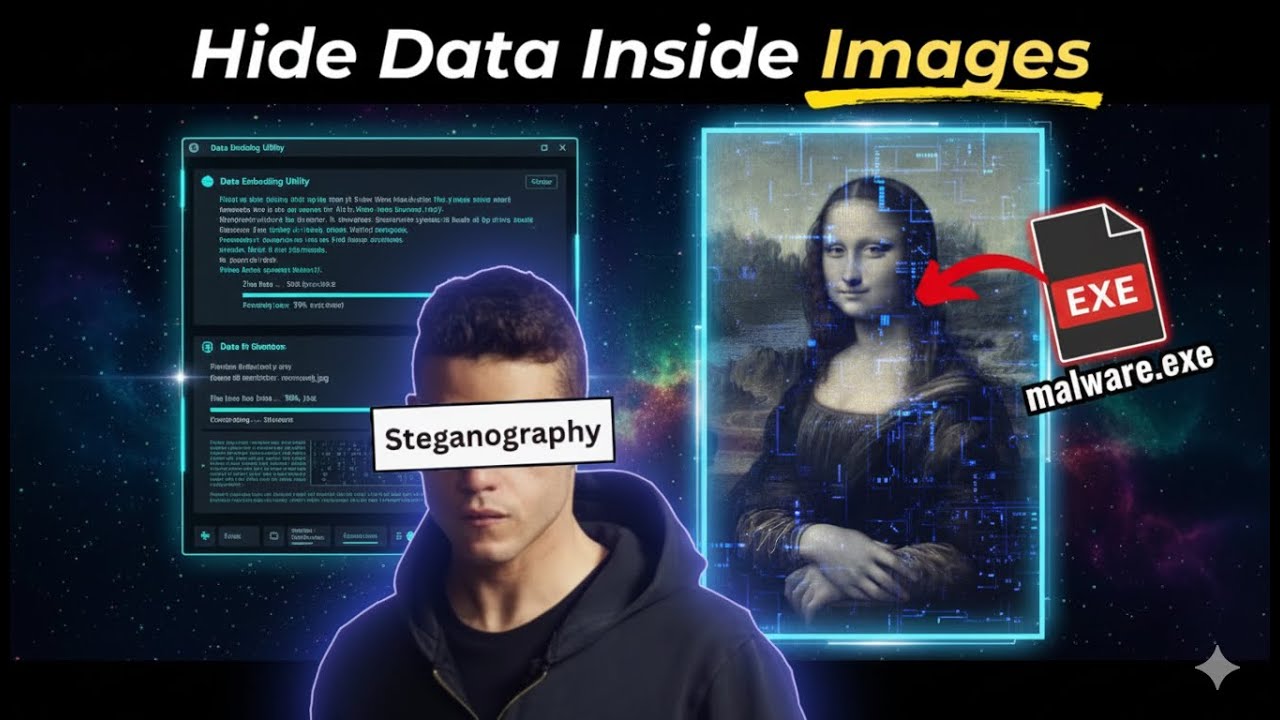
How Hackers Hide Files Inside Images (Steganography Explained)
Ever wondered how files can be hidden inside images without changing how the image looks? In this video, I explain steganography attacks from a cybersecurity...

LinuxGuy | Cyber Security
602 views • Jan 9, 2026
About this video
Ever wondered how files can be hidden inside images without changing how the image looks?
In this video, I explain steganography attacks from a cybersecurity perspective and show a safe, step-by-step demonstration of how data — including executable files — can be embedded and later extracted from image files.
This video is focused on education, awareness, and ethical hacking concepts, helping you understand how steganography works, who uses it, why it’s used, and how defenders detect it.
Using a popular open-source tool called OpenStego, I demonstrate:
How files are hidden inside image files
Why opening the image alone does nothing
How password-protected hidden data is extracted
The difference between data hiding and code execution
Whether you’re a beginner in cybersecurity, an ethical hacker, or someone interested in digital forensics, this video will give you a clear and practical understanding of steganography.
🧠 WHAT YOU’LL LEARN IN THIS VIDEO
What steganography attacks really are
How image steganography works behind the scenes
How files (TXT, EXE, documents) can be hidden inside images
Why attackers use steganography
How ethical hackers and defenders analyze hidden data
The difference between steganography and malware execution
Real-world use cases in cybersecurity and forensics
🛠️ TOOL USED
OpenStego (Open-source steganography tool)
⚠️ EDUCATIONAL DISCLAIMER
This video is created strictly for educational and informational purposes only.
All demonstrations are performed in a controlled environment using harmless example files.
I do not promote or encourage illegal activity, unauthorized access, malware distribution, or misuse of tools.
Always practice ethical hacking responsibly and only on systems or data you own or have explicit permission to use.
👍 SUPPORT THE CHANNEL
If you found this video helpful:
Like the video
Subscribe for more cybersecurity and ethical hacking content
Turn on notifications so you don’t miss future uploads
🔎 KEYWORDS:
steganography, steganography attack, image steganography, hide files in image, hide exe inside image, openstego tutorial, ethical hacking steganography, cybersecurity steganography, data hiding techniques, steganography explained, how hackers hide data, digital forensics steganography, cybersecurity tutorial, information hiding, steganography demo, image based attacks, cyber security education
🏷️ HASHTAGS
#steganography #ethicalhacking #cybersecurity #ImageSteganography #bugbounty #dataprotection #datasecurity #cyberawareness #digitalforensics #infosec #hackingtutorial #dataprivacy #onlinesafety #kalilinux #informationsecurity
In this video, I explain steganography attacks from a cybersecurity perspective and show a safe, step-by-step demonstration of how data — including executable files — can be embedded and later extracted from image files.
This video is focused on education, awareness, and ethical hacking concepts, helping you understand how steganography works, who uses it, why it’s used, and how defenders detect it.
Using a popular open-source tool called OpenStego, I demonstrate:
How files are hidden inside image files
Why opening the image alone does nothing
How password-protected hidden data is extracted
The difference between data hiding and code execution
Whether you’re a beginner in cybersecurity, an ethical hacker, or someone interested in digital forensics, this video will give you a clear and practical understanding of steganography.
🧠 WHAT YOU’LL LEARN IN THIS VIDEO
What steganography attacks really are
How image steganography works behind the scenes
How files (TXT, EXE, documents) can be hidden inside images
Why attackers use steganography
How ethical hackers and defenders analyze hidden data
The difference between steganography and malware execution
Real-world use cases in cybersecurity and forensics
🛠️ TOOL USED
OpenStego (Open-source steganography tool)
⚠️ EDUCATIONAL DISCLAIMER
This video is created strictly for educational and informational purposes only.
All demonstrations are performed in a controlled environment using harmless example files.
I do not promote or encourage illegal activity, unauthorized access, malware distribution, or misuse of tools.
Always practice ethical hacking responsibly and only on systems or data you own or have explicit permission to use.
👍 SUPPORT THE CHANNEL
If you found this video helpful:
Like the video
Subscribe for more cybersecurity and ethical hacking content
Turn on notifications so you don’t miss future uploads
🔎 KEYWORDS:
steganography, steganography attack, image steganography, hide files in image, hide exe inside image, openstego tutorial, ethical hacking steganography, cybersecurity steganography, data hiding techniques, steganography explained, how hackers hide data, digital forensics steganography, cybersecurity tutorial, information hiding, steganography demo, image based attacks, cyber security education
🏷️ HASHTAGS
#steganography #ethicalhacking #cybersecurity #ImageSteganography #bugbounty #dataprotection #datasecurity #cyberawareness #digitalforensics #infosec #hackingtutorial #dataprivacy #onlinesafety #kalilinux #informationsecurity
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
602
Likes
35
Duration
8:16
Published
Jan 9, 2026
Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.
Trending Now