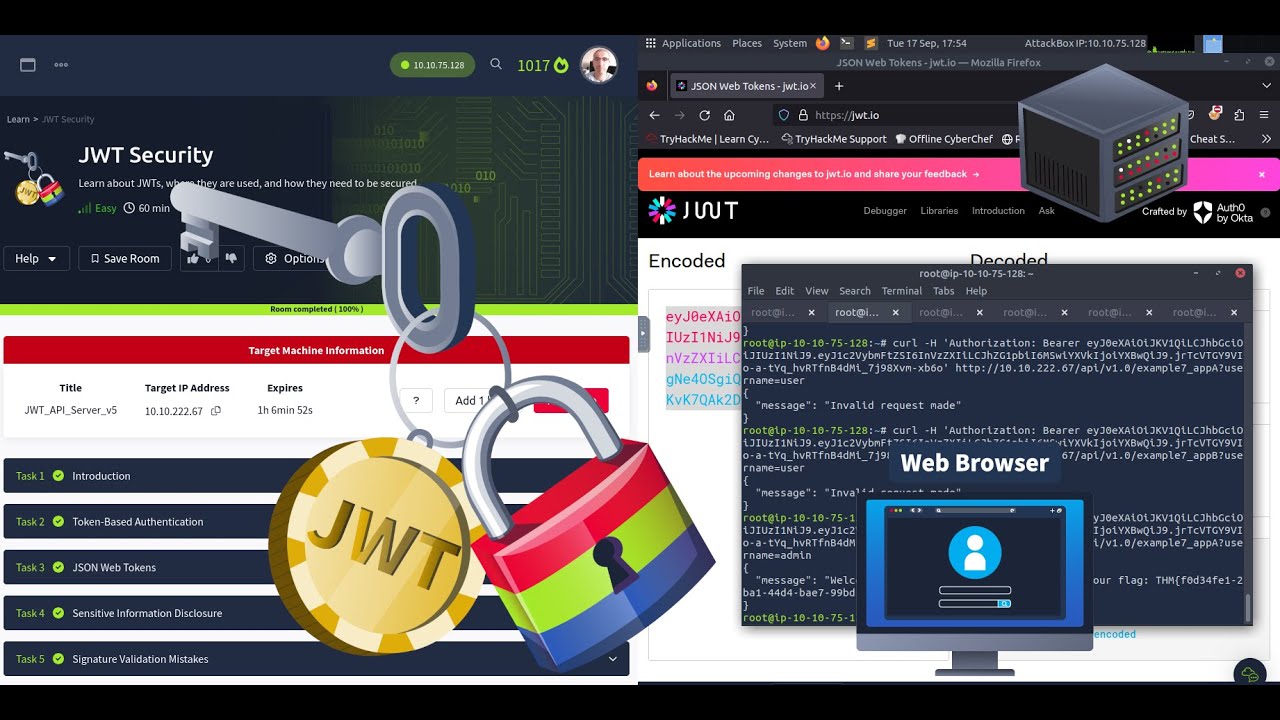
TryHackMe JWT Security - Full Walkthrough | TryHackMe Walkthrough on Token-Based Authentication
Master JWTs & Token Security | TryHackMe Room Guide 🏷️🏷️ Room Link: https://tryhackme.com/r/room/jwtsecurity In this room, you will learn about JSON Web ...

Djalil Ayed
16.5K views • Sep 20, 2024
About this video
Master JWTs & Token Security | TryHackMe Room Guide
🏷️🏷️ Room Link: https://tryhackme.com/r/room/jwtsecurity
In this room, you will learn about JSON Web Tokens (JWTs) and the security associated with them. With the rise of APIs, token-based authentication has become a lot more popular, and of these, JWTs remain one of the most popular implementations. However, with JWTs, ensuring the implementation is done securely is incredibly important. Insecure implementations can lead to serious vulnerabilities, with threat actors having the ability to forge tokens and hijack user sessions!
🚩 Learning Objectives 🚩
🍃 Learn about token-based authentication
🍃 Learn about JSON web tokens (JWTs)
🍃 Learn about why JWTs are popular to use
🍃 Learn about the security considerations when using JWTs
🍃 Learn how to attack vulnerable JWT implementations
🚩 Room Tasks: 🚩
🪙 Task 1: Introduction
🪙 Task 3: Token-Based Authentication
- What is the common header used to transport the JWT in a request?
🪙 Task 4: JSON Web Tokens
- HS256 is an example of what type of signing algorithm?
- RS256 is an example of what type of signing algorithm?
- What is the name used for encrypted JWTs?
🪙 Task 5: Sensitive Information Disclosure
- What is the flag for example 1?
🪙 Task 6: Signature Validation Mistakes
- What is the flag for example 2?
- What is the flag for example 3?
- What is the flag for example 4?
- What is the flag for example 5?
🪙 Task 7: JWT Lifetimes
- What is the flag for example 6?
🪙 Task 8: Cross-Service Relay Attacks
- What is the flag for example 7?
🪙 Task 8: Conclusion
JWT Vulnerabilities & Signature Validation | TryHackMe JWT Security
Securing JSON Web Tokens | JWT Attacks & Fixes | TryHackMe
👍 👍 This content is for educational and authorized penetration testing purposes only. Always ensure you have permission before testing on any systems.
Don't forget to 👍 LIKE and 🔔 SUBSCRIBE for more cybersecurity tutorials!
#tryhackme #JWT #JSONWebTokens #JWTExploit #CyberSecurity #TokenAuthentication #SensitiveInformation #SignatureValidation #InfoSec #EthicalHacking #CaptureTheFlag #JWTAttacks #BugBounty #JWTLifetimes #RelayAttacks
🏷️🏷️ Room Link: https://tryhackme.com/r/room/jwtsecurity
In this room, you will learn about JSON Web Tokens (JWTs) and the security associated with them. With the rise of APIs, token-based authentication has become a lot more popular, and of these, JWTs remain one of the most popular implementations. However, with JWTs, ensuring the implementation is done securely is incredibly important. Insecure implementations can lead to serious vulnerabilities, with threat actors having the ability to forge tokens and hijack user sessions!
🚩 Learning Objectives 🚩
🍃 Learn about token-based authentication
🍃 Learn about JSON web tokens (JWTs)
🍃 Learn about why JWTs are popular to use
🍃 Learn about the security considerations when using JWTs
🍃 Learn how to attack vulnerable JWT implementations
🚩 Room Tasks: 🚩
🪙 Task 1: Introduction
🪙 Task 3: Token-Based Authentication
- What is the common header used to transport the JWT in a request?
🪙 Task 4: JSON Web Tokens
- HS256 is an example of what type of signing algorithm?
- RS256 is an example of what type of signing algorithm?
- What is the name used for encrypted JWTs?
🪙 Task 5: Sensitive Information Disclosure
- What is the flag for example 1?
🪙 Task 6: Signature Validation Mistakes
- What is the flag for example 2?
- What is the flag for example 3?
- What is the flag for example 4?
- What is the flag for example 5?
🪙 Task 7: JWT Lifetimes
- What is the flag for example 6?
🪙 Task 8: Cross-Service Relay Attacks
- What is the flag for example 7?
🪙 Task 8: Conclusion
JWT Vulnerabilities & Signature Validation | TryHackMe JWT Security
Securing JSON Web Tokens | JWT Attacks & Fixes | TryHackMe
👍 👍 This content is for educational and authorized penetration testing purposes only. Always ensure you have permission before testing on any systems.
Don't forget to 👍 LIKE and 🔔 SUBSCRIBE for more cybersecurity tutorials!
#tryhackme #JWT #JSONWebTokens #JWTExploit #CyberSecurity #TokenAuthentication #SensitiveInformation #SignatureValidation #InfoSec #EthicalHacking #CaptureTheFlag #JWTAttacks #BugBounty #JWTLifetimes #RelayAttacks
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
16.5K
Likes
231
Duration
46:05
Published
Sep 20, 2024
User Reviews
4.5
(3) Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.
Trending Now