Mastering Network Security: Asymmetric Cryptography Explained 🔐
Discover the fundamentals of asymmetric encryption, how it differs from symmetric methods, and see practical examples to enhance your understanding of network security.

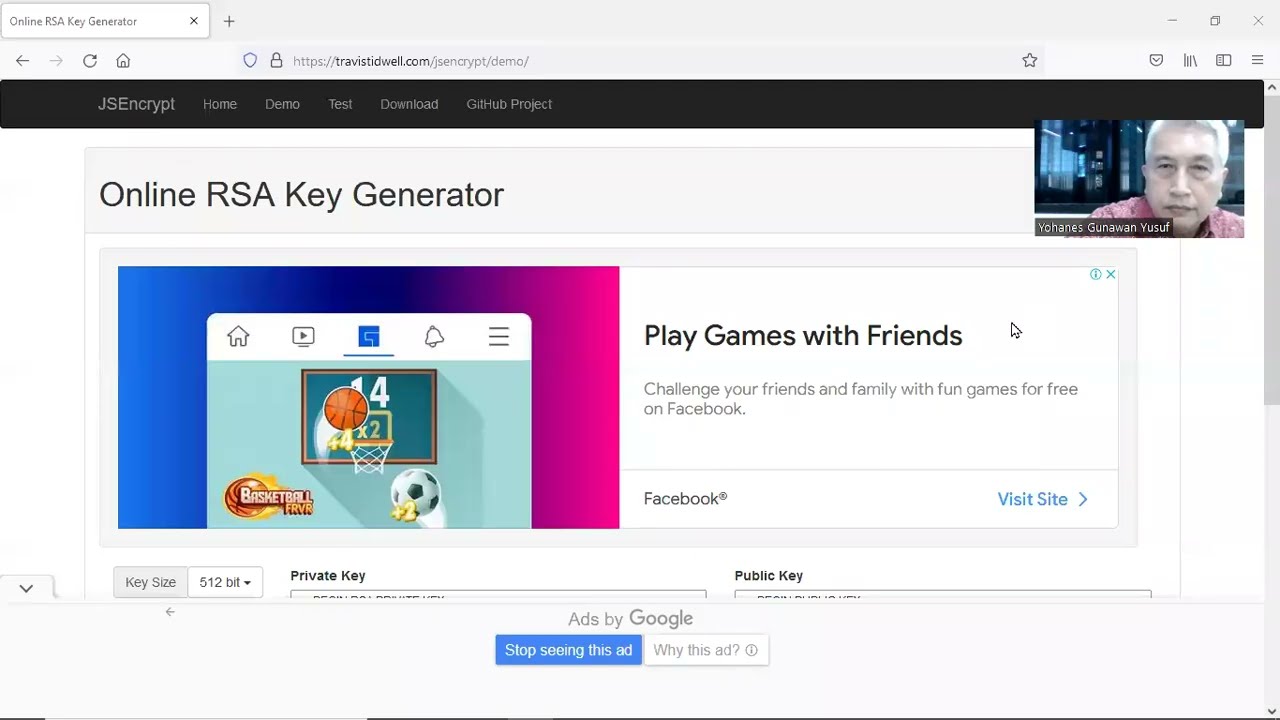
Yohanes Gunawan Yusuf 6111
25 views • May 12, 2022
About this video
Symmetrical encryption is an old and best-known technique. It uses a secret key that can either be a number, a word or a string of random letters. It is a blended with the plain text of a message to change the content in a particular way.
Asymmetrical encryption is also known as public key cryptography, which is a relatively new method, compared to symmetric encryption.
Asymmetric encryption uses two keys to encrypt a plain text. Secret keys are exchanged over the Internet or a large network.
Part 1 - Crypthography dan Keys Terminology
https://youtu.be/LNh5ALtBewo
Part 2 - Asymmetric Keys Samples
https://youtu.be/2U9kgIW0ATw
Part 3 - DIgital Signed, Digital Signature
https://youtu.be/tqaGhMUubcU
Part 4 - Message Digest (MD)
https://youtu.be/1bbB-NJvY1w
Asymmetrical encryption is also known as public key cryptography, which is a relatively new method, compared to symmetric encryption.
Asymmetric encryption uses two keys to encrypt a plain text. Secret keys are exchanged over the Internet or a large network.
Part 1 - Crypthography dan Keys Terminology
https://youtu.be/LNh5ALtBewo
Part 2 - Asymmetric Keys Samples
https://youtu.be/2U9kgIW0ATw
Part 3 - DIgital Signed, Digital Signature
https://youtu.be/tqaGhMUubcU
Part 4 - Message Digest (MD)
https://youtu.be/1bbB-NJvY1w
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
25
Duration
6:48
Published
May 12, 2022
Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.
Trending Now