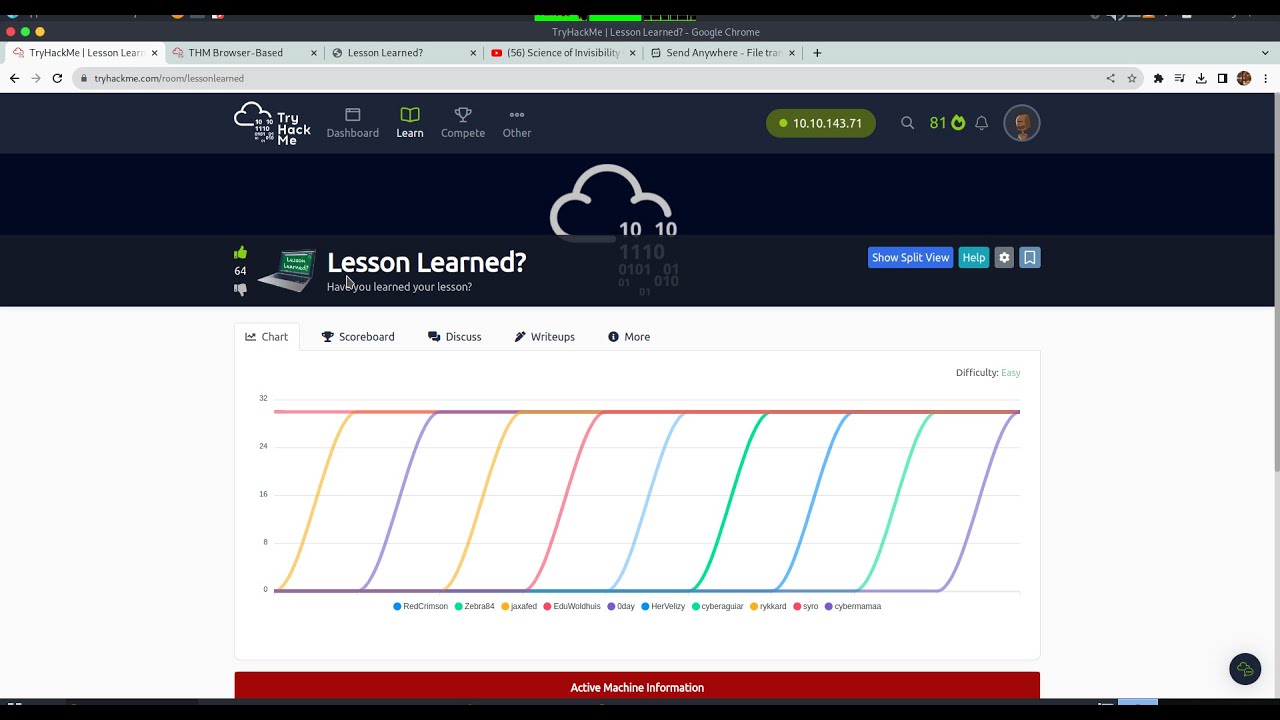
TryHackMe Lesson Learned Walkthrough 🔐
Step-by-step guide to solving the 'Lesson Learned' machine on TryHackMe, demonstrating easy penetration testing techniques.

Cybershield
403 views • Aug 27, 2023
About this video
Overview:
In this video, I'll guide you through the process of solving the "Lesson Learned" machine from TryHackMe. The machine presents us with a login page and a challenge to find the flag hidden beyond it. We'll treat this exercise as a real-world scenario and use ethical hacking techniques to bypass the login screen. Our main focus will be on utilizing SQL injection to exploit vulnerabilities and gain unauthorized access. I'll provide step-by-step instructions on how to perform the attack, explaining each concept along the way.
Goals:
Understand the importance of treating CTF challenges as real-world scenarios.
Learn the basics of SQL injection and its potential impact on web applications.
Gain hands-on experience in identifying and exploiting vulnerabilities in a controlled environment.
Successfully bypass the login screen of the "Lesson Learned" machine and retrieve the hidden flag.
Build confidence in your ethical hacking skills and problem-solving abilities.
What You'll Learn:
By the end of this video, you'll have learned how to:
Approach CTF challenges with a real-world mindset.
Identify and exploit SQL injection vulnerabilities.
Craft malicious input to manipulate web application behavior.
Extract sensitive information from a compromised system.
Apply ethical hacking techniques in a controlled and responsible manner.
In this video, I'll guide you through the process of solving the "Lesson Learned" machine from TryHackMe. The machine presents us with a login page and a challenge to find the flag hidden beyond it. We'll treat this exercise as a real-world scenario and use ethical hacking techniques to bypass the login screen. Our main focus will be on utilizing SQL injection to exploit vulnerabilities and gain unauthorized access. I'll provide step-by-step instructions on how to perform the attack, explaining each concept along the way.
Goals:
Understand the importance of treating CTF challenges as real-world scenarios.
Learn the basics of SQL injection and its potential impact on web applications.
Gain hands-on experience in identifying and exploiting vulnerabilities in a controlled environment.
Successfully bypass the login screen of the "Lesson Learned" machine and retrieve the hidden flag.
Build confidence in your ethical hacking skills and problem-solving abilities.
What You'll Learn:
By the end of this video, you'll have learned how to:
Approach CTF challenges with a real-world mindset.
Identify and exploit SQL injection vulnerabilities.
Craft malicious input to manipulate web application behavior.
Extract sensitive information from a compromised system.
Apply ethical hacking techniques in a controlled and responsible manner.
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
403
Likes
5
Duration
7:55
Published
Aug 27, 2023
Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.
No specific trending topics match this video yet.
Explore All Trends