Search Results for "android vulnerabilities"
Find videos related to your search query. Browse through our collection of videos matching "android vulnerabilities". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "android vulnerabilities"
50 results found

2:57
Android X12, Android A9, Android 2 sim, Android Dual sim, Android Китай
Neomi Mccorkle
2 views

8:29
Latest Android-One smartphone ⚡⚡| Cheapest budget android-One smartphone #android #android-one #stock-android
AB Multimedia
37 views

7:15
What is Android and what are the features of android ,Latest version of android ,Android 12, Android
Vrishank edu
1 views

0:25
Android Application Development, Android App Development, Android Developers, Android Development
David Mathew
4 views

3:13
Android FG8, FG8, 2 sim Android, Android Dual sim, Android Китай
Neomi Mccorkle
7 views

6:48
Top 5 Android Security Apps|Security Apps for Android|Android Security App|App Android
TechTips
7 views

4:25
free android bulk sms software online sms sending text messaging software tool freeware download free android send online sms free from free android apple how to send online bulk sms from free android shareware
sendonlinesms
323 views

1:41
android apps development, android apps developer, android mobile application development
Vishal Mlm
29 views

0:48
Android Application Development | Hire Android App Developers | Android Developers
Keyideas Infotech Private Limited
2 views
![[3 In 1]GTA V For Android Fake Or Real?,How To Create Android App & How To Stream PC Games On Android - Explained](/image/s2.dmcdn.net/v/Avd9n1eoJr1D5rMP0/xx720.pagespeed.ic.E0cq4v5b4X.jpg)
22:27
[3 In 1]GTA V For Android Fake Or Real?,How To Create Android App & How To Stream PC Games On Android - Explained
Hacking Ustaad
4 views

8:40
Krrish 3 Android Game | Krrish 3 Android Gameplay | Krrish 3 Android Game Download
Kono
13 views
6:28
how can i transfer data android to apple device // apple ke phone se android phone me data kaise bheje ya transfer kare//android phone se apple ke phone me data kaise bheje ya transfer kare
Technical-BAAT
32 views

12:03
WebView Android Studio: What is WebView in Android? | Android WebView Tutorial
Kayraa Programming
3 views

0:44
Android Application Development Video - Android App Development, Android Application Developers
androidappindia
257 views

0:57
Android Apps Development, Android App Programming, Android Application Developers
dotcominfoway
12 views
6:22
Delete Huye Videos Photos ko Wapas kaise Laye || How To Recover Deleted Videos And Photos On Android How To Recover Deleted Photos On Android Devices recover deleted photos how to recover deleted photos android data recovery recover photos recover delete
Meghraj Gurjar
12 views
![Android [Android Tunado] - Baixaki Android](/image/s2.dmcdn.net/v/AXMGf1clV6nfxlbxn/xx720.pagespeed.ic.L9CkTDGBAP.jpg)
10:13
Android [Android Tunado] - Baixaki Android
Tecmundo
2 views

5:23
Best Android App Made For Only Muslims-No More Facebook-Try This app Once || Best Android Apps 2018 || Android Apps
Ghulam Mustafa
60 views

0:09
top Android hacking app | hacking apps | hacking software in Android #viral #hack #android #phone
THE TWO FACT
485.7K views

2:14
OpenVPN android (OpenVPN service for ANDROID) VPN service android.
vpnunblockproxy
201 views

1:43
how to convert image to pdf on android | how to convert .jpg to .pdf on android | #android
Make knowledge free
232 views

0:08
CSV file reader for Android | Import CSV file in Android app | Open CSV file on Android app #shorts
Cloudzone Apps
7.2K views

15:17
Install jio tv on Android TV 💯🔥! how to install jio tv in Android TV ! jio tv working on Android/Google TV 💯🔥
Androoid world
1.2K views

8:37:05
Android Full Course - Learn Android in 9 Hours | Android Development Tutorial for Beginners| Edureka
edureka!
1.4M views

25:17
CS C S009 Non-Cryptographic Protocol Vulnerabilities
Studio IIT Bombay
539 views

5:35
Cryptography Basics: Symmetric and Asymmetric Cryptography - Identifying Security Vulnerabilities
Petrina Corine
25 views
34:39
Cryptography careers and IoT vulnerabilities | Cyber Work Podcast
Infosec
4.0K views

41:17
CS M S022 Non-Cryptographic Protocol Vulnerabilities
Studio IIT Bombay
429 views
3:21
How Does The Rise Of AI Impact Military Cryptography Vulnerabilities? - Tactical Warfare Experts
Tactical Warfare Experts
17 views

2:26:01
Virtual Machine Reset Vulnerabilities; Subspace LWE; Cryptography Against Continuous Memory Attacks
Microsoft Research
314 views

2:56
How Common are Cryptographic Vulnerabilities?
Cryptosense
615 views

1:32:49
RWPQC 2024 Session 5: Applied Cryptography, Vulnerabilities, and Countermeasures
SandboxAQ
26.2K views

38:56
Nmap Tutorial For Beginners | Nmap Tutorial to find Network Vulnerabilities | Amader Canvas
Amader Canvas
45.1K views
10:01
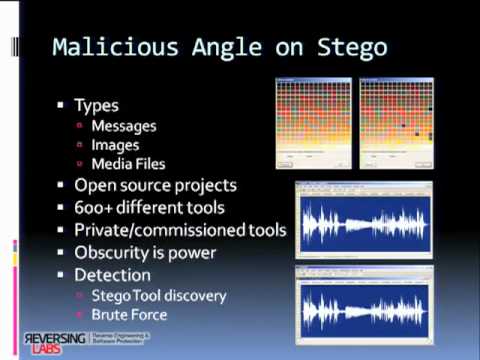
Blackhat Europe 2010: Steganography and Vulnerabilities in Popular Archives Formats 7/8
Christiaan008
148 views

1:11:10
Black Hat EU 2010 - Hiding in the Familiar: Steganography & Vulnerabilities in Pop Archives Formats
Black Hat
231 views

0:32
How Attackers Exploit Diameter Protocol Vulnerabilities
Offensive Wireless
523 views
10:01
Blackhat Europe 2010: Steganography and Vulnerabilities in Popular Archives Formats 1/8
Christiaan008
1.8K views
0:47
Researchers Discover New Vulnerabilities In Common Email Encryption Tech
Entertainment (now)
5 views
0:46
Risks Are Accelerating, Yet Traditional Security Vulnerabilities Plague Cryptocurrencies
Benzinga
14 views

10:41
USENIX Security '20 - TeeRex: Discovery and Exploitation of Memory Corruption Vulnerabilities...
USENIX
668 views
8:44
Armitage- Scanning a network for computers and finding their Vulnerabilities
DonDoes30
19 views
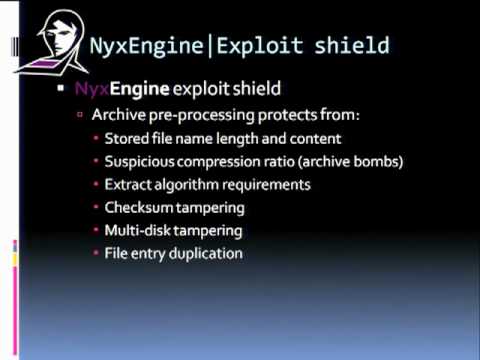
10:01
Blackhat Europe 2010: Steganography and Vulnerabilities in Popular Archives Formats 6/8
Christiaan008
194 views

5:45
Threats Vulnerabilities and Exploits
IBM Technology
34.4K views

17:37
TWIM Episode 2: Sodinokibi Ransomware Vulnerabilities & Maryland Criminalizes Malware Possession
This Week in Malware
66 views

29:23
Quantum Threat: Impact of Quantum Computers on Cybersecurity | Threats & Vulnerabilities Summit 2025
Cloud Security Alliance
155 views

20:58
Hackers expose deep cybersecurity vulnerabilities in AI | BBC News
BBC News
524.3K views
0:33
SQL Injection 101: Exploiting Vulnerabilities
CyberSquad
354.4K views
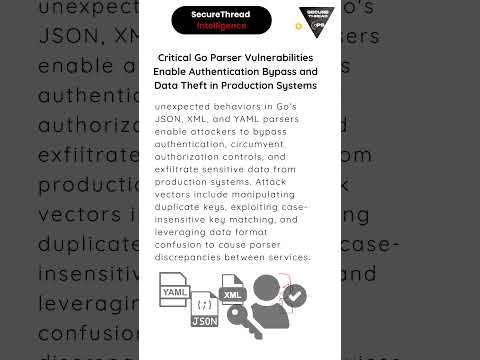
0:18
Critical Go Parser Vulnerabilities Enable Authentication Bypass and Data Theft in Production Systems
Secure Thread
122 views

5:10
Exploiting Windows Vulnerabilities with Metasploit
Hak5
831 views
9:35
Data Exfiltration Vulnerabilities in LLM Applications and Chatbots: Bing Chat, ChatGPT and Claude
Embrace The Red
1.9K views