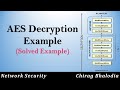
How to solve AES Decryption example | AES Decryption Example | Solved Example
How to solve AES Decryption example | AES Decryption Example | Solved Example | How to decrypt data using AES | Solved Example of AES decryption | AES Invers...
Chirag Bhalodia
25.8K views • Jun 27, 2022
About this video
How to solve AES Decryption example | AES Decryption Example | Solved Example | How to decrypt data using AES | Solved Example of AES decryption | AES Inverse Transformation Function
Follow my blog: https://www.chiragbhalodia.com/2021/09/aes-algorithm.html
In this video, I have explained all inverse transformation fuctions of AES with example (AES decryption process) in this video. Watch carefully. AES Solved example. AES decryption process explain with example.
For decryption, each round consists of the following four steps: Inverse Sub Bytes, Inverse Shift Rows, Inverse Mix Columns, Inverse Add Round Key.
Above steps also called AES inverse transformation function.
AES Inverse Sub BytesTransformation Function:
AES defines a 16 x 16 matrix of byte values, called an inverse S-box, that contains a permutation of all possible 256 8-bit values. These row and column values serve as indexes into the inverse S-box to select a unique 8-bit output value.
AES Inverse Shift RowsTransformation Function:
Rules of Inverse shifting rows,
Row 1 - No Shifting
Row 2 - 1 byte circular right shift
Row 3 - 2 byte circular right shift
Row 4 - 3 byte circular right shift
AES Inverse Mix Column Transformation Function:
AES inverse mix column transformation function is operates on each column individually. Each byte of a column is mapped into a new value that is a function of all four bytes in that column. Here in this function State Array is output of previous transformation function of decryption process.
AES Inverse Add Round Key Transformation Function:
The 128 bits of State are bitwise XORed with the 128 bits of the round key. Inverse add round key proceeds one column at a time.
0:00 Introduction
0:15 Outline
0:45 AES Inverse Sub Bytes (Explain with example)
3:37 AES Inverse Shift Rows (Explain with example)
6:30 AES Inverse Mix Column (Explain with example)
37:25 AES Inverse Add Round Key (Explain with example)
If you like my video contents, please LIKE, COMMENT, SUBSCRIBE & SHARE with your friends.
--------------------------------------------------------------------------------------------------------------
Check out other video on my channel
Block Cipher and Stream Cipher:
https://youtu.be/-gQrm5j0RkQ
Confusion & Diffusion (Frustrated Statistical Analysis or Claud Shannon Properties):
https://youtu.be/PJrW6ZqQipo
Feistel Cipher Structure (to understand DES):
https://youtu.be/emJ0p6h48u4
Data Encryption Standard (DES) Algorithm:
https://youtu.be/cVhlCzmb-v0
DES Example using Animation:
https://youtu.be/3YBwhWuXZ0o
Strength & Weakness of DES, Avalanche effect in DES:
https://youtu.be/Xy1hver_aaw
Advanced Encryption Standard (AES) Algorithm with structure:
https://youtu.be/X8whYEWoDSI
AES Example using Animation:
https://youtu.be/ZPLEtxxjCYA
Key expansion in AES:
https://youtu.be/14SAn4IEAHk
--------------------------------------------------------------------------------------------------------------
You can always connect with me at:
Follow my blog:
https://www.chiragbhalodia.com
Like my Facebook page:
https://www.facebook.com/chiragbhalodia25
Follow me on Instagram:
https://www.instagram.com/chiragbhalodia.25
Follow me on twitter:
https://twitter.com/chiragsbhalodia
Join telegram group:
https://t.me/chiragbhalodia
Subscribe me on youtube:
https://www.youtube.com/c/ChiragBhalodia
Follow me on Quora:
https://www.quora.com/profile/Chirag-Bhalodia-2
--------------------------------------------------------------------------------------------------------------
Playlist available on my channel:
Network Security (CNS, INS, IS):
https://youtube.com/playlist?list=PLzQqHxFtQGyfiYWaDnasLdy1JPK3JS06o
Computer Network (CN) with animation:
https://youtube.com/playlist?list=PLzQqHxFtQGycfs9Vn8BYy0ic0wh-oL9UC
VFX Animation & Fun Videos:
https://youtube.com/playlist?list=PLzQqHxFtQGyd9esvf-t5XYOKhxQS0tDWx
Comupter Organization & Architecture (COA, CA, CO):
https://youtube.com/playlist?list=PLzQqHxFtQGyd-uDzS9vov8hJfm03X_SzC
Assembly Language Programming:
https://youtube.com/playlist?list=PLzQqHxFtQGyeTa82xQyceYxaf-iyZBICw
Computer Graphics:
https://youtube.com/playlist?list=PLzQqHxFtQGycg_TJBA6uFGDLwbotjs68h
#chirag_bhalodia
#chiragbhalodia
#networksecurity
#cryptography
#AES_Decryption_Example
#AES_Decryption_Process
#AES_Inverse_Transformation_Function
Keep learning, keep supporting 🤝✨💯
How to decrypt data using AES?
AES Decryption Process
AES Decryption Example
How to solve AES decyrption Example
How to Solve AES Inverse Sub Bytes?
How to Solve AES Inverse Shift Rows?
How to Solve AES Inverse Mix Column?
How to Solve AES Inverse Add Round Key?
Follow my blog: https://www.chiragbhalodia.com/2021/09/aes-algorithm.html
In this video, I have explained all inverse transformation fuctions of AES with example (AES decryption process) in this video. Watch carefully. AES Solved example. AES decryption process explain with example.
For decryption, each round consists of the following four steps: Inverse Sub Bytes, Inverse Shift Rows, Inverse Mix Columns, Inverse Add Round Key.
Above steps also called AES inverse transformation function.
AES Inverse Sub BytesTransformation Function:
AES defines a 16 x 16 matrix of byte values, called an inverse S-box, that contains a permutation of all possible 256 8-bit values. These row and column values serve as indexes into the inverse S-box to select a unique 8-bit output value.
AES Inverse Shift RowsTransformation Function:
Rules of Inverse shifting rows,
Row 1 - No Shifting
Row 2 - 1 byte circular right shift
Row 3 - 2 byte circular right shift
Row 4 - 3 byte circular right shift
AES Inverse Mix Column Transformation Function:
AES inverse mix column transformation function is operates on each column individually. Each byte of a column is mapped into a new value that is a function of all four bytes in that column. Here in this function State Array is output of previous transformation function of decryption process.
AES Inverse Add Round Key Transformation Function:
The 128 bits of State are bitwise XORed with the 128 bits of the round key. Inverse add round key proceeds one column at a time.
0:00 Introduction
0:15 Outline
0:45 AES Inverse Sub Bytes (Explain with example)
3:37 AES Inverse Shift Rows (Explain with example)
6:30 AES Inverse Mix Column (Explain with example)
37:25 AES Inverse Add Round Key (Explain with example)
If you like my video contents, please LIKE, COMMENT, SUBSCRIBE & SHARE with your friends.
--------------------------------------------------------------------------------------------------------------
Check out other video on my channel
Block Cipher and Stream Cipher:
https://youtu.be/-gQrm5j0RkQ
Confusion & Diffusion (Frustrated Statistical Analysis or Claud Shannon Properties):
https://youtu.be/PJrW6ZqQipo
Feistel Cipher Structure (to understand DES):
https://youtu.be/emJ0p6h48u4
Data Encryption Standard (DES) Algorithm:
https://youtu.be/cVhlCzmb-v0
DES Example using Animation:
https://youtu.be/3YBwhWuXZ0o
Strength & Weakness of DES, Avalanche effect in DES:
https://youtu.be/Xy1hver_aaw
Advanced Encryption Standard (AES) Algorithm with structure:
https://youtu.be/X8whYEWoDSI
AES Example using Animation:
https://youtu.be/ZPLEtxxjCYA
Key expansion in AES:
https://youtu.be/14SAn4IEAHk
--------------------------------------------------------------------------------------------------------------
You can always connect with me at:
Follow my blog:
https://www.chiragbhalodia.com
Like my Facebook page:
https://www.facebook.com/chiragbhalodia25
Follow me on Instagram:
https://www.instagram.com/chiragbhalodia.25
Follow me on twitter:
https://twitter.com/chiragsbhalodia
Join telegram group:
https://t.me/chiragbhalodia
Subscribe me on youtube:
https://www.youtube.com/c/ChiragBhalodia
Follow me on Quora:
https://www.quora.com/profile/Chirag-Bhalodia-2
--------------------------------------------------------------------------------------------------------------
Playlist available on my channel:
Network Security (CNS, INS, IS):
https://youtube.com/playlist?list=PLzQqHxFtQGyfiYWaDnasLdy1JPK3JS06o
Computer Network (CN) with animation:
https://youtube.com/playlist?list=PLzQqHxFtQGycfs9Vn8BYy0ic0wh-oL9UC
VFX Animation & Fun Videos:
https://youtube.com/playlist?list=PLzQqHxFtQGyd9esvf-t5XYOKhxQS0tDWx
Comupter Organization & Architecture (COA, CA, CO):
https://youtube.com/playlist?list=PLzQqHxFtQGyd-uDzS9vov8hJfm03X_SzC
Assembly Language Programming:
https://youtube.com/playlist?list=PLzQqHxFtQGyeTa82xQyceYxaf-iyZBICw
Computer Graphics:
https://youtube.com/playlist?list=PLzQqHxFtQGycg_TJBA6uFGDLwbotjs68h
#chirag_bhalodia
#chiragbhalodia
#networksecurity
#cryptography
#AES_Decryption_Example
#AES_Decryption_Process
#AES_Inverse_Transformation_Function
Keep learning, keep supporting 🤝✨💯
How to decrypt data using AES?
AES Decryption Process
AES Decryption Example
How to solve AES decyrption Example
How to Solve AES Inverse Sub Bytes?
How to Solve AES Inverse Shift Rows?
How to Solve AES Inverse Mix Column?
How to Solve AES Inverse Add Round Key?
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
25.8K
Likes
286
Duration
42:01
Published
Jun 27, 2022
User Reviews
4.4
(5) Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.