Using Burp to Exploit XSS Injecting in to Tag Attributes | OWASP Top Ten | Burp suite
In our article "Exploiting XSS - Injecting in to Direct HTML" we started to explore the concept of exploiting XSS in various contexts by identifying the synt...

Technical Security
580 views • Apr 13, 2020
About this video
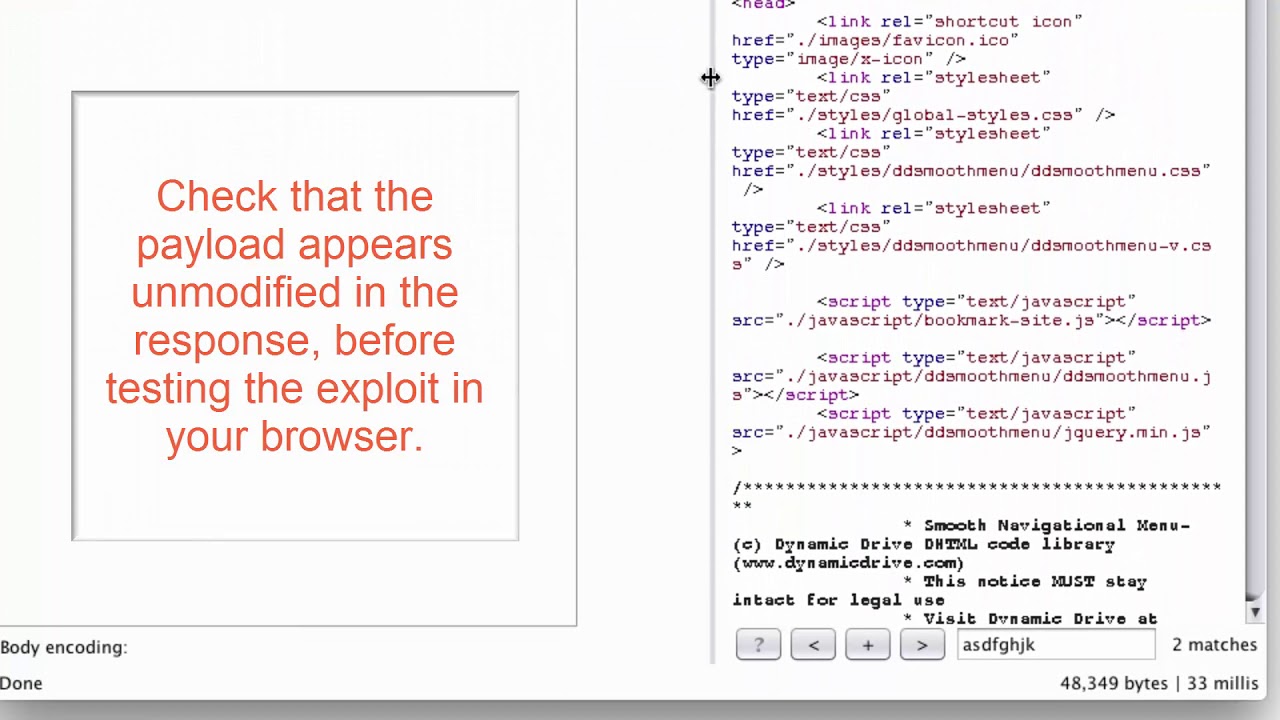
In our article "Exploiting XSS - Injecting in to Direct HTML" we started to explore the concept of exploiting XSS in various contexts by identifying the syntactic context of the response. In this article we demonstrate some methods of modifying your input when injecting in to various Tag Attributes.
By modifying your input appropriately, you can help ensure that the JavaScript included in your payload is executed as intended.
The example uses a version of "Mutillidae" taken from OWASP's Broken Web Application Project.
By modifying your input appropriately, you can help ensure that the JavaScript included in your payload is executed as intended.
The example uses a version of "Mutillidae" taken from OWASP's Broken Web Application Project.
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
580
Likes
4
Duration
3:30
Published
Apr 13, 2020
Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.