Search Results for "Encapsulation Security Payload"
Find videos related to your search query. Browse through our collection of videos matching "Encapsulation Security Payload". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "Encapsulation Security Payload"
50 results found

0:24
Interview Question: What Is Encapsulation? | #shorts #ytshorts #encapsulation #kiransir
Kiran Academy - Java By Kiran
445.2K views
![PAYLOAD: ICMP Data Exfiltration - USB Rubber Ducky/Exfiltration [PAYLOAD MINUTE]](/image/i.ytimg.com/vi/yGLDZTF7ZaA/hqdefault.jpg)
3:30
PAYLOAD: ICMP Data Exfiltration - USB Rubber Ducky/Exfiltration [PAYLOAD MINUTE]
Hak5
15.1K views
6:57
IP Security Protocol : Encapsulating Security Payload (ESP) Explained in Hindi
5 Minutes Engineering
127.5K views

9:32
Encapsulating Security Payload in Cryptography|| Cryptography and NS || #youtube #videos #cse #btech
Lab Mug
362 views
3:36
what is meant by data encapsulation
sekharonline4u
1 views
5:11
VxLAN | Part 2 - Header Format and Encapsulation
Network Direction
7 views
14:27
OOPS concepts in PHP in Hindi_Urdu (Encapsulation) - Part-3
Talkie Showbz Now
1 views
20:10
Saber on ARM: CCA secure module lattice based key encapsulation on ARM
IACR
327 views

5:42
encapsulation in c++ object oriented programming
Comsianlucky
435 views

22:47
Master OOP in Java: Encapsulation, Abstraction, Polymorphism & Inheritance Explained in 20 Minutes
Engineering Digest
123.9K views

0:57
Java Interview Question | How To Achieve Encapsulation In Java? | #shorts #kiransir #java
Kiran Academy - Java By Kiran
55.9K views

3:31
Can You HIDE a SECRET PAYLOAD in a JPEG Image? - Lec 27
Hack Sphere X
5.9K views
0:06
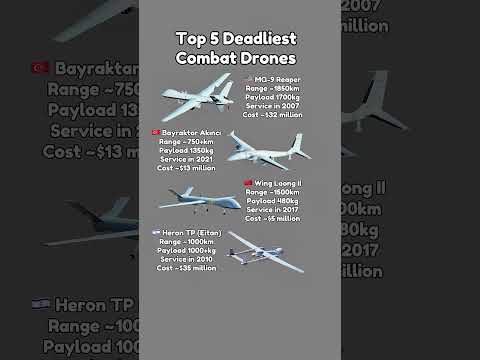
Top 5 Strike Drones Compared: Range, Payload & Cost
The Comparison Zone
669.0K views

3:09
Windows Pentesting Lab Walkthrough: Inject Payload Into Executable
Pentester Academy TV
830 views

13:56
ANDROID 15 HACKED! ⚠️ Metasploit ADVANCED F.U.D PAYLOAD | Google Play Protect & Antivirus DESTROYED!
Mind of a Hacker
57.8K views
4:47
Payload create android using Termux||L0oLzeC||
Ibrahim S
258 views
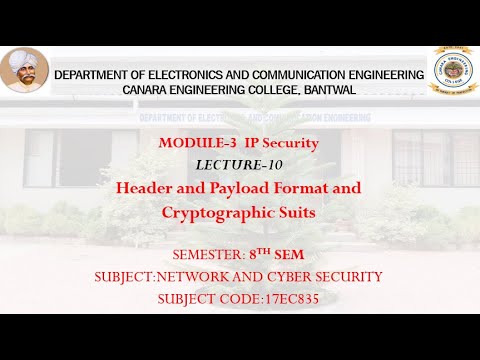
25:53
VTU NCS (17EC835) M3 L10 Header and Payload Format and Cryptographic Suits
Canara Engineering College Mangalore
727 views
5:30
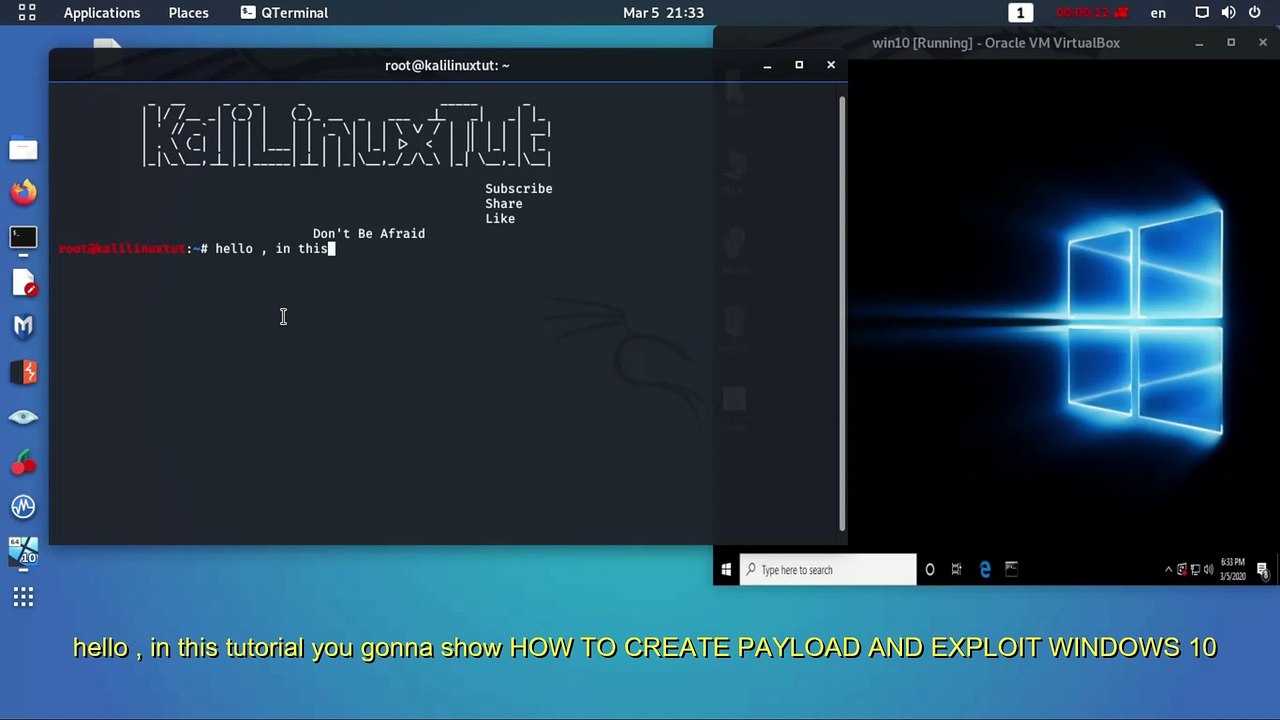
Create Payload And Exploit Windows 10
Mohamed Atwah
59 views
10:02
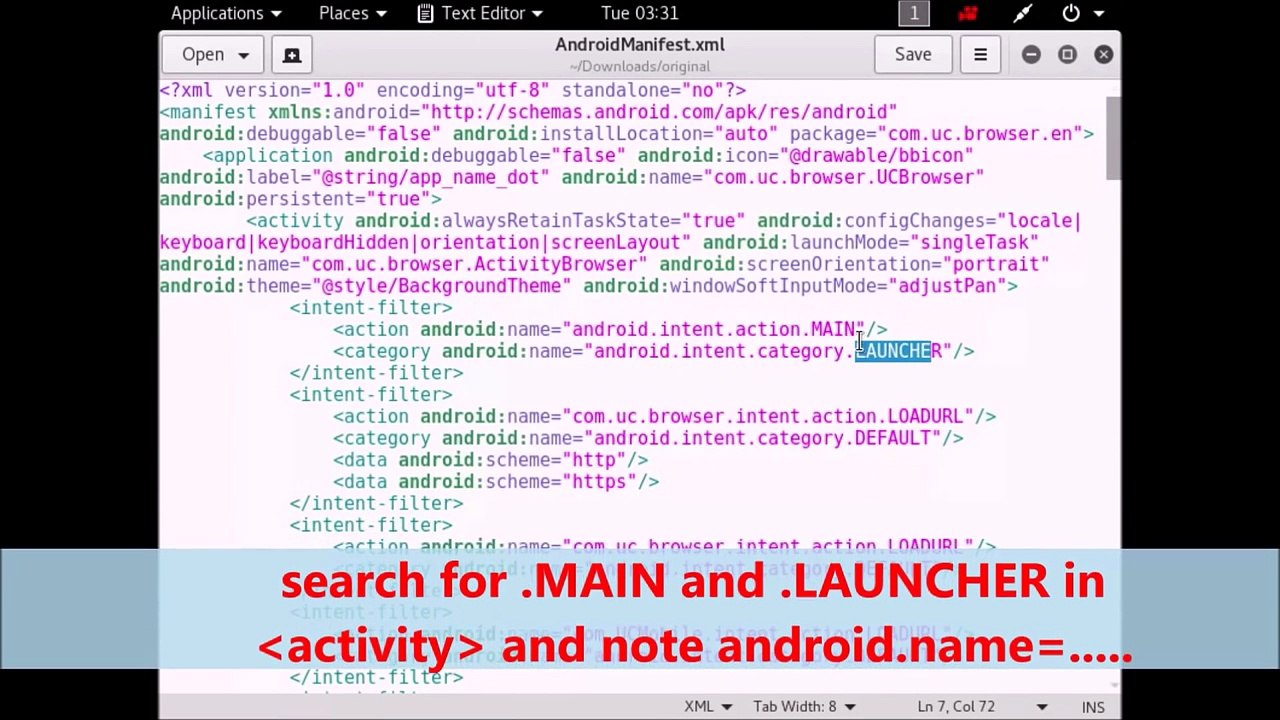
Hack android phone using kali linux (Embed payload in any apk)
Hacking Tutorials
15 views
5:40
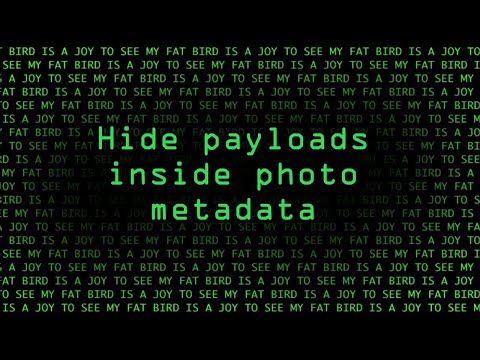
EXIF TOOL - HIDE PAYLOAD IN IMAGE
Guyo Wario
7.4K views

43:57
Air Crash Investigations - Perilous Payload
MediaEntertainment
1.4K views

0:36
mandurah security system, home cctv security systems mandurah, cctv security systems mandurah, mandurah security systems, cctv system mandurah
lockdownse
1 views

8:01
Web Security-Security Threats and their solution in hindi-Security Policy-computer network security
Unbeaten Learning
77.8K views

2:47
IP Security overview, IP Security architecture, Cryptography and Network Security.
Algorithm Pod
488 views

44:53
Networks Security | Security Services | Security Goals | Cryptography | Steganography | Attacks | IA
Bhavishya Coaching SGNR
929 views

1:01:28
Cryptography & Network Security | CH1.2 The OSI Security Architecture & 1.3 Security Attacks
Computer & IT lectures
67 views

7:32
CRYPTOGRAPHY AND NETWORK SECURITY(2) Principles of security, Security Services
Algorithm Pod
143 views

7:07
What Is Cyber Security | How It Works? | Cyber Security In 7 Minutes | Cyber Security | Simplilearn
Simplilearn
4.8M views

18:38
Information Security- Part 3 - Wireless Security, Cryptography, Application/Host Security, and Logs
Russ Esposito
85 views

6:02
Introduction to cryptography and network security|network security|computers security
SCS VAJRA TUTORIALS
35 views

23:56
What Is Network Security? | Introduction To Network Security | Network Security Tutorial|Simplilearn
Simplilearn
124.2K views

12:12
#5 Security Mechanisms In Network Security | Information Security |
Trouble- Free
71.0K views

9:23
MIME protocol in Cryptography and Network Security | Email security in Network Security
Abhishek Sharma
119.7K views

3:42
GuardMe Security - Home Security Systems & Commercial Security Systems
Craig Metzger
5 views

1:55
Retina Network Security Scanner - Conficker Worm Serial - Retina Network Security Scanner - Conficker Wormretina network security scanner conficker worm (2015)
Jose Sanchez
2 views

4:53
Cyber Security in hindi | Cyber security | What is cyber security
hackploit
18 views

5:30
What is security , information security and cyber security
Noor_khan official
3 views

1:00
security system (security system) "security system"
localvideotv
5 views

10:19
#2 Security Approaches and Principles or Goals of Security- Cryptography |Information Security|
Trouble- Free
99.1K views

13:10
Types of security policies, www policy, email security policy, cyber security lecture series
Gaurav Khatri
9.3K views

3:57
Security Mechanisms | Network Security | Cryptography and Network Security
Bikki Mahato
184 views

6:06
Need for Security | Network Security | Cryptography and Network Security
Bikki Mahato
405 views

8:46
Security Mechanisms | Computer Network Security | Information and Cyber Security |Full Course|Lec-04
Abhideep Online Education
11.7K views

14:06
CRYPTOGRAPHY AND NETWORK SECURITY NOTES | NETWORK SECURITY NOTES | NETWORK SECURITY
DIVVELA SRINIVASA RAO
382 views

14:40
SECURITY ATTACKS || TYPES || ACTIVE || PASSIVE || OSI SECURITY ARCHITECTURE --NETWORK SECURITY
t v nagaraju Technical
35.3K views

9:43
Information Security (IS) Vs Cyber Security (CS) || Security Goals
Simple & Effective Learning
735 views

6:02
Network Security Model | Network security model in cryptography | Network Security
Chirag Bhalodia
22.5K views

44:58
Computer Security | What Is Computer Security | Cyber Security Tutorial | Simplilearn
Simplilearn
95.6K views

6:31
Network Security vs Cyber Security | What is Security? | Explained in Hindi
Tech Guru Manjit
16.0K views

3:44
Cyber security क्या है? | What is Cyber Security in Hindi? | Why Cyber Security is Important?
Deepak TechTimes
59.8K views
Page 1