Types of Intrusion Detection Systems (IDS)
0:00:00 Overview: Intrusion Detection Systems (IDS) detects any abnormal activity, which is happening on your systems/ network in real-time, in an automated ...

Cyber Security Entertainment
4.4K views • Jul 17, 2019
About this video
0:00:00
Overview:
Intrusion Detection Systems (IDS) detects any abnormal activity, which is happening on your
systems/ network in real-time, in an automated manner.
0:00:51
Types of IDS
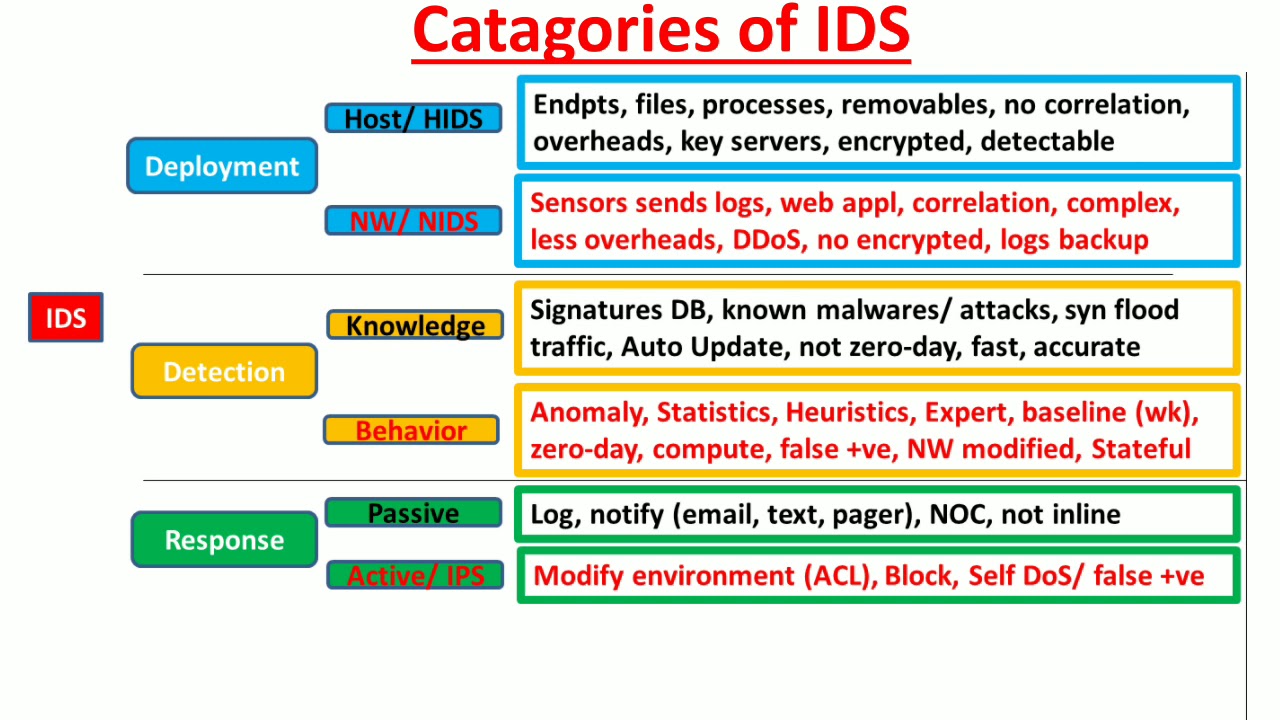
Intrusion detection systems (IDS) classified according to their Deployment position in the network architecture, Detection technology they use and Response they provide to the attacks.
Deployment Types:
According to their deployment, IDS can be deployed at the host/ network and called host-based Intrusion detection systems (HIDS) or network based intrusion systems (NIDS).
Detection Types:
IDS are called knowledge based IDS or behavior based IDS.
Response Types:
According to the Response IDS provide to the attacks, IDS are called as Passive Response IDS / Active Response IDS. Once Active Response IDS is deployed inline with the network traffic then it is called intrusion prevention systems (IPS), because it preemptively prevents/ blocks an attack.
0:02:17
Host based IDS:
0:03:57
Network based IDS (NIDS) uses sensors to collect log data from the network devices e.g. switches and firewalls.
0:06:33
knowledge based IDS;
uses a database of signatures of known malware/ known attacks e.g. Signature for Sync Flood Attack/ Traffic,
0:07:30
Behavior based IDS:
also called Anomaly/ Statistics/ Heuristics/ Expert, because they use a baseline of normal activities which they have gathered over a period of time (e.g. week).
0:09:06
Passive Response IDS:
It does not stop attack, it just logs attack ¬ify admin over email/ text/ pager.
0:09:47
Active Response IDS: actively stops the attack.
0:09:51
intrusion prevention systems (IPS):
There are two kinds of deployments for Active Response IDS, i.e. inline deployment and out of line (mirror traffic). Once deployed inline with traffic, Active Response IDS are known as intrusion prevention systems (IPS), because they can proactively stop or block the attack.
Reference
(ISC)2 CISSP Certified Information Systems Security Professional Official Study Guide 8th Edition: https://www.amazon.com/Certified-Information-Security-Professional-Official/dp/1119475937
Links to Channel's Playlists
Information Security Management: https://www.youtube.com/watch?v=ALRRuAcvEHQ&list=PLOvsYos8og_t8tIMtWHsgHwfpBCoMN5ls
Network Security: https://www.youtube.com/watch?v=YT2GRbokg0w&list=PLOvsYos8og_v6awSuBvvoM_ypoijDCPOi
Information Security Architecture: https://www.youtube.com/watch?v=4o9_22fLQZQ&list=PLOvsYos8og_tNJDrEzNh8q1Z11kx84oWD
Information Security Operations: https://www.youtube.com/watch?v=p5JAXc_4jeY&list=PLOvsYos8og_tDwQDyDnE3kX6WJ64KPMmg
Information Security Testing: https://www.youtube.com/watch?v=XFUP4u9rPng&list=PLOvsYos8og_tPX37LYCwzTngYA8_o31o3
Application Security: https://www.youtube.com/watch?v=wT47-1SJQSE&list=PLOvsYos8og_v6BvX7fAZottTzzB0qh4_h
Cyber Security: https://www.youtube.com/watch?v=YlHPX-gT14k&list=PLOvsYos8og_vUYfYRdk5ULwYSlUwdLaHm
Subscribe to Channel: https://www.youtube.com/channel/UCA88P8LVa18fjOarJkeNVvQ?sub_confirmation=1
Overview:
Intrusion Detection Systems (IDS) detects any abnormal activity, which is happening on your
systems/ network in real-time, in an automated manner.
0:00:51
Types of IDS
Intrusion detection systems (IDS) classified according to their Deployment position in the network architecture, Detection technology they use and Response they provide to the attacks.
Deployment Types:
According to their deployment, IDS can be deployed at the host/ network and called host-based Intrusion detection systems (HIDS) or network based intrusion systems (NIDS).
Detection Types:
IDS are called knowledge based IDS or behavior based IDS.
Response Types:
According to the Response IDS provide to the attacks, IDS are called as Passive Response IDS / Active Response IDS. Once Active Response IDS is deployed inline with the network traffic then it is called intrusion prevention systems (IPS), because it preemptively prevents/ blocks an attack.
0:02:17
Host based IDS:
0:03:57
Network based IDS (NIDS) uses sensors to collect log data from the network devices e.g. switches and firewalls.
0:06:33
knowledge based IDS;
uses a database of signatures of known malware/ known attacks e.g. Signature for Sync Flood Attack/ Traffic,
0:07:30
Behavior based IDS:
also called Anomaly/ Statistics/ Heuristics/ Expert, because they use a baseline of normal activities which they have gathered over a period of time (e.g. week).
0:09:06
Passive Response IDS:
It does not stop attack, it just logs attack ¬ify admin over email/ text/ pager.
0:09:47
Active Response IDS: actively stops the attack.
0:09:51
intrusion prevention systems (IPS):
There are two kinds of deployments for Active Response IDS, i.e. inline deployment and out of line (mirror traffic). Once deployed inline with traffic, Active Response IDS are known as intrusion prevention systems (IPS), because they can proactively stop or block the attack.
Reference
(ISC)2 CISSP Certified Information Systems Security Professional Official Study Guide 8th Edition: https://www.amazon.com/Certified-Information-Security-Professional-Official/dp/1119475937
Links to Channel's Playlists
Information Security Management: https://www.youtube.com/watch?v=ALRRuAcvEHQ&list=PLOvsYos8og_t8tIMtWHsgHwfpBCoMN5ls
Network Security: https://www.youtube.com/watch?v=YT2GRbokg0w&list=PLOvsYos8og_v6awSuBvvoM_ypoijDCPOi
Information Security Architecture: https://www.youtube.com/watch?v=4o9_22fLQZQ&list=PLOvsYos8og_tNJDrEzNh8q1Z11kx84oWD
Information Security Operations: https://www.youtube.com/watch?v=p5JAXc_4jeY&list=PLOvsYos8og_tDwQDyDnE3kX6WJ64KPMmg
Information Security Testing: https://www.youtube.com/watch?v=XFUP4u9rPng&list=PLOvsYos8og_tPX37LYCwzTngYA8_o31o3
Application Security: https://www.youtube.com/watch?v=wT47-1SJQSE&list=PLOvsYos8og_v6BvX7fAZottTzzB0qh4_h
Cyber Security: https://www.youtube.com/watch?v=YlHPX-gT14k&list=PLOvsYos8og_vUYfYRdk5ULwYSlUwdLaHm
Subscribe to Channel: https://www.youtube.com/channel/UCA88P8LVa18fjOarJkeNVvQ?sub_confirmation=1
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
4.4K
Likes
52
Duration
11:09
Published
Jul 17, 2019
User Reviews
4.4
(4) Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.
Trending Now