SHA Family: SHA-1, SHA-2 & SHA-3 Explained
Learn the differences between SHA-1, SHA-2, and SHA-3, key cryptographic hash functions used worldwide 🔐.

Lexorithm
31 views • Feb 13, 2026
About this video
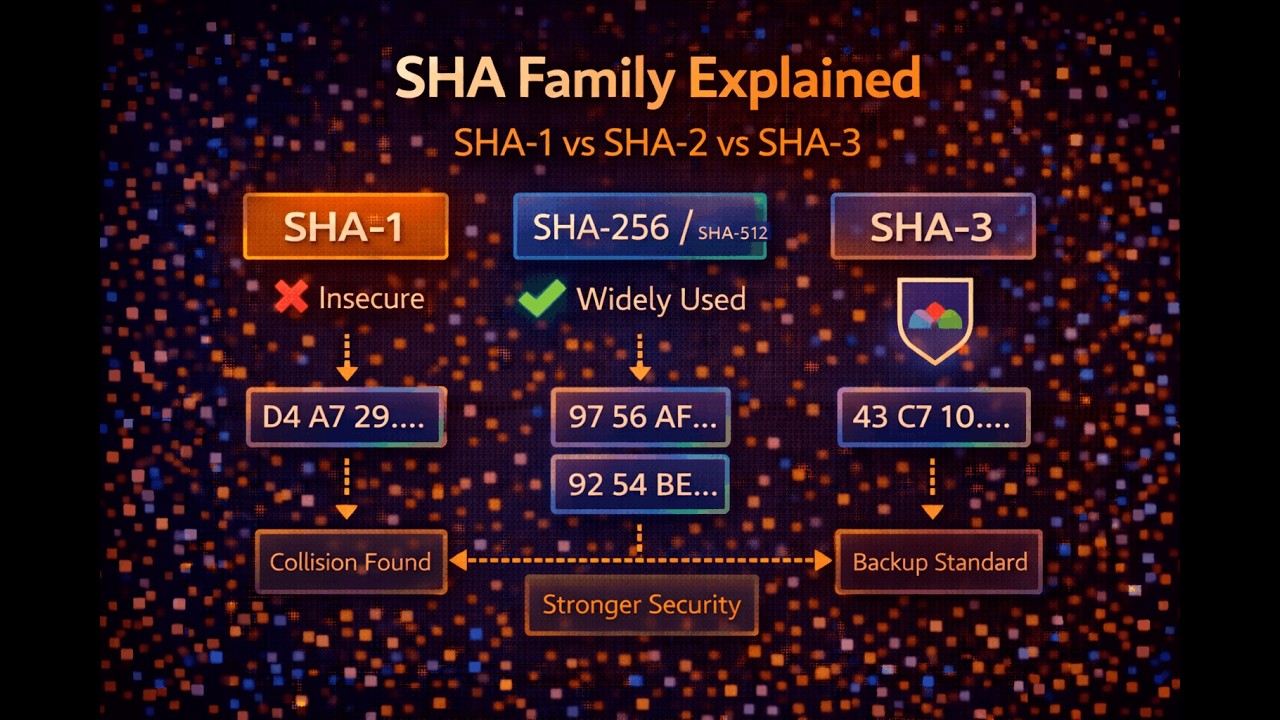
The SHA (Secure Hash Algorithm) family is one of the most widely used cryptographic hash standards in the world.
But what is the difference between SHA-1, SHA-2, and SHA-3?
In this video, we explain:
What SHA stands for
Why SHA-1 is no longer considered secure
Why SHA-256 (SHA-2) is widely used today
Why SHA-3 was introduced as an alternative design
You will understand how hash standards evolve over time and why cryptography must adapt to increasing computational power and new attack techniques.
This explanation focuses on conceptual clarity and comparison, without diving into internal compression functions or mathematical details.
📌 Previous video: Properties of Secure Hash Functions
📌 Next video: Message Authentication Codes (MACs)
But what is the difference between SHA-1, SHA-2, and SHA-3?
In this video, we explain:
What SHA stands for
Why SHA-1 is no longer considered secure
Why SHA-256 (SHA-2) is widely used today
Why SHA-3 was introduced as an alternative design
You will understand how hash standards evolve over time and why cryptography must adapt to increasing computational power and new attack techniques.
This explanation focuses on conceptual clarity and comparison, without diving into internal compression functions or mathematical details.
📌 Previous video: Properties of Secure Hash Functions
📌 Next video: Message Authentication Codes (MACs)
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
31
Likes
1
Duration
5:23
Published
Feb 13, 2026
Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.
No specific trending topics match this video yet.
Explore All Trends