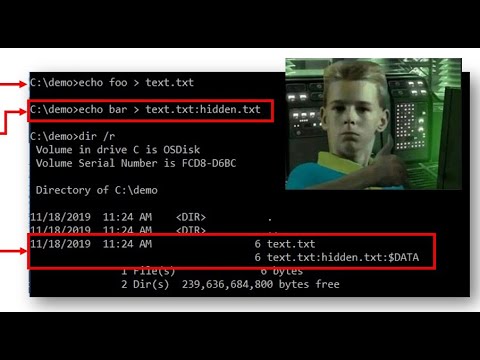
Sneaky Tips with Alternate Data Streams (ADS) 🕵️♂️
Discover how to use ADS to hide code and scripts on Windows and Mac, a secret trick for power users.

Sean
1.6K views • Mar 3, 2021
About this video
Alternate Data Streams are little known to most Windows (and Mac) power users and can easily be leveraged as sneaky places to hide executable code and scripts. Most administrators don’t know about them and most AV’s can’t scan them – especially when hidden in strange places like File System reserved directories!
Links:
https://twitter.com/secure_sean
http://www.exploit-monday.com/2011/09/stealth-alternate-data-streams-and.html
https://redcanary.com/blog/using-alternate-data-streams-bypass-user-account-controls/
https://www.wilderssecurity.com/threads/ntfs-alternate-data-streams-can-be-used-to-bypass-some-path-based-security-checks.377223/
https://www.sciencedirect.com/topics/computer-science/alternate-data-stream
http://tudr.thapar.edu:8080/jspui/bitstream/10266/2810/1/801232019_ruhi.pdf
https://www.google.com/search?q=alternate+data+streams+Service+Hijacking&client=firefox-b-1-d&ei=m-7IXdr1McfU5gL06brwBg&start=10&sa=N&ved=0ahUKEwiar4TXs-HlAhVHqlkKHfS0Dm4Q8NMDCNYB&biw=1536&bih=714
https://www.researchgate.net/publication/250702184_NTFS_Alternate_Data_Streams_focused_hacking
https://cqureacademy.com/blog/alternate-data-streams
https://www.giac.org/paper/gcwn/230/alternate-data-streams-shadows-light/104234
https://www.deepinstinct.com/2018/06/12/the-abuse-of-alternate-data-stream-hasnt-disappeared/
Mentioned Minner running net view https://nakedsecurity.sophos.com/2017/09/21/how-bitpaymer-ransomware-covers-its-tracks/
https://textslashplain.com/2016/04/04/downloads-and-the-mark-of-the-web/
https://textslashplain.com/2016/04/04/downloads-and-the-mark-of-the-web/
https://cyberforensicator.com/2018/06/26/where-did-it-come-from-forensic-analysis-of-zone-identifier/
https://superuser.com/questions/1199464/alternate-data-stream-win32app-1-attached-to-a-large-number-of-folders
https://blogs.technet.microsoft.com/askcore/2013/03/24/alternate-data-streams-in-ntfs/
https://hshrzd.wordpress.com/2016/03/19/introduction-to-ads-alternate-data-streams/
https://cdn2.hubspot.net/hubfs/3354902/Cybereason%20Labs%20Analysis%20Operation%20Cobalt%20Kitty.pdf
https://www.codeproject.com/Articles/2670/Accessing-alternative-data-streams-of-files-on-an
https://github.com/reider-roque/pentest-tools/blob/master/password-cracking/vssown.vbs#L162
https://www.welivesecurity.com/wp-content/uploads/2017/08/eset-gazer.pdf
https://nakedsecurity.sophos.com/2017/09/21/how-bitpaymer-ransomware-covers-its-tracks/
https://attack.mitre.org/techniques/T1096/
https://blog.talosintelligence.com/2017/03/dnsmessenger.html
https://www.symantec.com/security-center/writeup/2005-020216-3537-99
https://www.symantec.com/security-center/writeup/2006-060111-5747-99
https://github.com/k-vitali/Malware-Misc-RE/blob/08ad115274ac3bf66d38cb6e7709ff6a776c1c79/2019-12-20-RunCmdJS-Valak-v6-vk.notes.raw
Empire: lib/modules/powershell/persistence/elevated/registry.py
Links:
https://twitter.com/secure_sean
http://www.exploit-monday.com/2011/09/stealth-alternate-data-streams-and.html
https://redcanary.com/blog/using-alternate-data-streams-bypass-user-account-controls/
https://www.wilderssecurity.com/threads/ntfs-alternate-data-streams-can-be-used-to-bypass-some-path-based-security-checks.377223/
https://www.sciencedirect.com/topics/computer-science/alternate-data-stream
http://tudr.thapar.edu:8080/jspui/bitstream/10266/2810/1/801232019_ruhi.pdf
https://www.google.com/search?q=alternate+data+streams+Service+Hijacking&client=firefox-b-1-d&ei=m-7IXdr1McfU5gL06brwBg&start=10&sa=N&ved=0ahUKEwiar4TXs-HlAhVHqlkKHfS0Dm4Q8NMDCNYB&biw=1536&bih=714
https://www.researchgate.net/publication/250702184_NTFS_Alternate_Data_Streams_focused_hacking
https://cqureacademy.com/blog/alternate-data-streams
https://www.giac.org/paper/gcwn/230/alternate-data-streams-shadows-light/104234
https://www.deepinstinct.com/2018/06/12/the-abuse-of-alternate-data-stream-hasnt-disappeared/
Mentioned Minner running net view https://nakedsecurity.sophos.com/2017/09/21/how-bitpaymer-ransomware-covers-its-tracks/
https://textslashplain.com/2016/04/04/downloads-and-the-mark-of-the-web/
https://textslashplain.com/2016/04/04/downloads-and-the-mark-of-the-web/
https://cyberforensicator.com/2018/06/26/where-did-it-come-from-forensic-analysis-of-zone-identifier/
https://superuser.com/questions/1199464/alternate-data-stream-win32app-1-attached-to-a-large-number-of-folders
https://blogs.technet.microsoft.com/askcore/2013/03/24/alternate-data-streams-in-ntfs/
https://hshrzd.wordpress.com/2016/03/19/introduction-to-ads-alternate-data-streams/
https://cdn2.hubspot.net/hubfs/3354902/Cybereason%20Labs%20Analysis%20Operation%20Cobalt%20Kitty.pdf
https://www.codeproject.com/Articles/2670/Accessing-alternative-data-streams-of-files-on-an
https://github.com/reider-roque/pentest-tools/blob/master/password-cracking/vssown.vbs#L162
https://www.welivesecurity.com/wp-content/uploads/2017/08/eset-gazer.pdf
https://nakedsecurity.sophos.com/2017/09/21/how-bitpaymer-ransomware-covers-its-tracks/
https://attack.mitre.org/techniques/T1096/
https://blog.talosintelligence.com/2017/03/dnsmessenger.html
https://www.symantec.com/security-center/writeup/2005-020216-3537-99
https://www.symantec.com/security-center/writeup/2006-060111-5747-99
https://github.com/k-vitali/Malware-Misc-RE/blob/08ad115274ac3bf66d38cb6e7709ff6a776c1c79/2019-12-20-RunCmdJS-Valak-v6-vk.notes.raw
Empire: lib/modules/powershell/persistence/elevated/registry.py
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
1.6K
Likes
40
Duration
31:49
Published
Mar 3, 2021
User Reviews
4.5
(1) Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.
No specific trending topics match this video yet.
Explore All Trends