MACs Explained: HMAC, CBC-MAC & GMAC 🔐
Learn about Message Authentication Codes (MACs), including HMAC, CBC-MAC, and GMAC, to understand how they ensure data integrity and authenticity.

The 3xplainer
233 views • Nov 10, 2025
About this video
In this video, we break down Message Authentication Codes (MACs) — the cryptographic tools that protect data integrity and verify message authenticity in secure communication.
Assess your Knowledge: https://forms.gle/hgYjTJd71usXJe4AA
🔐 What You’ll Learn (Short & Clear):
• What a Message Authentication Code (MAC) is and why it’s symmetric
• How MACs ensure message integrity and authentication
• Why MACs differ from digital signatures (no nonrepudiation)
• The basic process: MAC_k(x) — a message authenticated with a secret key
• How MACs produce a fixed-size tag from variable-length messages
• Real-world MAC constructions:
– HMAC (Hash-based MAC using SHA algorithms)
– CBC-MAC (Built from block ciphers like AES)
– GMAC (High-speed, parallel MAC used in IPsec & TLS)
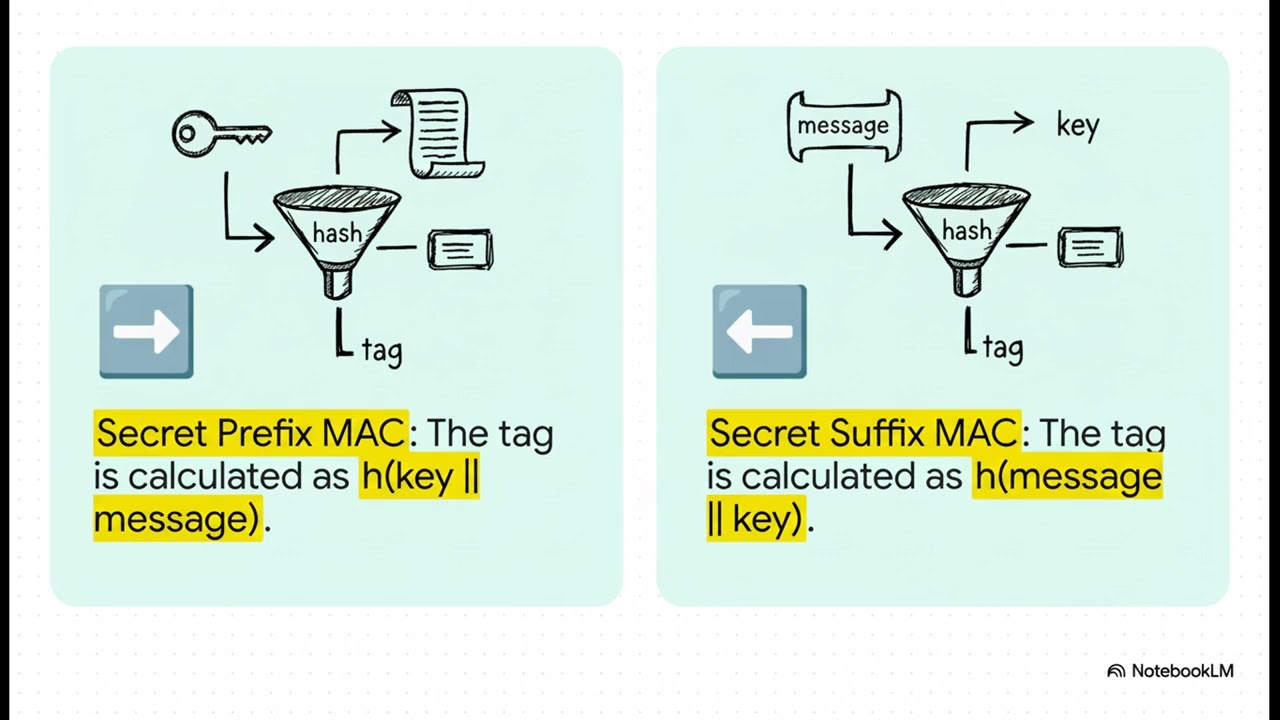
• Why insecure constructions like h(k||x) or h(x||k) are vulnerable
• How HMAC achieves provable security and protects real-world protocols
This video gives you a clear, fast explanation of how MACs act as digital seals — ensuring that a message truly comes from the right source and hasn’t been altered in transit.
✅ Subscribe to The Explainer for more cryptography, cybersecurity, and tech-explainer content!
🔔 Turn on notifications so you never miss a new episode
Assess your Knowledge: https://forms.gle/hgYjTJd71usXJe4AA
🔐 What You’ll Learn (Short & Clear):
• What a Message Authentication Code (MAC) is and why it’s symmetric
• How MACs ensure message integrity and authentication
• Why MACs differ from digital signatures (no nonrepudiation)
• The basic process: MAC_k(x) — a message authenticated with a secret key
• How MACs produce a fixed-size tag from variable-length messages
• Real-world MAC constructions:
– HMAC (Hash-based MAC using SHA algorithms)
– CBC-MAC (Built from block ciphers like AES)
– GMAC (High-speed, parallel MAC used in IPsec & TLS)
• Why insecure constructions like h(k||x) or h(x||k) are vulnerable
• How HMAC achieves provable security and protects real-world protocols
This video gives you a clear, fast explanation of how MACs act as digital seals — ensuring that a message truly comes from the right source and hasn’t been altered in transit.
✅ Subscribe to The Explainer for more cryptography, cybersecurity, and tech-explainer content!
🔔 Turn on notifications so you never miss a new episode
Video Information
Views
233
Likes
5
Duration
6:53
Published
Nov 10, 2025