Search Results for "emdr sleep protocol"
Find videos related to your search query. Browse through our collection of videos matching "emdr sleep protocol". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "emdr sleep protocol"
50 results found
34:55
Episode 1 - The Protocol Paradox in Cryptography and System Security
Maitt Saiwyer
3 views
15:51
Verifpal Cryptographic Protocol Analysis for Students and Engineers
All Hacking Cons
24 views
59:35
Webinar on "Quantum Concept's":- Quantum Key Distribution (BB84) Protocol for beginner's
VK
846 views
1:24:09
Stanford Seminar - The TLS 1.3 Protocol
Stanford Online
23.6K views
49:42
Quantum cryptography | BB84 Protocol, Security & Future Trends | Exploring Future of QM Cryptography
Research Tech info
103 views
0:16
A2A-Protocol die neue Multi-Agent KI #ki #googleai #automation #softwareentwicklung #ai #agents #llm
genPsoft GmbH - agile Softwareentwicklung nach Maß
168 views

1:06
Which Protocol Secures Wi-Fi Best? | WPA3 Explained #TechQuiz #Cybersecurity #WiFiSecurity #TechTips
TECHLOGICS
132 views
5:59
Key Distribution Center (KDC) Protocol for Generation of Session Keys
Network Security Wallah
1.7K views
26:07
A Multiparty Commutative Hashing Protocol based on the Discrete Logarithm Problem
Computer Science & IT Conference Proceedings
44 views

13:22
Needham and Schroeder Protocol
WorthWatching
32.3K views
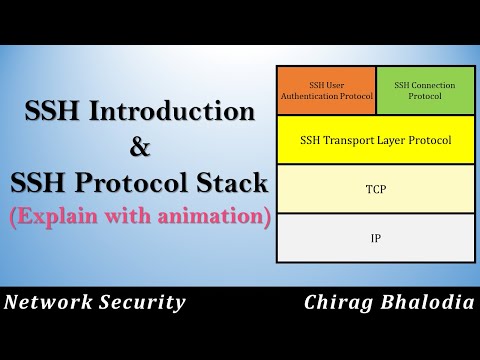
25:33
SSH | SSH Protocol Stack | SSH Protocols explain with animation | Why SSH? | Secure Shell (SSH)
Chirag Bhalodia
22.9K views
11:09
Quantum Key Distribution (BB84 Protocol) Explained Simply | Quantum Cryptography Made Easy
Engineering_enigma
66 views
30:27
LoneStarRuby 2015 - Building a binary protocol client in Ruby: A magical journey!
Confreaks
893 views
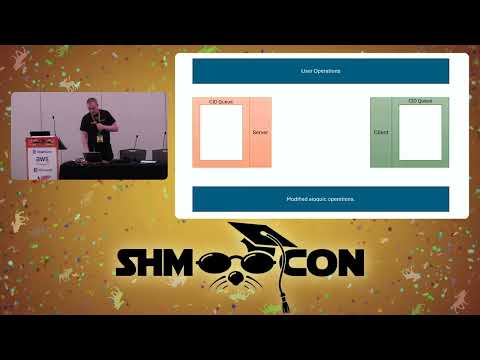
17:43
ShmooCon 2025 - On Covert Channels Using QUIC Protocol Headers
David Cheeseman
102 views

27:57
Lecture 6. The Signal Protocol (Applied Cryptography 101: Real-World Deployments)
Cryptography 101
1.5K views

11:59
41.Quantum key distribution II: EPR protocol
Jochen Rau
892 views
25:14
Internet Security (IP) Protocol - Security Assosiations & IKE ( Internet Key Exchange)- #21is71 #cns
VTU padhai
2.3K views
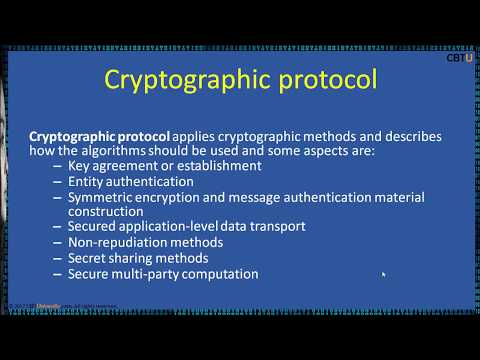
6:59
19.4 Cryptographic protocol
World Gurukul way of Learning Values and Wisdom
3.6K views
9:33
The Diffie-Hellman Protocol (ft. Serge Vaudenay)
ZettaBytes, EPFL
4.1K views
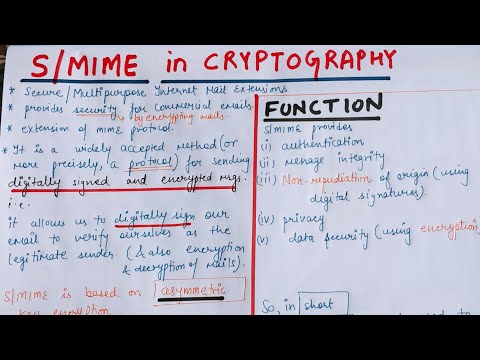
10:02
S/MIME protocol in Hindi | Cryptography and Network Security
Abhishek Sharma
142.4K views

3:00
What’s the weirdest security protocol you’ve ever seen at work?
Fiffy Patas
4.1K views

3:20
CLIENT SIDE SECURE IMAGE DEDUPLICATION USING DICE PROTOCOL
MICANS INFOTECH PVT LTD
113 views

3:24
Skeng X Sparta - Protocol (Official Music Video)
Skeng
104.2M views

1:02:51
DEF CON 8 - Bennett Haselton - A protocol that uses steganography to circumvent
DEFCONConference
202 views

6:32
URGENT - Tounkara réagit au discours en anglais de Diomaye Faye et tire sévèrement sur le protocol
Senegalactu Tv
88.7K views
21:34
How to End your Phone Addiction (Social Media Detox Protocol)
Abraham
2.4M views
0:40
CCMP - Counter-Mode/CBC-MAC Protocol - Security+
Geekus Maximus
86 views
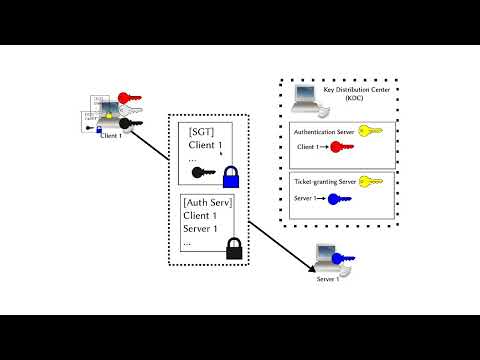
14:24
The Kerberos Authentication Protocol Explained
Suckless Programmer
306 views
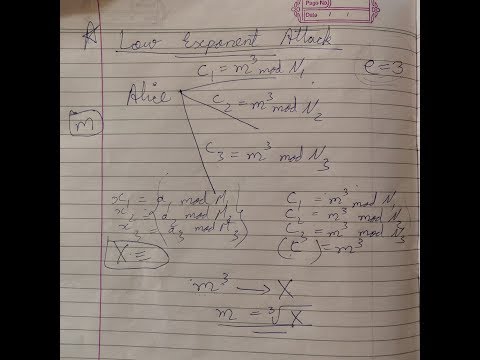
14:08
Low Exponent Attack | Attacks on RSA | Protocol Failure Attack | Cryptography & Network Security
Quick Trixx
11.4K views
3:03
Is The BB84 Protocol Essential For Quantum Cryptography? - Quantum Tech Explained
Quantum Tech Explained
14 views
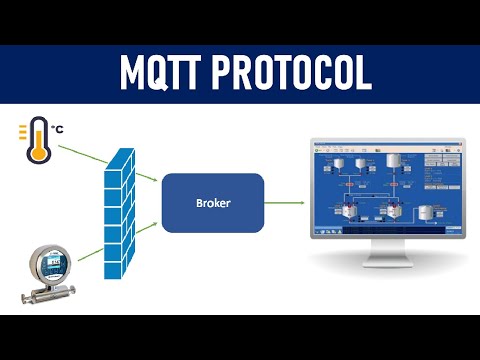
7:19
What is MQTT Protocol ? How it works ? | 2022
IT and Automation Academy
178.4K views

14:39
HAVEN GAMES AND HOBBIES Marvel Crisis Protocol MCP Tournament Baron of Dice RSMP Tabletop
RSMP Tabletop
2.0K views
5:43
How To Hide A Message In An Image (Steganography) Using Linux Terminal | The Protocol S
The Protocol S
140 views
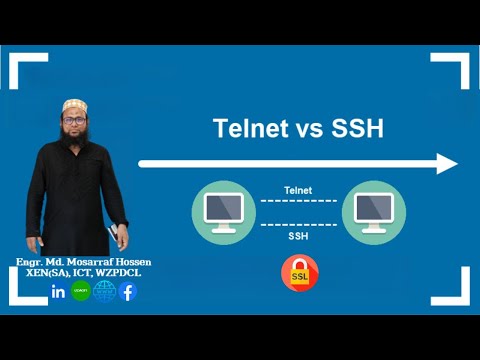
5:06
Telnet vs SSH Protocol | Why SSH is More Secure than Telnet!
Md. Mosarraf Hossain
148 views

1:04
SSL vs TLS: Which Encryption Protocol Is Better?
CyberPhormX
115 views
39:35
19-Learn Kerberos in Network Security 🔐 | How Kerberos Works? | Authentication Protocol Made Simple
Sundeep Saradhi Kanthety
184.1K views
9:58
COMP90043 Cryptography and Security - PAKE Protocol Introduction
WH
343 views
7:50
Marvel Crisis Protocol: Let's take a look at the Dice needed and their symbols (How to play)
Rage Against The Dice
240 views

2:09
Entanglement-based Key Distribution: the E91 protocol
Aliro
1.6K views

2:48
Internet Protocol Security (IPSec)
Vaishali Tutorials
27.5K views
1:07:03
Steve Girvin: Secure Communication in a Quantum World – BB84 Protocol
Yale University
4.3K views

1:01
Symmetric Cryptography - AES Encryption - Exa Protocol #shorts
Exa Protocol
96 views
3:48
How Do You Choose The Right Encryption Protocol? - Internet Infrastructure Explained
Internet Infrastructure Explained
1 views
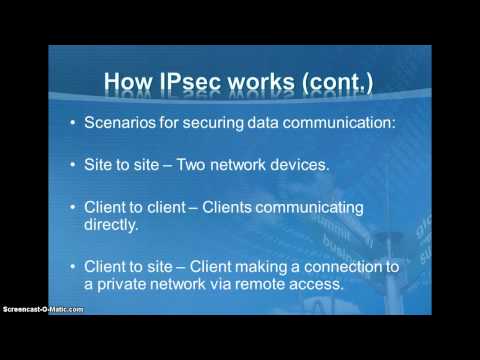
5:11
Internet Protocol Security
dnizi2000
3.7K views

9:24
Kerberoes protocol in Cryptography and Network Security #cryptography #education #computerscience
Lab Mug
1.8K views
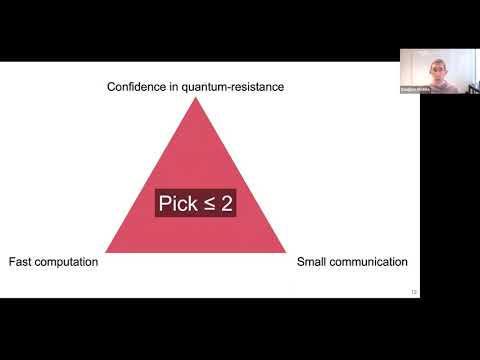
53:08
Transitioning the TLS protocol to post-quantum cryptography
CANS - Cryptology and Network Security
1.0K views

16:34
Graciela Bachu: The BB84 Quantum Cryptography Protocol (TSI)
Talaria
221 views
36:57
CompTIA Security+ Full Course: Network Protocol Security
Certify Breakfast
3.0K views
0:05
Echo Protocol Wallet Compromised
Crypto Liaison
20 views

7:47
Basic concepts of web applications, how they work and the HTTP protocol
Natural Programmer
1.6M views