ECC Explained: How Public Keys Are Secure, Generated, and Used for Encryption 🔐
Discover the fundamentals of Elliptic Curve Cryptography (ECC): why public keys are secure, how they are generated, and the encryption process. Explore practical demos for a clearer understanding!

Bill Buchanan OBE
1.1K views • Mar 5, 2020
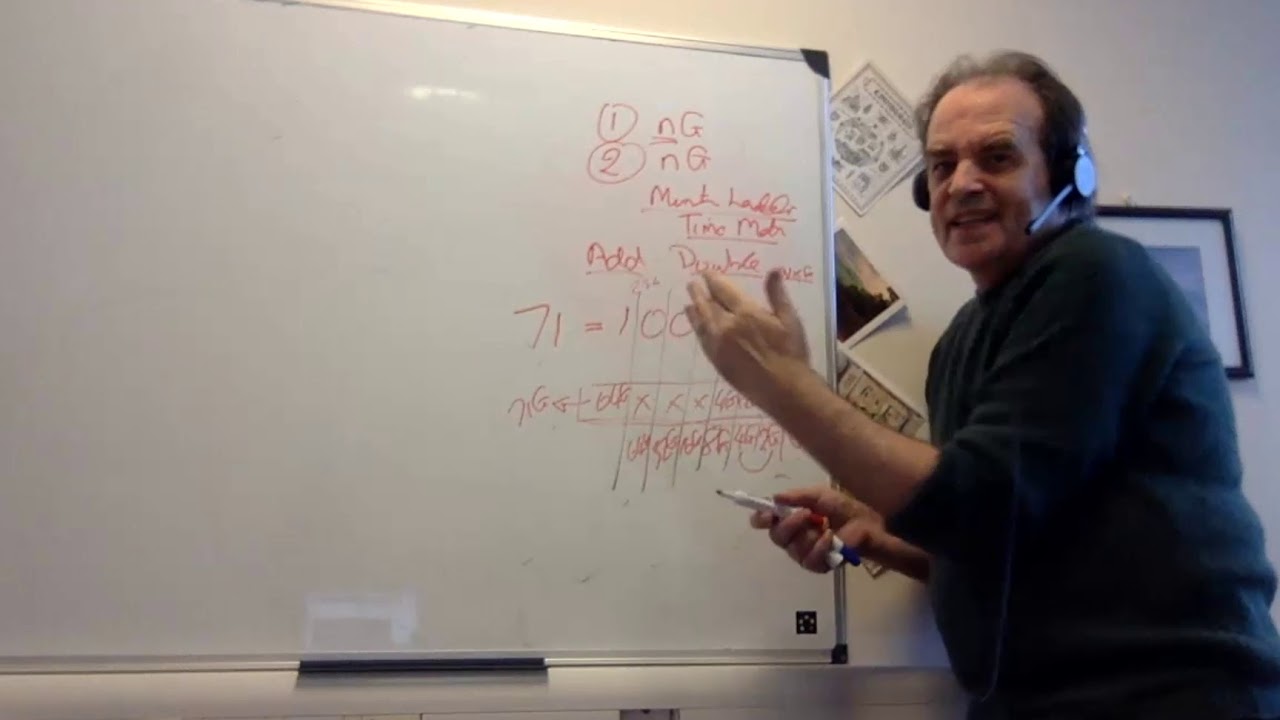
About this video
Demos used:
https://asecuritysite.com/ecdh/ecdh3
https://asecuritysite.com/ecies/go_ecies
https://asecuritysite.com/ecdh/ecdh3
https://asecuritysite.com/ecies/go_ecies
Video Information
Views
1.1K
Duration
23:19
Published
Mar 5, 2020
User Reviews
3.7
(1) Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.
Trending Now