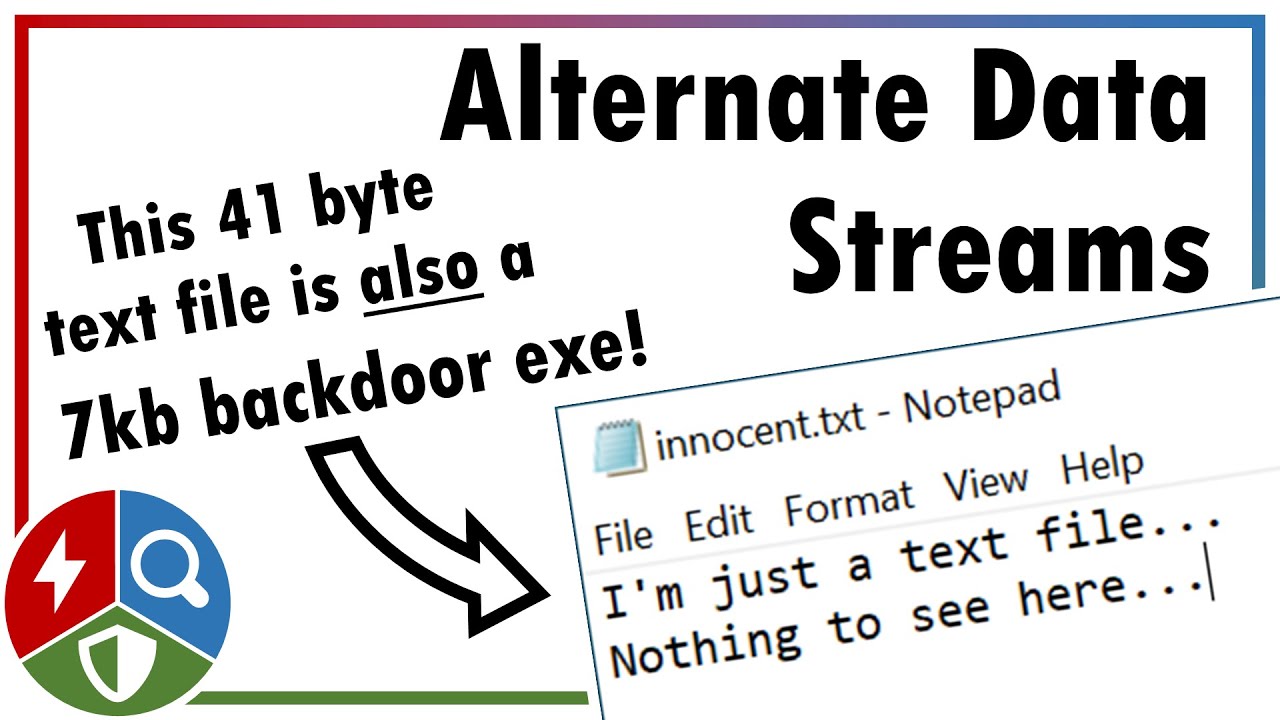
Hiding Data Using NTFS Alternate Data Streams (Defence Evasion)
In this video we'll be exploring how to attack, detect and defend against the abuse of NTFS alternate data streams. Originally designed for interoperability,...

Attack Detect Defend (rot169)
12.8K views • Jul 7, 2020
About this video
In this video we'll be exploring how to attack, detect and defend against the abuse of NTFS alternate data streams. Originally designed for interoperability, this feature has been commandeered by attackers to hide data and malware in otherwise benign files.
If you find the video useful please do give it a like, and consider subscribing if you want more of this sort of content. Drop a note in the comments if there’s anything you think I missed, or if you have a good idea of what topic I should cover next.
Further reading/watching:
Mitre ATT&CK on NTFS Alternate Data Streams: https://attack.mitre.org/techniques/T1564/004/
NTFS documentation by Richard Russon and Yuval Fledel: http://dubeyko.com/development/FileSystems/NTFS/ntfsdoc.pdf
Microsoft documentation about Zones: https://docs.microsoft.com/en-us/previous-versions/windows/internet-explorer/ie-developer/platform-apis/ms537183(v=vs.85)
Sean Pierce on “Sneaky Tips and Tricks with Alternate Data Streams”: https://www.sans.org/cyber-security-summit/archives/file/summit-archive-1574190235.pdf
Sysinternals Sysmon tool: https://docs.microsoft.com/en-us/sysinternals/downloads/sysmon
Audio Credits (licensed under CC0):
Intro/Outro Music by Flavio Concini (https://freesound.org/people/Greek555/)
Transition audio: "Ethereal Woosh" by Newagesoup (https://freesound.org/people/newagesoup/)
Timestamps:
0:00 Intro
2:16 Attack
3:46 Detect
5:25 Defend
If you find the video useful please do give it a like, and consider subscribing if you want more of this sort of content. Drop a note in the comments if there’s anything you think I missed, or if you have a good idea of what topic I should cover next.
Further reading/watching:
Mitre ATT&CK on NTFS Alternate Data Streams: https://attack.mitre.org/techniques/T1564/004/
NTFS documentation by Richard Russon and Yuval Fledel: http://dubeyko.com/development/FileSystems/NTFS/ntfsdoc.pdf
Microsoft documentation about Zones: https://docs.microsoft.com/en-us/previous-versions/windows/internet-explorer/ie-developer/platform-apis/ms537183(v=vs.85)
Sean Pierce on “Sneaky Tips and Tricks with Alternate Data Streams”: https://www.sans.org/cyber-security-summit/archives/file/summit-archive-1574190235.pdf
Sysinternals Sysmon tool: https://docs.microsoft.com/en-us/sysinternals/downloads/sysmon
Audio Credits (licensed under CC0):
Intro/Outro Music by Flavio Concini (https://freesound.org/people/Greek555/)
Transition audio: "Ethereal Woosh" by Newagesoup (https://freesound.org/people/newagesoup/)
Timestamps:
0:00 Intro
2:16 Attack
3:46 Detect
5:25 Defend
Video Information
Views
12.8K
Likes
425
Duration
6:30
Published
Jul 7, 2020
User Reviews
4.6
(2) Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.
Trending Now