GPG Usage: Key Generation & Revocation Examples 🔑
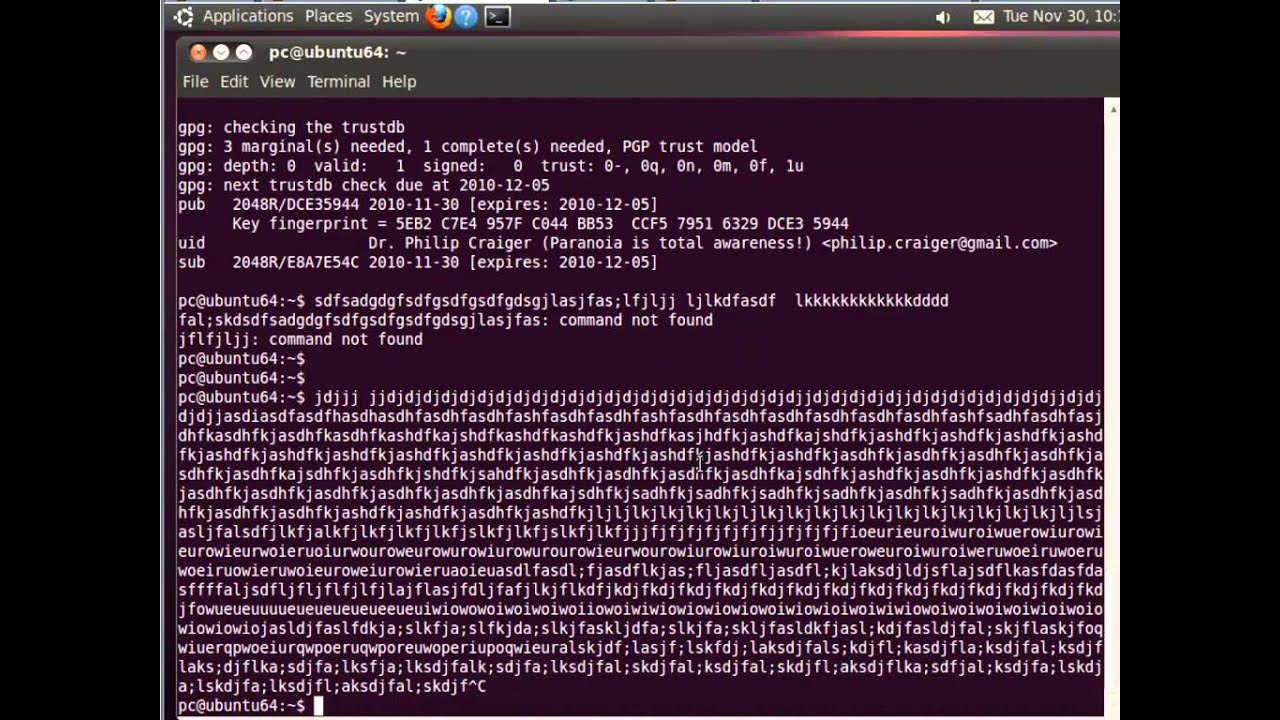
Learn how to generate GPG keys, create revocation certificates, and manage your GPG setup with detailed examples.

Computer and Network Security
91.2K views • Jun 25, 2014
About this video
Summary
Many more examples of GPG usage.
7:09 - Generating a GPG key pair
16:24 - Creating a revocation certificate
18:05 - Outputting revocation certificate to a file
20:01 - Exporting public key (binary file)
20:26 - Using xxd hex viewer to view binary file
21:14 - Exporting public key (ASCII file)
28:09 - Importing a public key
28:51 - Checking fingerprint of public key
Reference Materials
http://www.gnupg.org/documentation/index.en.html - GnuPG Documentation
Many more examples of GPG usage.
7:09 - Generating a GPG key pair
16:24 - Creating a revocation certificate
18:05 - Outputting revocation certificate to a file
20:01 - Exporting public key (binary file)
20:26 - Using xxd hex viewer to view binary file
21:14 - Exporting public key (ASCII file)
28:09 - Importing a public key
28:51 - Checking fingerprint of public key
Reference Materials
http://www.gnupg.org/documentation/index.en.html - GnuPG Documentation
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
91.2K
Likes
965
Duration
30:26
Published
Jun 25, 2014
User Reviews
4.4
(18) Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.
No specific trending topics match this video yet.
Explore All Trends