Search Results for "sampling technique"
Find videos related to your search query. Browse through our collection of videos matching "sampling technique". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "sampling technique"
50 results found

0:45
FL STUDIO SAMPLING TUTORIAL • Advanced Chopping
Busy Works Beats
507.2K views
1:29:06
Q&A session with Scott Aaronson on Quantum Supremacy with Boson Sampling | QWorld
QWorld
1.5K views

0:37
Sampling sounds with Blackstratblues: Ganpati Procession Recordings
Sinusoidal Music
1.0K views

4:51
Fully Funded PhD in Quantum Computing—Fermion & Boson Sampling|CTP PAS Poland|Apply by 8 August 2025
scholars scholarship
3 views

1:02:40
Zixin Huang - Private-Key Quantum Cryptography with Boson Sampling devices
LaQuTeC
111 views
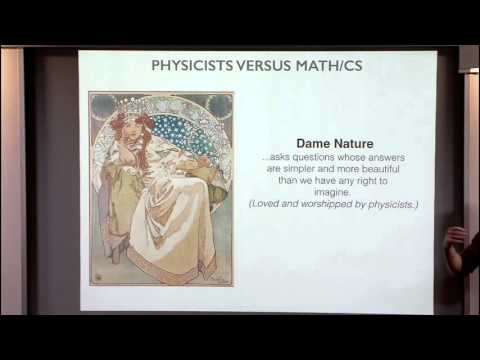
1:10:35
The Partition Function, Sampling and Equilibration in Physics
Simons Institute for the Theory of Computing
801 views

49:03
Aifer Ed Talk | Psychology Research Guidance Talk 2: Hypothesis and Sampling
Aifer UG Plus | PG Entrance
259 views

1:56
Sampling cassettes 🧨 #sp404 #boombap
Mad Doak
1.7K views
2:57:18
Quantum Complexity Theory: Lecture 9 - Boson Sampling
Sevag Gharibian
1.0K views
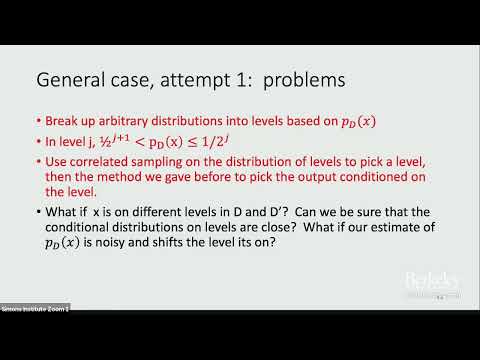
30:30
Cryptographic Hardness of Correlated Sampling
Simons Institute for the Theory of Computing
265 views

0:35
Capstone Designs Graphic Art Sampling
capstonedesigns
18 views
5:52
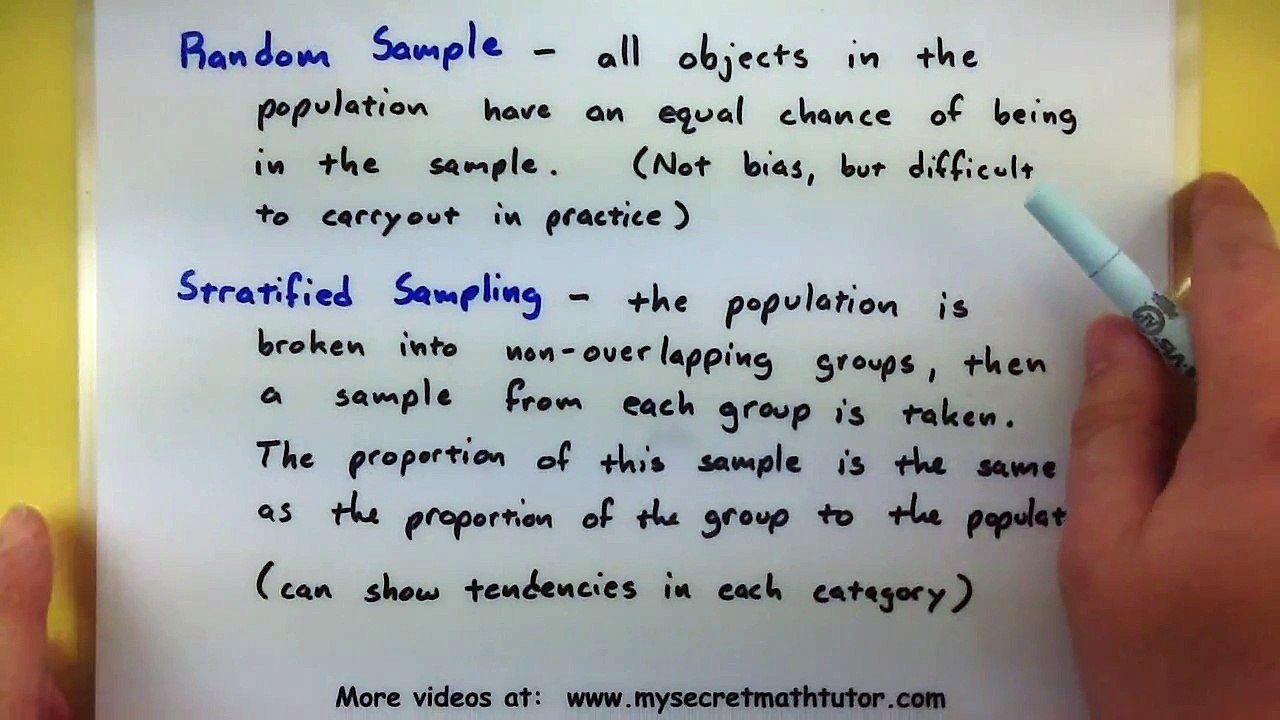
Statistics - Types of sampling
Randy Welker
5 views

2:36
Sampling Techniques
Luda Dinah
1 views

3:13
Understanding MIDI / Understanding Samplers and Sampling
ProAudioDVDs
9 views

1:09:54
Sampling Random Stuffs
Wulffiana
3 views
7:35
High Quality Sampling
donovan69
2 views
29:47
The Nyquist-Shannon sampling theorem, Nintendo DS emulators and QT programming - Hak5
Hak5
488 views
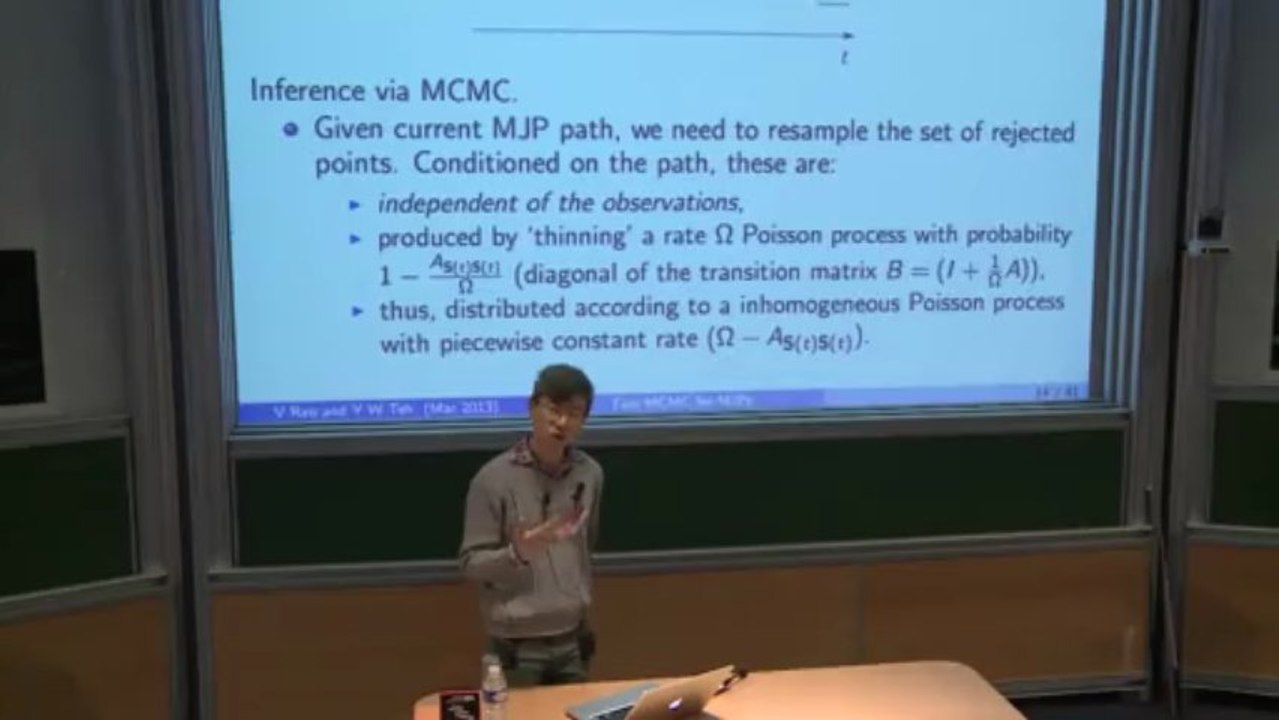
40:51
Fast MCMC sampling for Markov jump processes and extensions(Yee Whye TEH-Oxford)
IHES Institut des Hautes Études Scientifiques
2 views

0:11
Cryptography techniques || Substitutional technique || Transpositional technique || UNIT 01
Online Learning
5.0K views
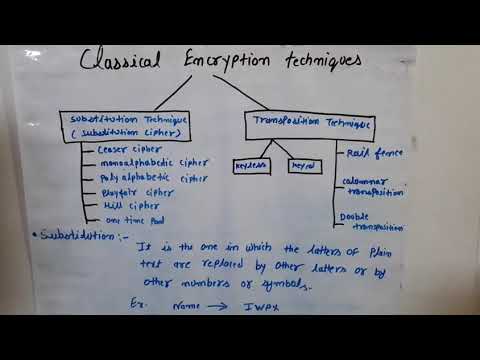
4:05
Classical encryptiin techniques, substitution technique, transposition technique
Gaurav Khatri
498 views
23:16
NIS-3.2-1 : Types of Cipher Technique (Substitution Cipher Technique, Caesar cipher)
rathod_sir
361 views

4:05
Substitution Cipher Technique V/s Transposition Cipher Technique in Cryptography and Network Securit
Short Tricks Learning
631 views

0:46
What technique do you use during competitive eating?: Competitive Eating Strategy And Technique
Scribble
1 views

5:42
Hair Cutting Technique: Mahogany Cutting Technique
Grant Sharp
8.7K views
3:05
Steganography: How to send secret file using steganography technique || by tech knowledge
tech knowledge
92 views
6:31
Hill cipher technique
Sivaraman
4 views

4:14
Row Transposition Technique|| Cryptography and Network Security
Lab Mug
7.1K views

56:41
Day 21 - What Is Image Steganography? | Secret Data Hiding Technique
Cyber SecGuru
59 views
6:17
Show, Don't Tell Writing Technique | EasyTeaching
EasyTeaching
124.7K views

7:57
griet-it-2012- a cryptographic technique for heterogenous sensor networks.wmv
Maruti Kumar
18 views

1:36
How to hide files/data behind any file using command prompt- Crptography Technique
TechSci City
1.1K views

1:01
Technique pour avouer ses sentiments à son crush 😂 #crush #sms #message #dm #histoire #humour
MrFromages
314.9K views
16:00
PLAYFAIR CIPHER WITH EXAMPLE||SUBSTITUTION TECHNIQUE||MATHEMATICS OF CRYPTOGRAPHY-- NETWORK SECURITY
t v nagaraju Technical
45.9K views
7:41
An RSA-Based Secure Image Steganography Technique Using Adaptive Data Hiding - Mid
Akash Joy
7 views

0:21
Satisfying art with glue gun technique!🎨 #art #artideas #craftideas #paintingideas #viralshorts
Mr.RS.technologist
3.0M views

31:43
Data Hiding with Encrypted Multi Secret Sharing using Modified LSB Technique
IJERT
167 views

8:21
Final Year Projects | AN OVERVIEW OF DATA HIDING TECHNIQUE:-STEGANOGRAPHY
ClickMyProject
659 views

0:10
Technique of taekwondo fight 🥋
PS Taekwondo
2.6M views

5:51
Steganography technique
Kids& Code
1.8K views

4:46
Demonstration of Implementation of Image Steganography using LSB Technique and Morse Code.
ProkillerGirl
110 views

12:59
Caesar Cipher Encryption and Decryption with Solved Example || Substitution Technique
A Z Computing
37.3K views

1:01
Kisiko Manane Ki Ninja Technique!! 🤣 😂 #k3g #srk #funny #kareenakapoorkhan #hrithikroshan #kajol
Just Chill
19.2M views

15:14
BEHAVIOURAL Interview Questions & Answers! (The STAR Technique for Behavioral Interview Questions!)
CareerVidz
663.7K views
10:53
PART 4 | HASH FUNCTION ATHENTICATION TECHNIQUE IN CRYPTOGRAPHY & NETWORK SECURITY (BANGLA)
COMPUTER SCIENCE WITH BHASKAR SIR
229 views

11:08
5 STAR Interview Questions and ANSWERS! How To Use The STAR Technique!
CareerVidz
87.8K views
2:25:42
Cryptography in network& computer security |Cryptography Encryption Technique| chapter three #በአማርኛ
Universal-tube
6.2K views

10:57
Additive Shift Ceaser Cipher Technique || Lesson 5 || Cryptography || Learning Monkey ||
Wisdomers - Computer Science and Engineering
435 views
7:38
MONOALPHABETIC CIPHER || SUBSTITUTION TECHNIQUE || CRYPTOGRAPHY || LECTURE 6 || HIRALSHASTRI
Shastri Hiral
112 views

4:55
A new image encryption technique combining Elliptic Curve Cryptosystem with Hill cipher in Matlab
OKOKPROJECTS
204 views

12:06
TRANSPOSITION TECHNIQUES || RAIL FENCE TECHNIQUE || COLUMNAR TRANSPOSITION -- NETWORK SECURITY
t v nagaraju Technical
11.8K views
Page 1