Search Results for "secure APIs"
Find videos related to your search query. Browse through our collection of videos matching "secure APIs". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "secure APIs"
50 results found

7:15
How to secure Gmail ? || Gmail ko secure kaise kare ?क्या आपका Gmail Secure है ?
DoWithMe Start Learning
1 views

1:10
APIs explained in the simplest way 🍽️💡#api #coding #programming #softwaredevelopment #software
Rayhan's Tech Realm
15 views

1:30
Einführung in die APIS IQ-Software - FMEA einfach gemacht!
Daniel Adams
2 views

25:29
Comparing the usability of cryptographic APIs | Yasemin Acar (Leibniz U. Hannover) | RWC 2018
Real World Crypto
1.6K views
15:04
Key wrapping for cryptographic apis
CodeGrip
18 views
17:58
All you need to know about APIs | Product Management | PM School
PM School by NextLeap
59.3K views

19:19
Types of WordPress APIs with Documentation | Complete Guide for Developers
CodePress Academy - WordPress Tutorials
8 views
2:43
Orange APIs Story - At the Gym - Datavenue
Orange Dev
104 views

11:20
RESTful APIs in 100 Seconds // Build an API from Scratch with Node.js Express
Fireship
1.8M views

9:32
Devar Aur Bhabhi Ki Apis Mein Larai...!! #kinzahashmi #azaansamikhan - Hum Dono - HUM TV
HUM TV
165.9K views
12:35
JavaScript Visualized - Event Loop, Web APIs, (Micro)task Queue
Lydia Hallie
993.5K views
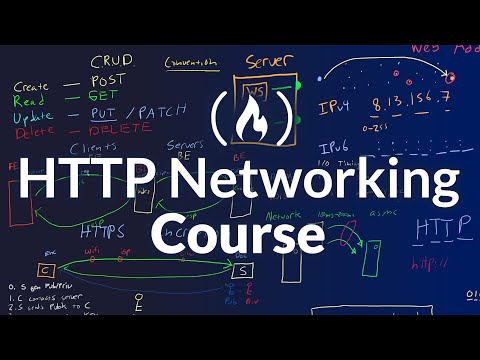
5:08:48
Full HTTP Networking Course – Fetch and REST APIs in JavaScript
freeCodeCamp.org
1.1M views
3:57
APIs Explained (in 4 Minutes)
Exponent
1.9M views

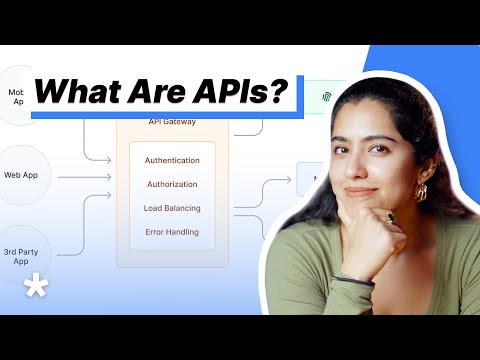
6:49
What Are APIs? - Simply Explained
Simply Explained
923.2K views

11:36
APIs Explained | Real World Examples
CertBros
595.4K views
6:41
APIs Explained in 6 Minutes!
ByteByteGo
104.2K views

9:06
A Beginner's Guide to REST APIs in Under 10 Minutes!
Cloudmancer
27.1K views

0:11
6 Common Ways to Build APIs
Amigoscode
224.4K views

2:19:33
APIs for Beginners - How to use an API (Full Course / Tutorial)
freeCodeCamp.org
4.7M views
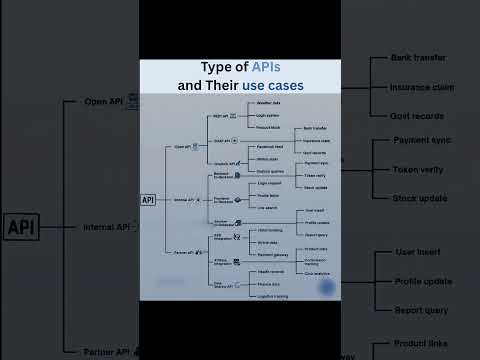
0:07
APIs Explained with Real Use Cases
CodewithPrashant
33.5K views

0:32
REST APIs Explained in 30 secs #javascript #python #web #coding #programming
ByteByteGo
307.3K views

3:24
Nobody Explained APIS Like This Before In 4 Minutes!
Professor explainer
86.9K views

1:18:34
Cryptographic Key Management APIs - Graham Steel
secappdev.org
8.8K views

0:13
Difference between unconditionally secure and computationally secure in cryptography and .....
SUKANYA BASU
973 views

8:37
SSH (Secure shell) protocol in Hindi | Secure shell protocol in Network Security
Abhishek Sharma
84.3K views

46:18
Roll Your Own Secure Cloud Storage with SSHFS - Secure Shell File System - Hak5
Hak5
5 views

4:10
Difference between Computationally Secure and Unconditional Secure Cipher | Information Security
Easy Engineering Classes
6.4K views

0:55
Overview of Secure Aggregation #ai #artificialintelligence #machinelearning #aiagent Overview Secure
NextGen AI Explorer
12 views

2:05
Secure USB Flash Drive - SanDisk Enterprise Secure ...
John Objet
1 views

0:05
Read Secure Software and Comm. on Handheld Devices: Secure Software and Communication on Handheld
Isaksen
2 views

3:39
Medical Coding Services | Secure Medical Coding & Secure Medical Data Handling
PDNSeek .com
5 views

4:53
Best browser for privacy 2021 | Iridium Browser | A browser securing your privacy | Most Secure Web Browsers That Protect Your Privacy | most secure browser 2021
FOCUS EXCLUSIVE
13 views
0:25
A Secure Erasure Code-Based Cloud Storage System with Secure Data Forwarding
satish20059
259 views
![Towards more Practical Secure Computation: Efficient Protocols for Secure Linear Algebra [1/2]](/image/i.ytimg.com/vi/Hs-7ixoSqAA/xhqdefault.jpg.pagespeed.ic.BPwrxXKFrf.jpg)
41:29
Towards more Practical Secure Computation: Efficient Protocols for Secure Linear Algebra [1/2]
Microsoft Research
77 views

19:03
What is SSL? | What is SSL Ceritificate? | SSL Architecture and Protocols | Secure Socket Layer
Chirag Bhalodia
72.1K views

5:49
US Marines Still Battling to Secure Fallujah 2004
Channel 4 News
2.2M views

55:35
Cryptography and Network Security Part 4/5 | WIlliam Stallings |Secure communication - S8 EC, CS,KTU
bushara abdulrahim
498 views

44:23
Blockchain Cryptography Math Explained: A Guide to the Mathematics Behind Secure Digital Ledgers
Network Technician
6 views

36:07
Quantum Cryptography: How Weird Physics Could Secure Your Secrets Forever
Volkan Duran
55 views

10:22
INFORMATION SECURITY( HINDI).WHAT IS CRYPTOGRAPHY AND HOW IT WORKS TO SECURE YOUR INFORMATION.(ICT)
Computerprime
2.3K views

6:17
Secure QR-Code Based Message Sharing System Using Cryptography and Steganography
SHOAIB SHAIKH
633 views

7:41
An RSA-Based Secure Image Steganography Technique Using Adaptive Data Hiding - Mid
Akash Joy
7 views

12:01
Secure Data Transfer Based on Visual Cryptography - Part1
AmAn
30 views
3:17
How Does No-Cloning Theorem Secure Quantum Cryptography? - Quantum Tech Explained
Quantum Tech Explained
0 views

32:28
17-How Public Key Distribution Works? 💡 | Secure Key Sharing in Network Security
Sundeep Saradhi Kanthety
107.5K views

39:04
Cryptoparty: An Introduction to Secure, Usable Encryption Tools for All
RSA Conference
3.8K views

2:44
Why Is Quantum Cryptography The Future Of Secure Communication? - Quantum Tech Explained
Quantum Tech Explained
7 views
0:35
Understanding AES Encryption: Simply Explained in 60 Seconds! #ytshorts #secure #internet
Tamilayrus - தமிழ்அய்ரஸ்
785 views

1:33
Secure File Storage in Cloud Computing Using Cryptography in Python | Python Project Ideas
Nevon Projects
56.2K views

14:15
Entity Encryption using AES | Spring Boot | JPA | Advanced Encryption Standard | Secure your data
VKS Tech
10.7K views
Page 1