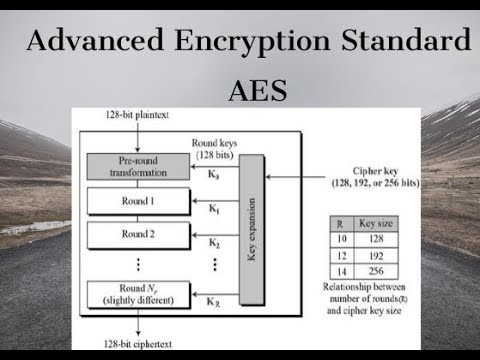
Understanding AES - Advanced Encryption Standard
An explanation of the encryption and decryption processes involved in the Advanced Encryption Standard (AES).

Lectures by Shreedarshan K
4.6K views • Oct 30, 2019
About this video
Explanation of Encryption and Decryption of #AES
--------------------------------------------------------------------------------------------------------------------------
#AdvancedEncryptionStandard #Cryptography #SymmetricCipher #Cipher #AES #AdvancedEncryptionStandard #Encryption and #Decryption #Security #NetworkSecurity
Thanks for watching.
Do like , share and subscribe
------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Blowfish Algorithm : https://youtu.be/qso0bla-cOc
Elliptical Curve Cryptography - 1 : https://youtu.be/_QR-kTypf4E
Brute force Attack : https://youtu.be/W9r80z1cfTk
Avalanche Effect in Cryptography : https://youtu.be/b3zEi4YcEHY
Double & Triple DES : https://youtu.be/SjuZQG89dCA
Steganography / Cryptography Differences: https://youtu.be/MaNk2kMhAQA
Four Square Cipher : https://youtu.be/54YwDWVasXo
Route Cipher : https://youtu.be/a801gnJTbAA
Fiestel Cipher Structure: https://youtu.be/EE297gIlkzQ
Network Security - Attacks : https://youtu.be/8Swn1yj4ccs
Network Security - Authentication using Message Encryption : https://youtu.be/UQbWZvSw4IU
Fiestel Cipher Structure: https://youtu.be/EE297gIlkzQ
Diffie Hellman Key Exchange: https://youtu.be/dloRO4tfE1I
Euler's Totient Function [Euler's Phi Function]:https://youtu.be/h-UVsqZvWng
Fermat's Theorem - Explanation with example: https://youtu.be/cq2vIqyfJAg
s DES - Key Generation : https://youtu.be/mS2VC7vbbNc
Differences between s-DES and DES: https://youtu.be/WGqZTYwG_uU
Primitive Root : https://youtu.be/tngcCcZrezA
-----------------------------------------------------------------------
# To watch lecture videos on Digital Electronics:
https://www.youtube.com/playlist?list=PLzyg4JduvsMqBK7b3UgjeXMHDvlZJoEbN
# To watch lecture videos on 12th Maths:
https://www.youtube.com/playlist?list=PLzyg4JduvsMrt86uef1l_5rTVkPUVjRzO
# To watch lecture videos on 10th Maths:
https://www.youtube.com/playlist?list=PLzyg4JduvsMoke_u9ekH3sSLxJ4LVmbAh
# To watch lecture videos on Vedic Maths:
https://www.youtube.com/playlist?list=PLzyg4JduvsMrT8E4e8ESgLio-x4Gh_Blu
# To watch lecture videos on Cryptography:
https://www.youtube.com/playlist?list=PLzyg4JduvsMoBwwNipMaLBt3E1tGUSkFF
# To watch lecture videos on Information Theory/Coding Theory:
https://www.youtube.com/playlist?list=PLzyg4JduvsMr6B0nu5_n61DFvbo0LuEhI
#To watch lecture videos on Electronics:
https://www.youtube.com/playlist?list=PLzyg4JduvsMrPC_NbIHryZ9gCEz6tz9-r
# To Subscribe:
https://www.youtube.com/channel/UCcwe0u-5wjn8RPGkkDeVzZw?sub_confirmation=1
#To follow my Facebook page : https://www.facebook.com/Lectures-by-Shreedarshan-K-106595060837030/
# Follow Naadopaasana channel - Classical Music, Spiritual discourse channel
https://www.youtube.com/channel/UCNkS1AXwAqIZXhNqrB3Uskw?sub_confirmation=1
# Follow my Blog on Hinduism and Spiritual Significance: https://naadopaasana.co.in/
---------------------------------------------------------------------------------------
Encryption
Decryption
Ciphers
Symmetric Ciphers
Cryptography
Network Security
Polynomials
Primitive root
DES
Data Encryption Standard
Confusion
Diffusion
Hill Cipher
Playfair Cipher
Caesar Cipher
Hill Cipher
Steganography
Triple DES
Meet in the middle attack
Blowfish Algorithm
Eulers Theorem
Chinese Remainder Theorem
IDEA
GCD
Number Theory
Extended Euclidean Algorithm for Modular Inverse
Congruences
RSA Algorithm
Diffie Hellman Key Exchange
ElGamal Cryptosystem
Hash Functions
MAC
Message Authentication Codes
--------------------------------------------------------------------------------------------------------------------------
#AdvancedEncryptionStandard #Cryptography #SymmetricCipher #Cipher #AES #AdvancedEncryptionStandard #Encryption and #Decryption #Security #NetworkSecurity
Thanks for watching.
Do like , share and subscribe
------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Blowfish Algorithm : https://youtu.be/qso0bla-cOc
Elliptical Curve Cryptography - 1 : https://youtu.be/_QR-kTypf4E
Brute force Attack : https://youtu.be/W9r80z1cfTk
Avalanche Effect in Cryptography : https://youtu.be/b3zEi4YcEHY
Double & Triple DES : https://youtu.be/SjuZQG89dCA
Steganography / Cryptography Differences: https://youtu.be/MaNk2kMhAQA
Four Square Cipher : https://youtu.be/54YwDWVasXo
Route Cipher : https://youtu.be/a801gnJTbAA
Fiestel Cipher Structure: https://youtu.be/EE297gIlkzQ
Network Security - Attacks : https://youtu.be/8Swn1yj4ccs
Network Security - Authentication using Message Encryption : https://youtu.be/UQbWZvSw4IU
Fiestel Cipher Structure: https://youtu.be/EE297gIlkzQ
Diffie Hellman Key Exchange: https://youtu.be/dloRO4tfE1I
Euler's Totient Function [Euler's Phi Function]:https://youtu.be/h-UVsqZvWng
Fermat's Theorem - Explanation with example: https://youtu.be/cq2vIqyfJAg
s DES - Key Generation : https://youtu.be/mS2VC7vbbNc
Differences between s-DES and DES: https://youtu.be/WGqZTYwG_uU
Primitive Root : https://youtu.be/tngcCcZrezA
-----------------------------------------------------------------------
# To watch lecture videos on Digital Electronics:
https://www.youtube.com/playlist?list=PLzyg4JduvsMqBK7b3UgjeXMHDvlZJoEbN
# To watch lecture videos on 12th Maths:
https://www.youtube.com/playlist?list=PLzyg4JduvsMrt86uef1l_5rTVkPUVjRzO
# To watch lecture videos on 10th Maths:
https://www.youtube.com/playlist?list=PLzyg4JduvsMoke_u9ekH3sSLxJ4LVmbAh
# To watch lecture videos on Vedic Maths:
https://www.youtube.com/playlist?list=PLzyg4JduvsMrT8E4e8ESgLio-x4Gh_Blu
# To watch lecture videos on Cryptography:
https://www.youtube.com/playlist?list=PLzyg4JduvsMoBwwNipMaLBt3E1tGUSkFF
# To watch lecture videos on Information Theory/Coding Theory:
https://www.youtube.com/playlist?list=PLzyg4JduvsMr6B0nu5_n61DFvbo0LuEhI
#To watch lecture videos on Electronics:
https://www.youtube.com/playlist?list=PLzyg4JduvsMrPC_NbIHryZ9gCEz6tz9-r
# To Subscribe:
https://www.youtube.com/channel/UCcwe0u-5wjn8RPGkkDeVzZw?sub_confirmation=1
#To follow my Facebook page : https://www.facebook.com/Lectures-by-Shreedarshan-K-106595060837030/
# Follow Naadopaasana channel - Classical Music, Spiritual discourse channel
https://www.youtube.com/channel/UCNkS1AXwAqIZXhNqrB3Uskw?sub_confirmation=1
# Follow my Blog on Hinduism and Spiritual Significance: https://naadopaasana.co.in/
---------------------------------------------------------------------------------------
Encryption
Decryption
Ciphers
Symmetric Ciphers
Cryptography
Network Security
Polynomials
Primitive root
DES
Data Encryption Standard
Confusion
Diffusion
Hill Cipher
Playfair Cipher
Caesar Cipher
Hill Cipher
Steganography
Triple DES
Meet in the middle attack
Blowfish Algorithm
Eulers Theorem
Chinese Remainder Theorem
IDEA
GCD
Number Theory
Extended Euclidean Algorithm for Modular Inverse
Congruences
RSA Algorithm
Diffie Hellman Key Exchange
ElGamal Cryptosystem
Hash Functions
MAC
Message Authentication Codes
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
4.6K
Likes
103
Duration
53:11
Published
Oct 30, 2019
User Reviews
4.6
(4) Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.