What is ARP protocol? #cyber #cybersecurity #network
Continuing our layer 2 series, what if computer A doesn't know the mac address of computer B? This is why we have ARP protocol! This protocol, stands for add...

CyberWisdom
6.7K views • Aug 24, 2024
About this video
Continuing our layer 2 series, what if computer A doesn't know the mac address of computer B?
This is why we have ARP protocol! This protocol, stands for address resolution protocol, is responsible to get the MAC address of a desired computer.
So how he does it?
He sends in broadcast - I'm computer A, Who is Computer B and what's your MAC address? Then computer B answers - I'm computer B and this is my MAC address!
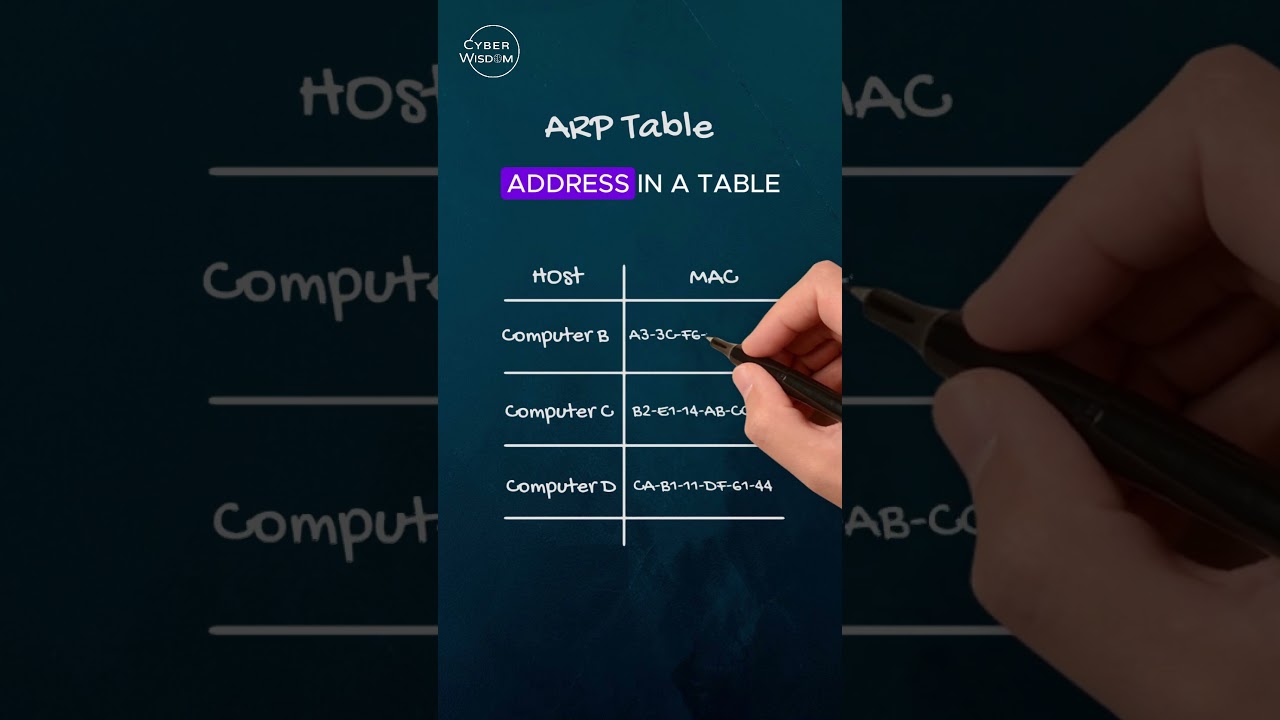
Upon receiving the MAC address of computer B, computer A saves this address in a table called ARP table, so it won't need to ask again.
Open your CMD and run arp dash a, and you will see your computer's arp table.
In the next video we will learn about a technique called ARP poisoning that can be used by attackers.
This is why we have ARP protocol! This protocol, stands for address resolution protocol, is responsible to get the MAC address of a desired computer.
So how he does it?
He sends in broadcast - I'm computer A, Who is Computer B and what's your MAC address? Then computer B answers - I'm computer B and this is my MAC address!
Upon receiving the MAC address of computer B, computer A saves this address in a table called ARP table, so it won't need to ask again.
Open your CMD and run arp dash a, and you will see your computer's arp table.
In the next video we will learn about a technique called ARP poisoning that can be used by attackers.
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
6.7K
Likes
185
Duration
0:58
Published
Aug 24, 2024
User Reviews
4.6
(1) Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.
No specific trending topics match this video yet.
Explore All Trends