Secure & Anonymize with Tor Browser Setup 🔒
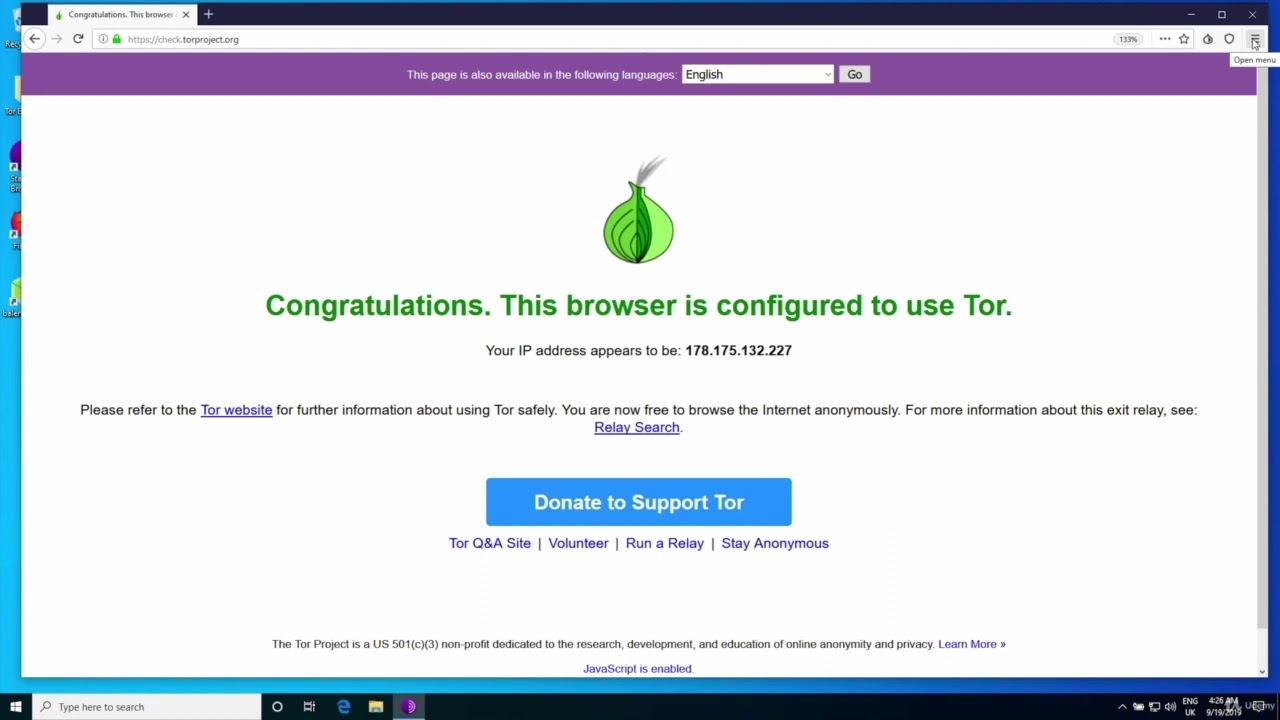
Learn how to configure Tor Browser for maximum security and anonymity while browsing privately using the Tor network.

Diverse_Content
371 views • Aug 10, 2023
About this video
The Tor Browser is a web browser that is specifically designed to use the Tor network for anonymous and private internet browsing. It's based on the Mozilla Firefox browser and incorporates the Tor protocol to provide users with enhanced privacy and security features.
Here's how the Tor Browser works:
Anonymity: When you use the Tor Browser, your internet traffic is routed through the Tor network, which consists of a series of volunteer-operated relays. This routing process helps hide your IP address and location from websites and online services you visit.
Encryption: The Tor Browser encrypts your data multiple times, creating layers of encryption that are decrypted by each relay in the network. This makes it extremely difficult for anyone to trace your online activities back to you.
Browsing Privacy: The Tor Browser prevents websites from tracking you across different sites, blocks third-party trackers, and disables most browser plugins that could compromise your privacy.
Access to .onion Sites: The Tor Browser allows you to access websites with addresses ending in ".onion," which are part of the Tor network's hidden services. These sites are only accessible through the Tor network and provide an additional layer of anonymity.
Security Enhancements: The Tor Browser includes various security features such as built-in HTTPS Everywhere to ensure secure connections and NoScript to block potentially harmful scripts.
User-Friendly Interface: The Tor Browser is designed to be user-friendly and accessible to individuals without technical expertise. It provides a simple way to start browsing with the Tor network's anonymity and privacy benefits.
It's important to note that while the Tor Browser offers increased privacy and anonymity, it may affect browsing speed due to the multiple relays that your data passes through. Additionally, while Tor can help protect your identity, it doesn't provide complete security against all potential threats. It's always recommended to stay informed about online privacy and security best practices.
The Tor Browser is often used by individuals who wish to browse the internet anonymously, avoid online tracking, access censored content, or maintain privacy in regions with strict internet surveillance.
Here's how the Tor Browser works:
Anonymity: When you use the Tor Browser, your internet traffic is routed through the Tor network, which consists of a series of volunteer-operated relays. This routing process helps hide your IP address and location from websites and online services you visit.
Encryption: The Tor Browser encrypts your data multiple times, creating layers of encryption that are decrypted by each relay in the network. This makes it extremely difficult for anyone to trace your online activities back to you.
Browsing Privacy: The Tor Browser prevents websites from tracking you across different sites, blocks third-party trackers, and disables most browser plugins that could compromise your privacy.
Access to .onion Sites: The Tor Browser allows you to access websites with addresses ending in ".onion," which are part of the Tor network's hidden services. These sites are only accessible through the Tor network and provide an additional layer of anonymity.
Security Enhancements: The Tor Browser includes various security features such as built-in HTTPS Everywhere to ensure secure connections and NoScript to block potentially harmful scripts.
User-Friendly Interface: The Tor Browser is designed to be user-friendly and accessible to individuals without technical expertise. It provides a simple way to start browsing with the Tor network's anonymity and privacy benefits.
It's important to note that while the Tor Browser offers increased privacy and anonymity, it may affect browsing speed due to the multiple relays that your data passes through. Additionally, while Tor can help protect your identity, it doesn't provide complete security against all potential threats. It's always recommended to stay informed about online privacy and security best practices.
The Tor Browser is often used by individuals who wish to browse the internet anonymously, avoid online tracking, access censored content, or maintain privacy in regions with strict internet surveillance.
Video Information
Views
371
Likes
3
Duration
7:32
Published
Aug 10, 2023
Related Trending Topics
LIVE TRENDSRelated trending topics. Click any trend to explore more videos.