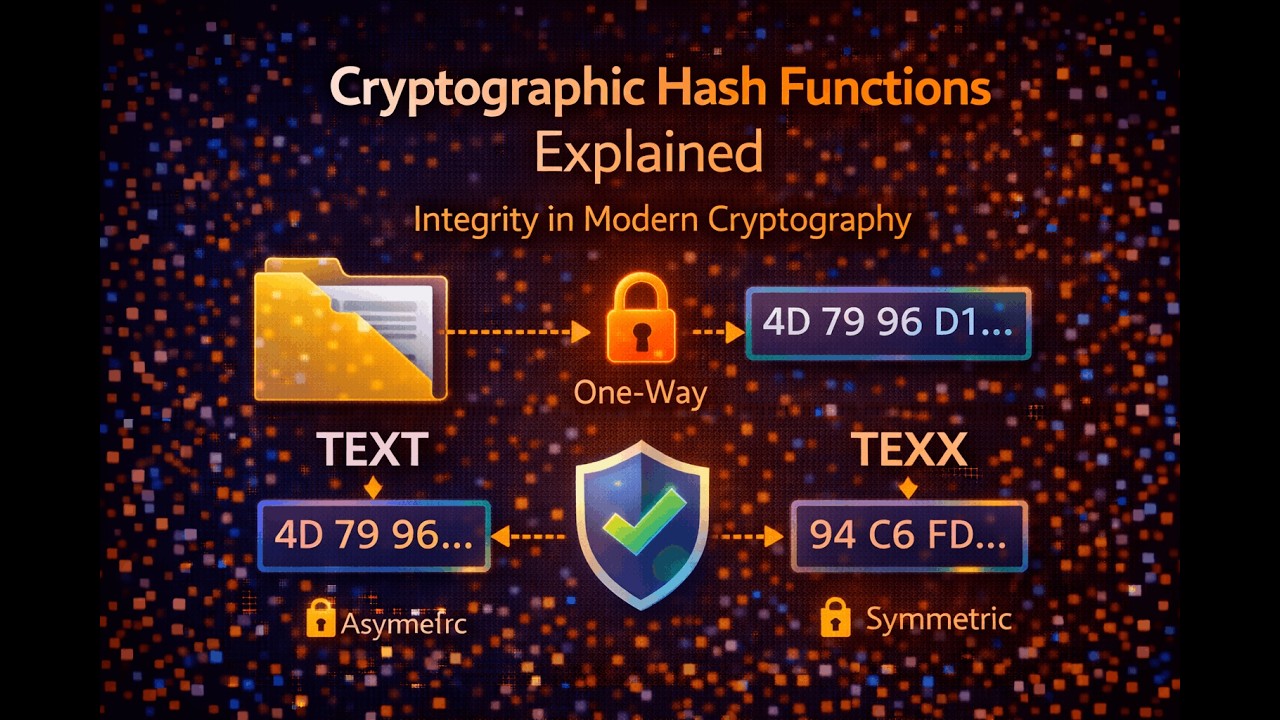
Cryptographic Hash Functions Explained | Integrity in Modern Cryptography
Encryption protects confidentiality, but how do we detect if data has been changed? This is where cryptographic hash functions play a critical role. In this...

Lexorithm
7 views • Feb 12, 2026
About this video
Encryption protects confidentiality, but how do we detect if data has been changed?
This is where cryptographic hash functions play a critical role.
In this video, we explain:
What a cryptographic hash function is
Why hash functions produce fixed-size outputs
The one-way property of hashing
The avalanche effect and why it matters
How hash functions ensure data integrity
You will also understand the difference between encryption and hashing, and why hashing is essential in digital signatures, password storage, and blockchain systems.
This explanation focuses on conceptual clarity, without diving into specific algorithms like SHA-256 or mathematical details.
📌 Previous video: Hybrid Cryptography – How Modern Secure Communication Works
📌 Next video: Properties of Secure Hash Functions
This is where cryptographic hash functions play a critical role.
In this video, we explain:
What a cryptographic hash function is
Why hash functions produce fixed-size outputs
The one-way property of hashing
The avalanche effect and why it matters
How hash functions ensure data integrity
You will also understand the difference between encryption and hashing, and why hashing is essential in digital signatures, password storage, and blockchain systems.
This explanation focuses on conceptual clarity, without diving into specific algorithms like SHA-256 or mathematical details.
📌 Previous video: Hybrid Cryptography – How Modern Secure Communication Works
📌 Next video: Properties of Secure Hash Functions
Tags and Topics
Browse our collection to discover more content in these categories.
Video Information
Views
7
Duration
6:01
Published
Feb 12, 2026
Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.