Search Results for "what is remote user authentication in network security"
Find videos related to your search query. Browse through our collection of videos matching "what is remote user authentication in network security". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "what is remote user authentication in network security"
50 results found

13:49
Remote User Authentication using Asymmetric Encryption in Network Security | Woo and Lam Proposal
Chirag Bhalodia
30.0K views

9:47
We Remote Control Real Human - 100% Real || Remote Control man || Remote man
RANGOLI TV
13 views

20:53
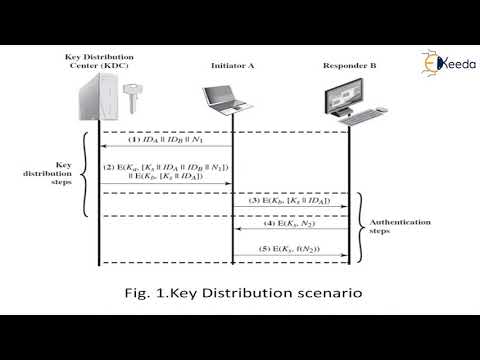
Remote User Authentication Using Symmetric Encryption | Needham Shcroeder Protocol
Chirag Bhalodia
33.5K views

21:42
Remote User Authentication: Principles & Techniques | Cryptography- #21is71 #cryptography #vtupadhai
VTU padhai
4.0K views

8:37
Remote user authentication using symmetric encryption
Anand Pashupatimath
4.6K views

20:25
INS: Unit-9 Remote User-Authentication (Kerberos)
Twinkal Patel
423 views

58:47
Kerberos Version 4 & 5 and Remote User Authentication with Asymmetric Encryption -#21is71 VTU 7thsem
VTU padhai
2.3K views

11:49
Authentication functions and 3 ways to produce authentication | Message authentication
Abhishek Sharma
263.4K views

11:49
Network Security - Message Authentication Code (MAC) | Cryptography and Network Security
Lectures by Shreedarshan K
2.5K views

23:56
What Is Network Security? | Introduction To Network Security | Network Security Tutorial|Simplilearn
Simplilearn
124.2K views

1:55
Retina Network Security Scanner - Conficker Worm Serial - Retina Network Security Scanner - Conficker Wormretina network security scanner conficker worm (2015)
Jose Sanchez
2 views

14:06
CRYPTOGRAPHY AND NETWORK SECURITY NOTES | NETWORK SECURITY NOTES | NETWORK SECURITY
DIVVELA SRINIVASA RAO
382 views

6:02
Network Security Model | Network security model in cryptography | Network Security
Chirag Bhalodia
22.5K views

8:25
Cryptography and Network Security Unit 1- Part 5 | Network Security & Network Access Security Models
TN55 RLE
442 views

4:27
Introduction to User Authentication - CompTIA Network+ N10-005: 5.3
Professor Messer
15.0K views
19:53
User authentication protocols | Cryptography and System Security
Ekeeda
307 views

31:22
23-IP Security (IPSec) Part 1 🔐 | Authentication Header Explained | Network Security
Sundeep Saradhi Kanthety
204.7K views

2:31:55
Network Security Full Course ! Cyber Security Tutorial ! Cryptography ! Encryption ! Authentication!
Sharan S
468 views

0:21
IRCTC User Id & password kaise banaye Hindi #How to create IRCTC user is & password
BIKASH 4888
3.1M views

8:22
How to input data from keyboard in python | keyboard input in python | read data from keyboard | python practically | easy way of python programming | python basics | read data from user | input from user in python | input function in python
ALL IN ONE
8 views

14:01
VB.NET Creating Login with Admin & User (User Level)
Codinger Tutorial
14 views

5:39
How to input data from keyboard in python | keyboard input in python | read data from keyboard | python practically | easy way of python programming | python basics | read data from user | input from user in python | input function in python
ALL IN ONE
1 views

6:02
Introduction to cryptography and network security|network security|computers security
SCS VAJRA TUTORIALS
35 views

9:23
MIME protocol in Cryptography and Network Security | Email security in Network Security
Abhishek Sharma
119.7K views

3:57
Security Mechanisms | Network Security | Cryptography and Network Security
Bikki Mahato
184 views

6:06
Need for Security | Network Security | Cryptography and Network Security
Bikki Mahato
405 views

8:36
Network Security Model| Model of Network Security | Information and Cyber Security
T N V S PRAVEEN
292 views

1:01
Lg ac remote demo in hindi // lg ac remote function
Home Appliances market
1.7M views

4:10
Remote - calm down remix (wire Oh) #Rippers Boss Datt# song Written by:remote
DARK3M VEVO
302.4K views

0:39
Does not work remote control JCB remote #shorts #experiment #entertainment
Mk HACKER
25.7K views

0:05
Download Physical Principles of Remote Sensing (Topics in Remote Sensing) PDF Free
Vfonseca
2 views

3:21
Remote Coder Positions | Remote Medical Coding Job Tips
PDNSeek .com
41 views

4:23
Remote control differences and best remote control
john info
4 views
0:19
8k Tv | Samsung Neo QLED solar-cell remote #samsung #remote #smartgadgets #8k
The Box Show
445.7K views

9:54
Valie Export: .......remote........remote (1973)
Filmow
1.4K views

23:47
Remote-Controlled Semi Truck?! Testing Scania’s New Pro Remote 2.0
Bruce Wilson
35.6K views

2:46
USER AUTHENTICATION USING CRYPTOGRAPHY AND STEGANOGRAPHY FOR WEB APPLICATIONS
Gagan Suneja
214 views
0:30
About For Books Mechanics of User Identification and Authentication: Fundamentals of Identity
dm_09d226e7605f9f5a1a3a6425e52120d4
0 views
1:09:38
CSE571-11-15B: User Authentication Protocols (Part 2 of 3)
Raj Jain
1.8K views

0:40
Why Continuous User Authentication Matters
CyberGuard
1 views

0:27
Unlocking the Secrets of User Authentication
CyberGuard
0 views
13:31
Build Node.js User Authentication - Password Login
Web Dev Simplified
565.0K views

8:01
Web Security-Security Threats and their solution in hindi-Security Policy-computer network security
Unbeaten Learning
77.8K views

6:12
#33 Message Authentication & Authentication Functions in Cryptography |CNS|
Trouble- Free
193.2K views

6:52
MAC / HMAC - Message Authentication Code / Hash Bashed Message Authentication Codes
Practical Networking
30.0K views

13:38
Cryptography (18CS744) Mutual authentication, one way authentication, kerberos and kerberos diff
1VA19CS061 YASHAS HM
106 views

40:38
Cryptography in network (Network security basics) |Lecture 25| Data Communication & Computer Network
Mateen Yaqoob
58 views

12:55
Types of Message Authentication | Message Encryption | Part 1 | Network Security | Hindi Urdu
Ask Faizan
4.3K views
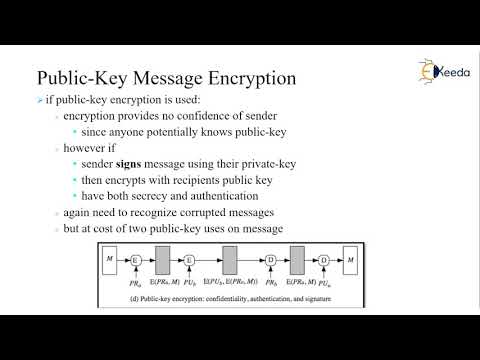
12:54
Authentication Functions | Cryptography and Network Security
Ekeeda
910 views
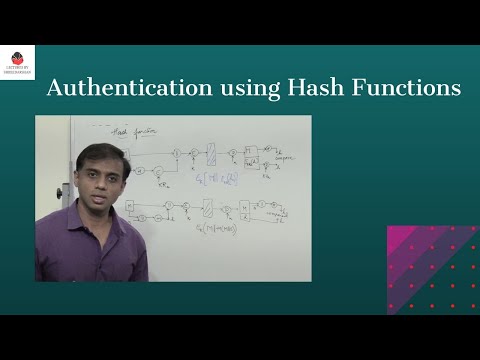
16:37
Message Authentication using Hash Functions - Network Security
Lectures by Shreedarshan K
4.3K views