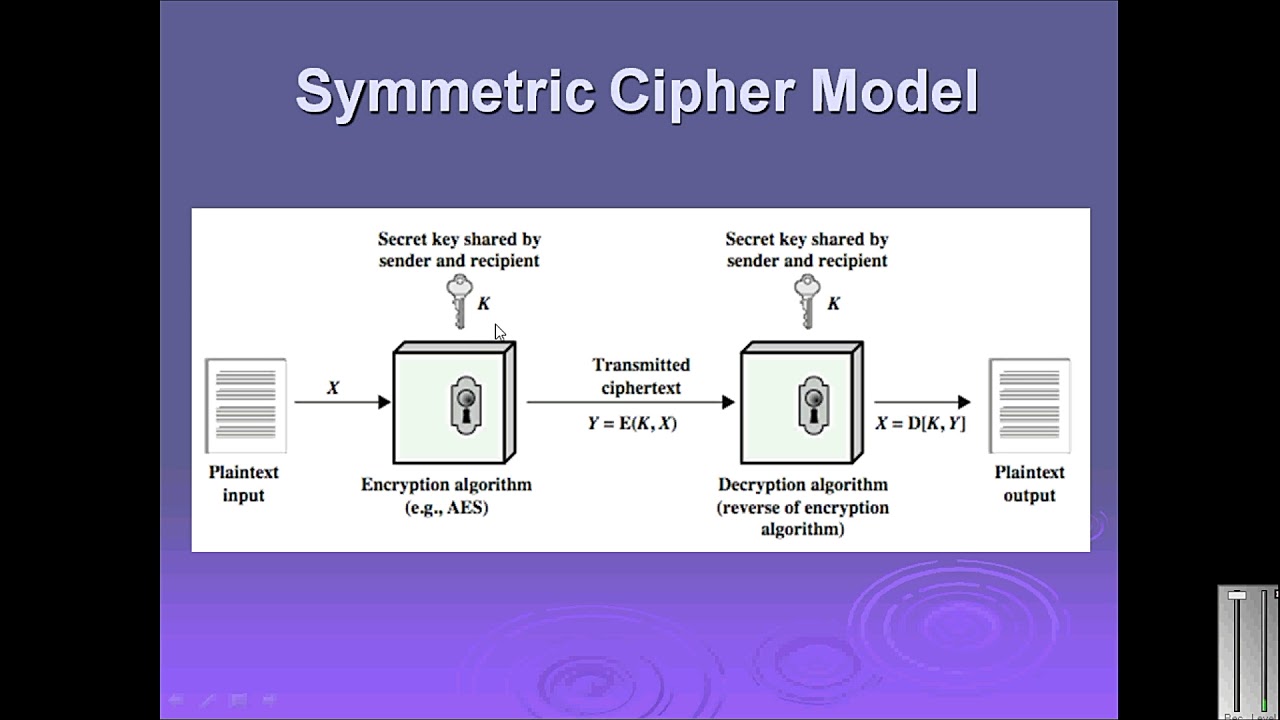
Symmetric Cipher in Cryptography & Network Security 🇵🇸 | Urdu/Hindi | Part 13
Learn about symmetric cipher models in cryptography and network security. This detailed Urdu/Hindi guide covers key concepts and their applications. Watch now!

IT Expert Rai Jazib
458 views • Aug 2, 2018
About this video
Welcome back to our channel
Title:- symmetric cipher || urdu hindi | symmetric cipher model in cryptography and network security }part13
===
Topics Covered in the playlist (Try to Ignore this):
symmetric cipher,symmetric cipher in hindi,symmetric cipher model,symmetric cipher model in hindi,symmetric cipher model in cryptography and network security,symmetric cipher model in cryptography and network security in hindi,symmetric cipher model in network security,symmetric cipher model in network security in hindi,symmetric cipher model in cryptography,symmetric cipher model in cryptography in hindi,symmetric cipher explanation with example in hindi
• Introduction to Network Security, Information security, network security. Computer security, Security Trends, OSI Security Architecture, Security Attacks, Security Services, Security Mechanisms, A model for Network Security
• Symmetric encryption principles, Shift cipher, Rot-13 cipher, Ceasar cipher
• Cryptography, Cryptanalysis techniques,
• Security Threats in Ad-hoc Social Networks,
• Polyalphabetic ciphers, brute force search
• Fiestel cipher structure, Data Encryption Standard
• DES
• DES
• Cipher Block Modes of Operations
• CBM
• Secret key cryptography, key distribution scenario and issues, PRNGs
• Public key cryptography
• Diffie-hellman key agreement, exchange and its security, public key applications
• Quiz # 2
• Mid Term Week
• Mid Term Week
• RSA, Digital signature
RSA security
• Secret sharing, Threshold based SS
• Blakley’s scheme, Entity authentication
• S-MIME
• IP Security Overview, IP Security Policy
• Web Security, Threats and approaches, SSL
• Legal and ethical aspects
• System Security, Intruders, Intrusion Detection, Audit Records, Statistical Anomaly detection
• Rule based intrusion detection, Distributed intrusion detection, honeypots,
• Password management, protection, Strategies to choose password
• Malicious Software’s
• The Need for Firewalls
• Firewall Characteristics
• Types of Firewalls
• Firewall Basing
• Firewall Location and Configurations
Tags:-
#General Knowledge-GK
#EH_BY_IT_Expert_Rai_Jazib
#Birds_Lover
#IT_Expert_Rai_Jazib
#Worlds_color
______________/LINKS\_____________________________
► Facebook:➜ https://www.facebook.com/IT-Expert-Rai-jazib-423950851519009
► Twitter:➜ https://twitter.com/Rai_jazib
► Pinterest:➜ https://www.pinterest.com/raijazib/
► Website:➜ https://itexpertraijazib.blogspot.com/
================================================
Title:- symmetric cipher || urdu hindi | symmetric cipher model in cryptography and network security }part13
===
Topics Covered in the playlist (Try to Ignore this):
symmetric cipher,symmetric cipher in hindi,symmetric cipher model,symmetric cipher model in hindi,symmetric cipher model in cryptography and network security,symmetric cipher model in cryptography and network security in hindi,symmetric cipher model in network security,symmetric cipher model in network security in hindi,symmetric cipher model in cryptography,symmetric cipher model in cryptography in hindi,symmetric cipher explanation with example in hindi
• Introduction to Network Security, Information security, network security. Computer security, Security Trends, OSI Security Architecture, Security Attacks, Security Services, Security Mechanisms, A model for Network Security
• Symmetric encryption principles, Shift cipher, Rot-13 cipher, Ceasar cipher
• Cryptography, Cryptanalysis techniques,
• Security Threats in Ad-hoc Social Networks,
• Polyalphabetic ciphers, brute force search
• Fiestel cipher structure, Data Encryption Standard
• DES
• DES
• Cipher Block Modes of Operations
• CBM
• Secret key cryptography, key distribution scenario and issues, PRNGs
• Public key cryptography
• Diffie-hellman key agreement, exchange and its security, public key applications
• Quiz # 2
• Mid Term Week
• Mid Term Week
• RSA, Digital signature
RSA security
• Secret sharing, Threshold based SS
• Blakley’s scheme, Entity authentication
• S-MIME
• IP Security Overview, IP Security Policy
• Web Security, Threats and approaches, SSL
• Legal and ethical aspects
• System Security, Intruders, Intrusion Detection, Audit Records, Statistical Anomaly detection
• Rule based intrusion detection, Distributed intrusion detection, honeypots,
• Password management, protection, Strategies to choose password
• Malicious Software’s
• The Need for Firewalls
• Firewall Characteristics
• Types of Firewalls
• Firewall Basing
• Firewall Location and Configurations
Tags:-
#General Knowledge-GK
#EH_BY_IT_Expert_Rai_Jazib
#Birds_Lover
#IT_Expert_Rai_Jazib
#Worlds_color
______________/LINKS\_____________________________
► Facebook:➜ https://www.facebook.com/IT-Expert-Rai-jazib-423950851519009
► Twitter:➜ https://twitter.com/Rai_jazib
► Pinterest:➜ https://www.pinterest.com/raijazib/
► Website:➜ https://itexpertraijazib.blogspot.com/
================================================
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
458
Likes
9
Duration
5:48
Published
Aug 2, 2018
Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.
Trending Now