Search Results for "Cybersecurity Governance"
Find videos related to your search query. Browse through our collection of videos matching "Cybersecurity Governance". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "Cybersecurity Governance"
50 results found

44:14
CyberSecurity Steganography
Learn & Earn
3 views
![Cybersecurity CLASSROOM [Cohort 4]](/image/i.ytimg.com/vi/4OKF3Ne0qjw/hqdefault.jpg)
1:54:36
Cybersecurity CLASSROOM [Cohort 4]
MyDreamConnect LC
4 views
0:07
Cybersecurity Definition #15 - Brute Force Attack #shorts #short #bruteforce
Ken Underhill - Cybersecurity Training
1.3K views
0:47
How Do Data Breaches Happen? #HIPAA #EDI #cybersecurity #breach #IT #technology #tech #healthcare
HIPAA Vault
82 views
0:44
Asymmetric Encryption Visually Explained #cybersecurity #shortsvideo
ByteQuest
26.4K views

0:39
Asymmetric Encryption is Just a Mailbox #ai #twitch #cybersecurity #security
gdcomplex
650 views

11:08
7 Things I Wish I Knew Before Starting Cybersecurity
Addie LaMarr
74.0K views
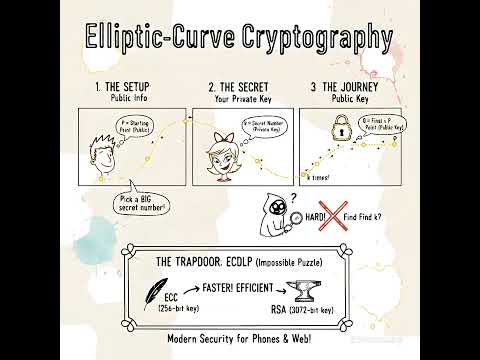
1:26
Encryption: Elliptic-Curve Cryptography #cryptography #encryption #cybersecurity #cissp
The Cyber Dojo
211 views
0:16
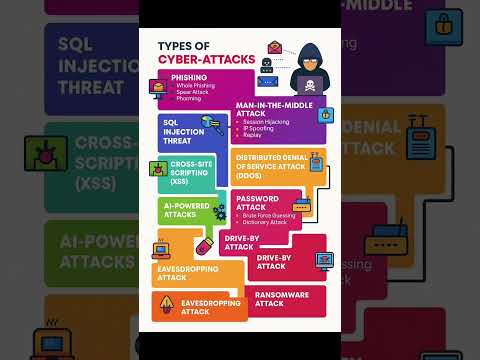
Types of Cyber-Attacks!!! #ccna #cybersecurity #networking #programming #techshorts #cryptocurrency
Networks Professionals
11 views
1:26
Cybersecurity Shorts: Day 97 - What is HASHING ?
Shiva Ram Tech
1.4K views

8:25
Russia-Ukraine conflict and US cybersecurity | Dig In 2 It
WFMY News 2
18.2K views
3:52
Cryptography University of Maryland,College Park | Cryptography Week 3 |Cybersecurity Specialization
Career4freshers
207 views

0:59
Password vs Passkey #cybersecurity #dev #code #softwareengineer #programming
Beyond Identity
56.5K views

9:34
Cybersecurity Trends and Essential Skills for 2025
Tiff In Tech
9.0K views
0:35
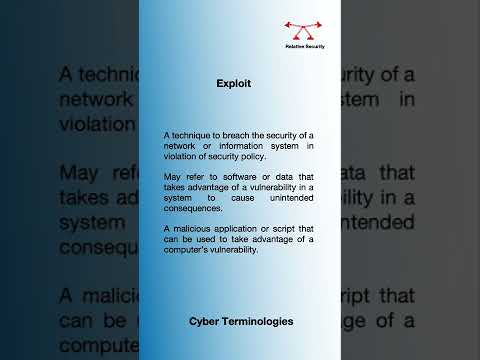
CyberSecurity Definitions | Exploit
Relative Security
503 views

5:02
Cybersecurity and crime | Internet 101 | Computer Science | Khan Academy
Khan Academy
316.2K views
0:51
CISSP Quiz #quiz #cybersecurity
LufSec Cyber Security
115 views

0:43
Encryption Explained: How to Protect Your Data from Hackers #cybersecurity #technology #tech
HackTales
65 views
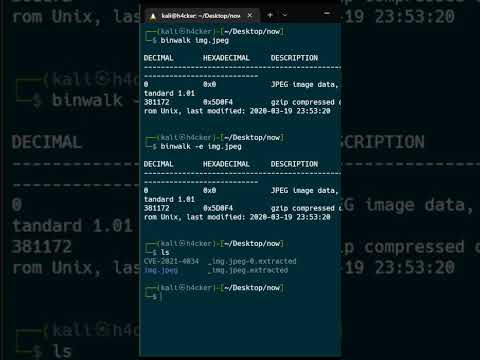
0:38
Binwalk Image forensic extract information from image #cybersecurity #imageforensic #binwalk #exif
Zodiac
8.1K views
31:15
Cybersecurity Architecture: Who Are You? Identity and Access Management
IBM Technology
369.5K views
1:49
How to Solve CTFs (Capture The Flag) | Complete Beginner’s Guide #ctfchallenge #ctf #cybersecurity
MainEkHacker
3.7K views
1:30
Top Cybersecurity Expert Reveals Best Encryption Techniques
MonkWire
89 views

1:24
Der Vastaamo Fall #informatik #cybersecurity #fakten #wissen
Hood Informatik
11.1K views

59:29
Cybersecurity Basics: Crash Course for Beginners
Coding Bootcamps
6 views
0:59
3 programming Languages to learn in 2023 for cybersecurity #shorts
Cybersecurity Guy
293 views
9:34
(CH7/2) Cryptography - Types of Cybersecurity Attacks Part 2
FENIXSOYA
30 views

1:24
Session Hijacking Explained in less than 90 Seconds #SessionHijacking #Cybersecurity #EthicalHacking
Yaniv Hoffman
5.5K views

3:14
What Is The Difference Between Symmetric And Asymmetric Encryption In Cybersecurity?
Your Engineering Future
1 views
0:58
Revolutionizing Cybersecurity with Quantum Key Distribution
Tech Visionary Insights
0 views

0:39
Best Cybersecurity Jobs of 2024!
Daily CyberConnect
23 views

1:00
What is IoT ? Internet of things: Explained #cybersecurity #shorts
TutorialsFreak
805 views
0:24
CyberSecurity Definitions | Man in the Middle Attack
Relative Security
969 views
0:16
Decrypt Files Instantly with AES-256 🔓 | Python Decryption Tool | Cybersecurity Project
Esraa Codes
1.9K views

1:08
Hybrid Cryptography: Future-Proof Your Security! #shorts #cybersecurity
Your SASE Gateway
405 views
4:52
Cybersecurity | Cryptography | Caesar Cipher
Naresh KSHETRI
104 views
1:00
About of Bitcoin fraud #cybercrime #cybersecurity #digitalforensics
FDI LABS CLASSROOM
29 views

7:57
2024 Cybersecurity Trends
IBM Technology
222.7K views

1:54:16
ASC Webinars: Cybersecurity from Zero to Hero - Mohammad Khreesha
Arab Security Conference
2.5K views

0:09
What is Cryptography? #cybersecurity #cyber #security #terms #tech #learn
IT and Cyber Security Definitions
1.8K views

11:50
Try These Cybersecurity Projects For Beginners to Get HIRED in 2025: Top 5 Beginner Cyber Projects
With Sandra
46.0K views

0:09
🔒 SSL (Secure Sockets Layer) 🌐 | Data Encryption, Cybersecurity & Safe Web Browsing
Smart Digital Pakistan
138 views
0:48
Caesar Cipher Explained: Oldest Encryption Technique! 🔐L#shorts #cybersecurity
Tech With Vyshali
961 views

5:37
How to store hidden information in Kali Linux using Steghide| Steganography| Cybersecurity
Revathy Mohan Kannara
61 views
2:39
How Will Cybersecurity Standardize Post-quantum Cryptography? - Quantum Tech Explained
Quantum Tech Explained
0 views
0:46
What is Steganography | Secure your data #ethicalhacking #hindi #cybersecurity #hindishorts
Cyberverse Academy
4.9K views

0:04
Symmetric vs Asymmetric Encryption #cybersecurity #networking #shorts
Build IT Skill
906 views

0:59
Quantitative Risk Analysis #cissp #cisa #ccsp #cism #crisc #cybersecurity
InfoSec Guardians
328 views

2:06
The History of Cryptography and Modern Cybersecurity
PtrckM
19 views
0:06
phishing #cybersecurity #cyber #attacks #shorts
Cybergram
272 views

0:48
Diferença entre criptografia simétrica e assimétrica #hacker #cybersecurity #criptografia #ssh
HackingNaTuga
81 views