Search Results for "key escrow information security"
Find videos related to your search query. Browse through our collection of videos matching "key escrow information security". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "key escrow information security"
50 results found
6:28
Key Of The Kaaba History In Urdu | key of kaaba family | kaaba,key of kaaba,key of the kaaba history in urdu,key of kaaba history,key of kaaba history in urdu,history of khana kaba,key of kaaba history in english,amazing history of key of khana kaaba
Knowldge Factory
10 views
24:35
LECTURE 38 UNIT 3 EXPLAIN KEY ESCROW
J
38 views

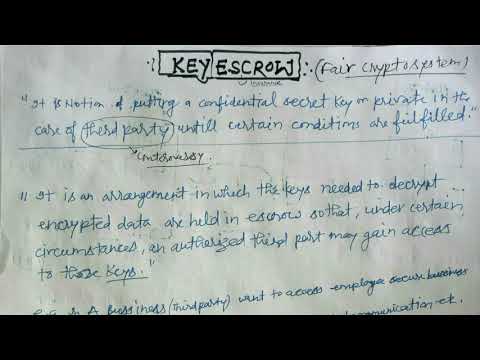
5:11
Foundations of Cryptography 5-5: Key Escrow
TechKnowSurge
486 views
6:13
key escrow in Hindi
CSJM CLASSES INSTRUCTOR RAM SWAROOP
2.7K views

0:39
sbb key programmer review,Sbb Key Programmer,sbb car key programmer,sbb key programmer v33 manual,sbb key programmer v33,key programmer sbb
lara-baby
8 views

1:45
Asymmetric key cryptography || Public key cryptography || Information security and cyber security
Pooja Patel
41 views
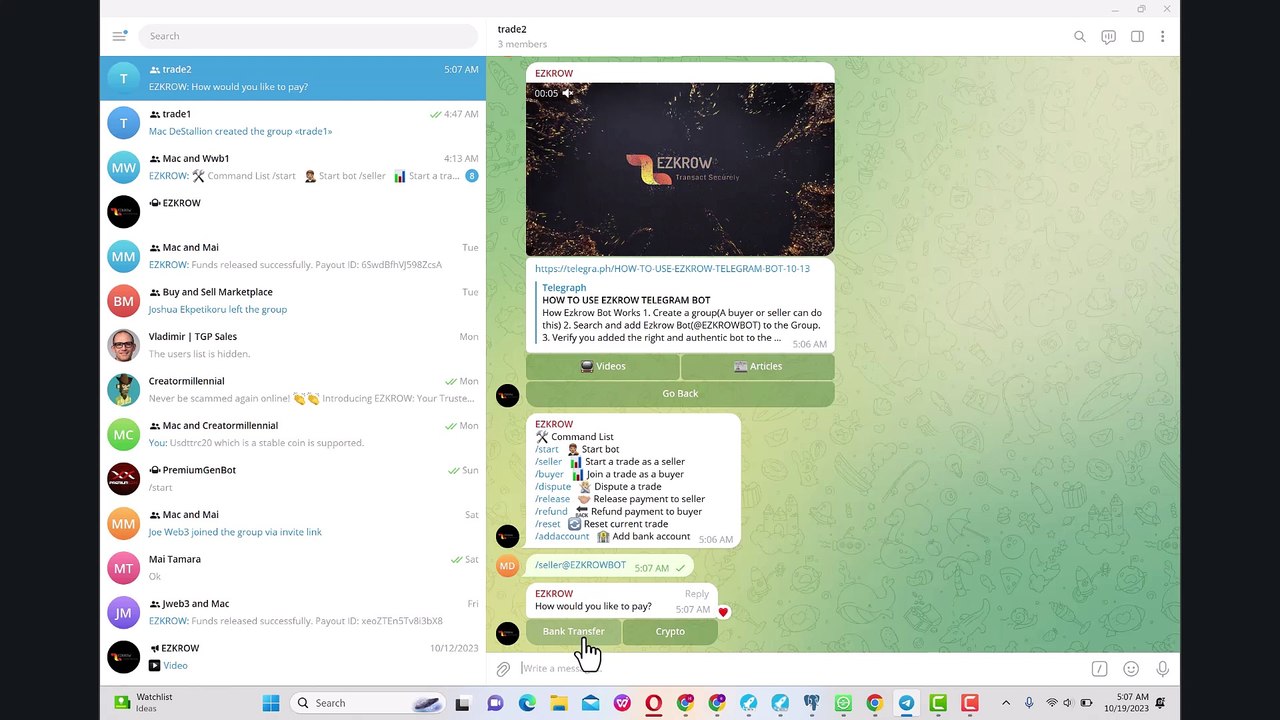
16:15
ezkrow: fully automated telegram escrow bot
joe uman
725 views

0:35
Key west florida accommodations, key west vacation rentals, key west condos, key west hideaways, key west nightlife
Tommy Lee
57 views
0:15
Elements of Information Security #shorts #security #information #knowledge #facts #education
Educryst
3.1K views

6:54
What is Information Security ? | Information Security Explained in 5 mins | Great Learning
Great Learning
54.6K views
5:12
What is Information Security || Introduction to Information Security Tutorial in urdu/hindi
A Z Computing
66.0K views

3:10:22
Certified Information Security Manager, CISM, Course 01, Information Security Governance,
Open Learning
108.6K views
0:15
Download Legal Issues In Information Security Jones Bartlett Learning Information Systems Security Assurance Pdf
Ogiemaryanti
5 views
0:15
Download Legal Issues In Information Security Jones Bartlett Learning Information Systems Security Assurance Series pdf
Ogiemaryanti
2 views
2:59
Information Security Project output - Information security Project
Academic College Projects
2 views
0:17
PDF Download Electronic Healthcare Information Security Advances in Information Security PDF Online
Choaib15omran
1 views

0:16
Read Electronic Healthcare Information Security Advances in Information Security Ebook Free
Abdur Jagot
0 views
![[PDF] Electronic Healthcare Information Security (Advances in Information Security) Popular](/image/s2.dmcdn.net/v/Hg3Wn1e9-WYLu6Q99/x720)
0:27
[PDF] Electronic Healthcare Information Security (Advances in Information Security) Popular
Biel Payton
1 views
6:14
Difference between Hash and MAC in Information Security | Comparison | Information Security Lectures
Easy Engineering Classes
10.7K views

1:53
What is Information technology?, Explain Information technology, Define Information technology
Audioversity
66.2K views

0:56
Information Technology – All About Information Technology - What Information Technology means
ComputeWorld
1 views

50:02
Cryptanalysis of Symmetric Key Cryptography | Private Key Cryptography | Information Security
Shiv Yog Classes
8 views

0:21
The difference between symmetric key & asymmetric key cryptography | information security
Pooja Patel
8 views

24:37
Information Security Lec 05: Low, Moderate & High Security Levels | Computer Security Challenges
Tech CS&IT
2.2K views

8:36
Network Security Model| Model of Network Security | Information and Cyber Security
T N V S PRAVEEN
292 views

18:38
Information Security- Part 3 - Wireless Security, Cryptography, Application/Host Security, and Logs
Russ Esposito
85 views

8:46
Security Mechanisms | Computer Network Security | Information and Cyber Security |Full Course|Lec-04
Abhideep Online Education
11.7K views

10:19
#2 Security Approaches and Principles or Goals of Security- Cryptography |Information Security|
Trouble- Free
99.1K views

12:12
#5 Security Mechanisms In Network Security | Information Security |
Trouble- Free
71.0K views

5:30
What is security , information security and cyber security
Noor_khan official
3 views

9:43
Information Security (IS) Vs Cyber Security (CS) || Security Goals
Simple & Effective Learning
735 views

10:22
INFORMATION SECURITY( HINDI).WHAT IS CRYPTOGRAPHY AND HOW IT WORKS TO SECURE YOUR INFORMATION.(ICT)
Computerprime
2.3K views
54:30
Designing an Information Architecture to Support Cyber Security and Information Assurance
Tech
213 views
![[PDF Download] Information Assurance: Security in the Information Environment (Computer Communications](/image/s1.dmcdn.net/v/D7aRX1cldHGr_Ey5g/x720)
0:05
[PDF Download] Information Assurance: Security in the Information Environment (Computer Communications
Donammis42
1 views
![[PDF Download] Managing Risk In Information Systems (Information Systems Security & Assurance)](/image/s2.dmcdn.net/v/DB1S81e0J9e8R5SHb/x720)
0:07
[PDF Download] Managing Risk In Information Systems (Information Systems Security & Assurance)
Zqleukji
1 views
0:07
Read Information Assurance: Security in the Information Environment (Computer Communications
Tegroothulsens
1 views
0:06
Read Information Security: Policy Processes and Practices (Advances in Management Information)
Abazasdze
0 views
0:07
Read Managing Risk In Information Systems (Information Systems Security & Assurance Series)
Tsereteli Lia
0 views
0:05
Read Information Assurance: Security in the Information Environment (Computer Communications
Hecke
0 views
0:08
Read Managing Risk In Information Systems (Information Systems Security & Assurance Series)
Bbuhler
0 views
0:08
Read Trusted Recovery and Defensive Information Warfare (Advances in Information Security)
Ungers
1 views
0:05
Read Multidisciplinary Perspectives in Cryptology and Information Security (Advances in Information
Ungers
3 views
0:05
Read Multidisciplinary Perspectives in Cryptology and Information Security (Advances in Information
Ssanner
0 views
0:07
Download Managing Risk In Information Systems (Information Systems Security & Assurance Series)
Maisi Baker
3 views
0:27
Read Information Assurance: Security in the Information Environment (Computer Communications and
Scott Genesis
0 views

0:23
Read Information Security: Policy, Processes, and Practices (Advances in Management Information)
Hawkins Christine
0 views
![[Read PDF] Information Assurance: Security in the Information Environment (Computer Communications](/image/s1.dmcdn.net/v/H0ZzQ1e0SUQ22BTpJ/x720)
0:24
[Read PDF] Information Assurance: Security in the Information Environment (Computer Communications
Dawoodbertrad
4 views
![[FREE] Legal Issues In Information Security (Jones Bartlett Learning Information Systems](/image/s1.dmcdn.net/v/RJ8wz1epHT6d0flFG/x720)
0:34
[FREE] Legal Issues In Information Security (Jones Bartlett Learning Information Systems
lamajshamar
1 views

0:53
Computer Security: Personal Information & Passwords : Is it safe to send personal information in an email?
VideojugTechnologyandCars
1 views

9:55
what is symmetric key cryptography and asymmetric key cryptography , public key and private key
sawji gyaan
10 views