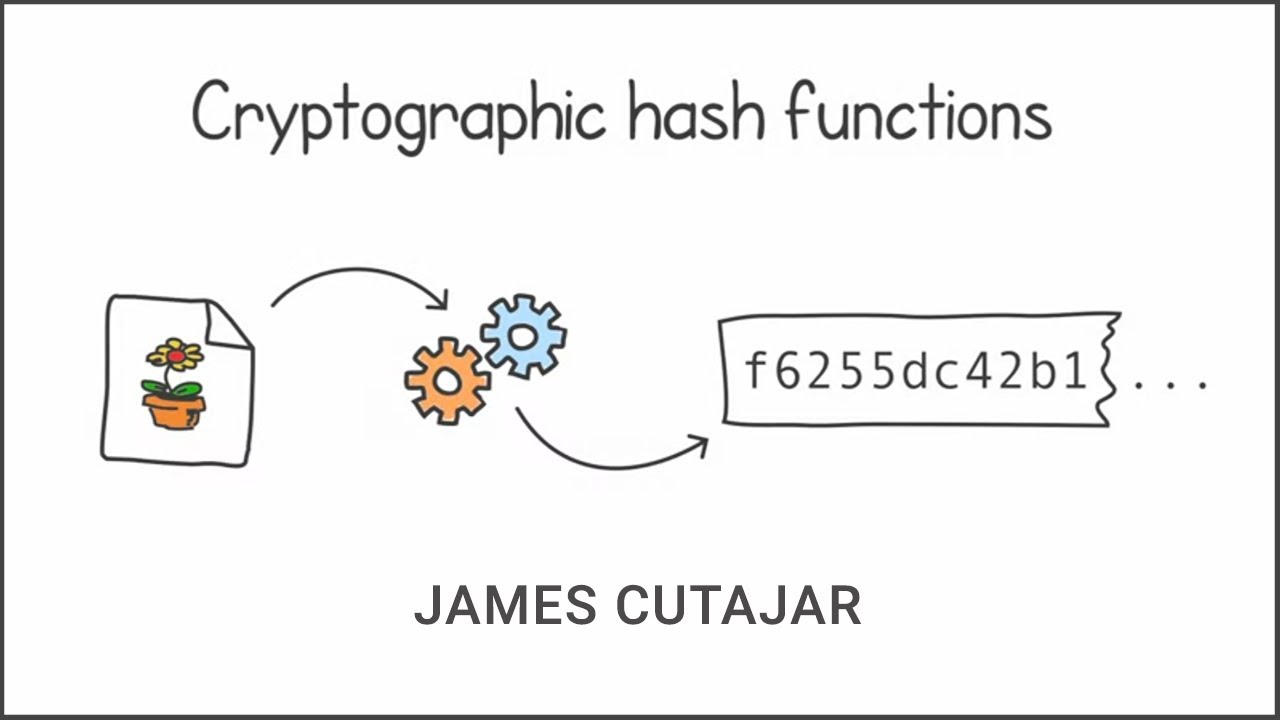
Impress your friends with Cryptographic Hashing!
Cryptographic hashing functions, such as sha-2 are used in many applications in Cryptography. In this video, James Cutajar of Learn Concurrent Programming wi...

Manning Publications
434 views • Oct 11, 2023
About this video
Cryptographic hashing functions, such as sha-2 are used in many applications in Cryptography. In this video, James Cutajar of Learn Concurrent Programming with Go gives an introduction to what they do and how they work.
Support James by purchasing Real-World Cryptography by David Wong using the link: http://mng.bz/lVRy
Follow James on social media:
LinkedIn: https://www.linkedin.com/in/cutajar/
Twitter: https://twitter.com/cutajarj
GitHub: https://github.com/cutajarj
YouTube: https://www.youtube.com/@jamescutajar
You can also purchase any booking from Manning.com using promo code au35cut (35% off) and this link: http://mng.bz/j1y9
Support James by purchasing Real-World Cryptography by David Wong using the link: http://mng.bz/lVRy
Follow James on social media:
LinkedIn: https://www.linkedin.com/in/cutajar/
Twitter: https://twitter.com/cutajarj
GitHub: https://github.com/cutajarj
YouTube: https://www.youtube.com/@jamescutajar
You can also purchase any booking from Manning.com using promo code au35cut (35% off) and this link: http://mng.bz/j1y9
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
434
Likes
23
Duration
7:27
Published
Oct 11, 2023
Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.