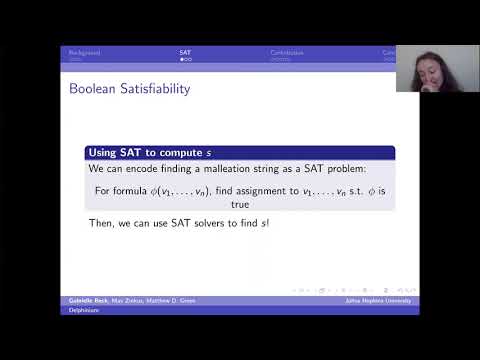
In this work we investigate the problem of automating the development of adaptive chosen ciphertext attacks on systems that contain vulnerable format oracles. Unlike previous attempts,which simply automate the execution of known attacks, we consider a more challenging problem: to programmatically derive a novel attack strategy, given only a machine-readable description of the plaintext verification function and the malleability characteristics of the encryption scheme.We present a new set of algorithms that use SAT and SMT solvers to reason deeply over the design of the system, producing an automated attack strategy that can entirely decrypt protected messages. Developing our algorithms required us to adapt techniques from a diverse range of research fields, as well as to explore and develop new ones. We implement our algorithms using existing theory solvers. The result is a practical tool called Delphinium that succeeds against real-world and contrived format oracles. To our knowledge, this is the first work to automatically derive such complex chosen ciphertext attacks.
View the full USENIX Security '20 program at https://www.usenix.org/conference/usenixsecurity20/technical-sessions
Gabrielle Beck, Maximilian Zinkus, and Matthew Green, Johns Hopkins University
In this work we investigate the problem of automating the development of adaptive chosen ciphertext attacks on systems that contain vulnerable format oracles. Unlike previous attempts,which simply automate the execution of known attacks, we consider a more challenging problem: to programmatically derive a novel attack strategy, given only a machine-readable description of the plaintext verification function and the malleability characteristics of the encryption scheme.We present a new set of algorithms that use SAT and SMT solvers to reason deeply over the design of the system, producing an automated attack strategy that can entirely decrypt protected messages. Developing our algorithms required us to adapt techniques from a diverse range of research fields, as well as to explore and develop new ones. We implement our algorithms using existing theory solvers. The result is a practical tool called Delphinium that succeeds against real-world and contrived format oracles. To our knowledge, this is the first work to automatically derive such complex chosen ciphertext attacks.
View the full USENIX Security '20 program at https://www.usenix.org/conference/usenixsecurity20/technical-sessions
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
272
Duration
12:17
Published
Sep 14, 2020
Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.