Search Results for "hash function security and reuqirement"
Find videos related to your search query. Browse through our collection of videos matching "hash function security and reuqirement". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "hash function security and reuqirement"
51 results found

14:52
Applications of Hash Function | Purpose of Hash Function | Real Time Application of Hash Function
Chirag Bhalodia
32.1K views
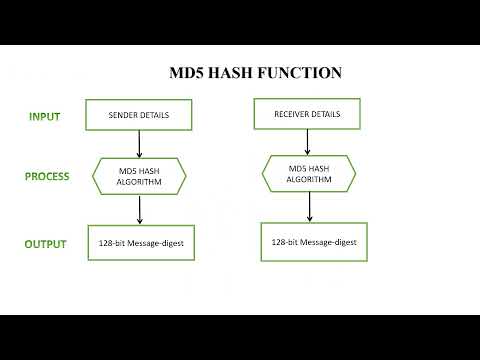
12:00
Hash Function in cryptograhy | Properties of Hash Function | Simple Hash Function Technique
Chirag Bhalodia
107.9K views

9:00
Hash Functions || hash function algorithm || hash function cryptography || hashing vs encryption
The Ecomly Tech
24 views

9:32
Hash function Keya hai? hashing Algorithm? password hashing? password and hash function Hindi
Technical Haroon
8.1K views

10:30
Introduction to HASHING in Data Structures || Hash Functions,Hash Table, Hash Keys,Hash Values in DS
Sundeep Saradhi Kanthety
11.5K views
0:13
Hash Oil,buy Hash oil online,Hash oil for sale,Prefilled hash oil cartridges for sale http://dabstarshop.com
dabstarshop dabstarspharmacy
1 views

7:40
Hash function based on CBC in cryptography | Hash function based on cipher block chaining
Chirag Bhalodia
24.0K views

8:19
LEC11| Blockchain | Cryptographic Hash Function & Properties of Hash Function by Mrs. G. Sowmya
MLID - MLR Institute of Technology
2.3K views
0:09
Function | Definition of function | define function | simple definition of function
Tartull education
23.4K views
11:15
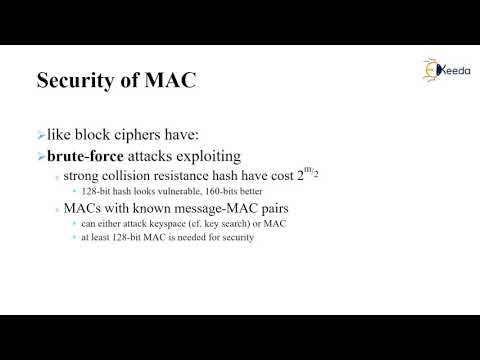
Security of MAC and HASH Function | Cryptography and Network Security
Ekeeda
3.3K views

1:34
Hash Security, Pass-the-Hash, and PKI Explained | Security+ in 60 Seconds
Cyber Buddy
40 views

7:53
Introduction to Hashing|Hashing in Data Strucutures|What is Hashing|Hash Table|Hash function
Scratch Learners
107.6K views
13:39
Introduction to Hashing in Data Structure | Hash Table, Hash Function | DSA using Java #56
ForMyScholars
27.2K views
26:41
What is HASHING ? | Why do we NEED it? | What is a Hash Function | (Example - Array vs Hash Table)
Simple Snippets
9.5K views
13:13
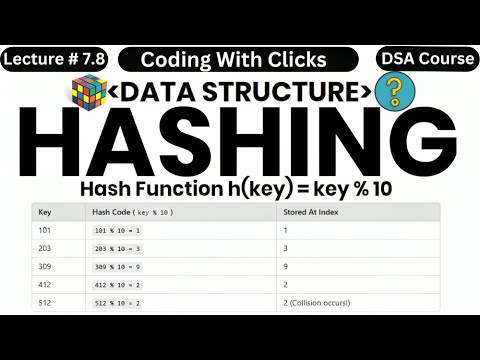
Hashing in Data Structure - Hashing in DSA - Hash Table - Hash Function - Collisions - Load Factor
Coding With Clicks
1.9K views
13:18
Introduction to Cryptographic Hash Function| Merkel Damgard Scheme | SHA-256 | Secure Hash Algorithm
Muhammed Mustaqim
607 views

37:31
Five* non-cryptographic hash functions enter. One hash function leaves.
Linux.conf.au 2016 -- Geelong, Australia
4.7K views

0:13
Euler function of 12 |phi function of 12 #Euler function #group #ringtheory #discretemathematics
Alpha Maths Academy
36.8K views
9:00
HMAC and CMAC in Cryptography Hash Function || Network Security in Telugu
Lab Mug
10.9K views
35:45
Hash Function in Cryptography(Malayalam)/CS 409 Cryptography and Network Security
Renisha's CS Eduworld
2.8K views

26:58
SHA-512 ALGORITHM || SECURE HASH ALGORITHM || CRYPTOGRAPHIC HASH FUNCTIONS || NETWORK SECURITY
t v nagaraju Technical
174.9K views
10:53
PART 4 | HASH FUNCTION ATHENTICATION TECHNIQUE IN CRYPTOGRAPHY & NETWORK SECURITY (BANGLA)
COMPUTER SCIENCE WITH BHASKAR SIR
229 views
5:13
Cryptographic Hash Function (CHF) in Cryptography || Network Security in Telugu
Lab Mug
18.5K views
10:26
Cryptography & Network Security | Meaning | Types | Encryption| Decryption | Hash Function (Hindi)
lets understand stop cramming
84 views
0:11
Hash Function Security: Core Properties
KD Sec n Tech
7 views
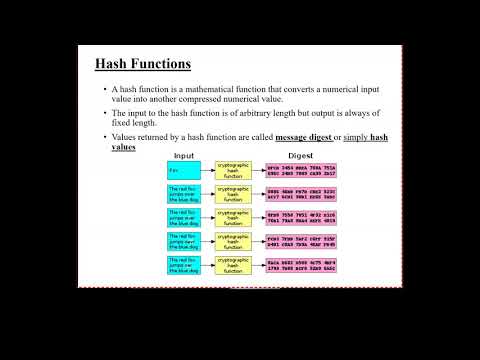
6:08
What is Security requirement of hash function in cryptography
Chirag Bhalodia
25.1K views
7:40
MAC Based on Hash Function | HMAC in network security
Chirag Bhalodia
67.7K views
9:01
Message Authentication Code (MAC) in Cryptography Hash Function || Network Security in Telugu
Lab Mug
14.3K views
5:19
How to make Hash oil with Hash and Aceton (QWACETON) and smoking it.
Carolyne Jeffries
158 views
25:15
Cryptography - Symmetric and Asymmetric key, Hash Function and Digital Signatures
அறிவு பரிணாமம் - Knowledge Evolution
76 views

0:58
Injective, Surjective and Bijective function.|One-One and Onto function.|@vmatics444
V Matics
103.2K views

0:46
What Is Hash Collision and What Does It Mean To Be Resistant To Hash Collisions?
Binance Academy
1.3K views
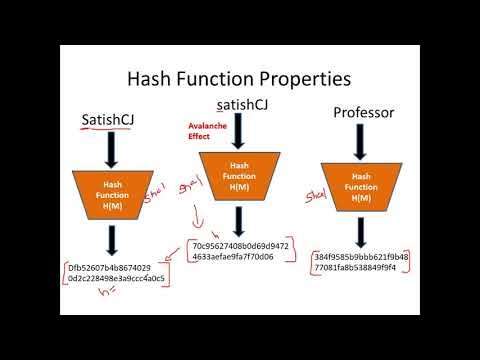
44:53
Introduction to Hash Functions and Application of Hash Functions in Cryptography - CSE4003
Satish C J
24.6K views

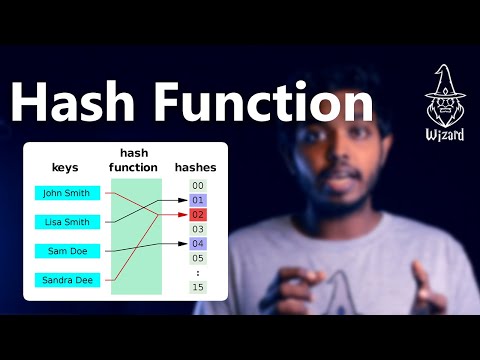
13:56
Hash Tables and Hash Functions
Computer Science Lessons
1.7M views

0:17
What is Hash and what it is used for? |#blockchain #blockchain #Hash #block #BlockchainSeekho
Blockchain Seekho
1.2K views
58:18
How to make hash, hash oil, and marijuana butter
Billman2112
6 views

2:18
BRUSSELS SPROUTS HASH WITH EGGS - brussels sprouts hash and eggs
huong tran
16 views
9:04
Message Digest and Digital Signature | Cryptographic Hash Function
saurabhschool
16.4K views
10:41
Hashing and Hash function explained in SInhala
Wizard LK
13.0K views
32:24
public key encryption: Key distribution, message Authentication and hash function- part1
Dr. Moonther
384 views

8:02
hashing Algorithm? password hashing? password and hash function Hindi
Technical Haroon
21.9K views

8:56
11 Cryptographic Hash Function and its Properties: Pre-image, Second Pre-image, Collision Resistance
Dr Nitin Naik - Aston University, UK
29.5K views

5:11
2. Hash Function and its properties | SHA-256 - Cryptography series
InvolveInInnovation
1.2K views
8:36
107 Secured Communication using hash function and steganography
ICDSMLA 2021
42 views
7:36
Cryptographic Hash Function Explained | How it works? | Properties | Uses and Examples
JXploit
13.8K views
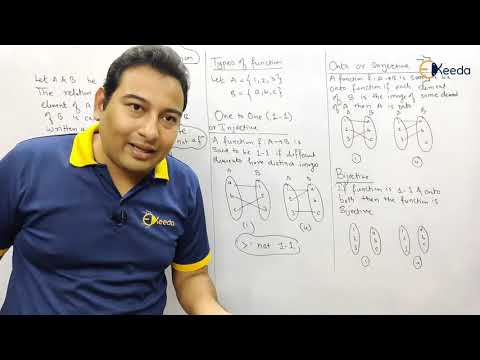
10:55
Introduction to Function and Types of Function - Functions - Discrete Mathematics
Ekeeda
465.8K views

11:33
Zeta function in terms of Gamma function and Bose integral
blackpenredpen
133.8K views
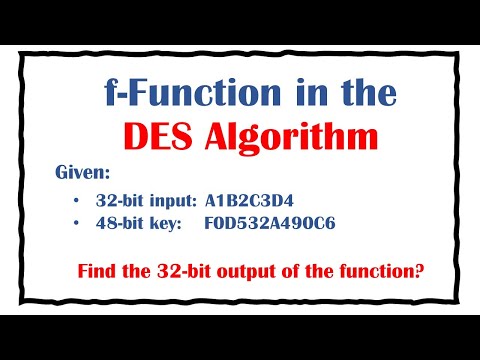
9:15
Find the output of the f-function in DES algorithm, given an input and the key to the function
Susan Zehra
1.5K views
12:14
Cryptography Part 9: F - function and Expansion function in DES
Tech Lover
144 views
13:19
The Xi Function and the Symmetry of the Riemann Zeta Function
Mike, the Mathematician
337 views

0:47
Massive Data Breach Exposes Personal Information of Millions of Comcast Xfinity Subscribers
Benzinga
317 views
Page 1 Next