Search Results for "authentication protocols"
Find videos related to your search query. Browse through our collection of videos matching "authentication protocols". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "authentication protocols"
50 results found

11:49
Authentication functions and 3 ways to produce authentication | Message authentication
Abhishek Sharma
263.4K views

6:12
#33 Message Authentication & Authentication Functions in Cryptography |CNS|
Trouble- Free
193.2K views

13:38
Cryptography (18CS744) Mutual authentication, one way authentication, kerberos and kerberos diff
1VA19CS061 YASHAS HM
106 views

6:52
MAC / HMAC - Message Authentication Code / Hash Bashed Message Authentication Codes
Practical Networking
30.0K views
19:53
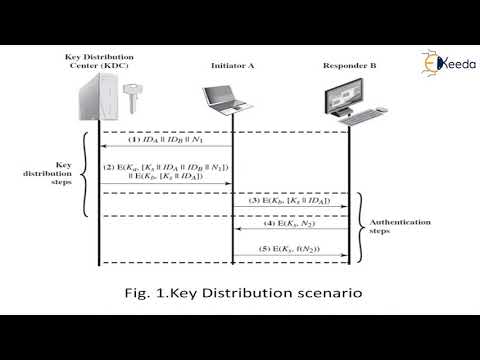
User authentication protocols | Cryptography and System Security
Ekeeda
307 views
1:09:38
CSE571-11-15B: User Authentication Protocols (Part 2 of 3)
Raj Jain
1.8K views
17:04
UNIT IV-COMMUNICATION SECURITY,AUTHENTICATION PROTOCOLS
janadeep n
24 views
1:20:56
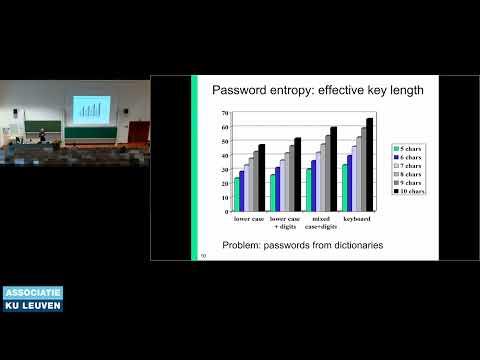
COSIC Course 2024: "Cryptographic protocols for entity authentication and..." (Bart Preneel, COSIC)
COSIC - Computer Security and Industrial Cryptography
239 views
0:59
Protocols | meaning of Protocols
The Definition Channel
504 views

0:11
network protocols and ports | networking protocols interview questions
Technical Spartan - Thakur
149.4K views

1:21
Solar Energy - Renewable Energy - Montreal Protocols & Kyoto Protocols
Cyber Energy Ltd
11 views
0:08
Read [ AACN Protocols for Practice: Noninvasive Monitoring[ AACN PROTOCOLS FOR PRACTICE: NONINVASIVE
Airini Arono
0 views

0:05
Download Telephone Triage Protocols for Adults 18 Years and Older (Telephone Triage Protocols
MarianRench
1 views
0:35
Best product Telephone Triage Protocols for Nurses (Briggs, Telephone Triage Protocols for
walker
1 views
![[Read] TCP/IP Illustrated, Volume 1: The Protocols: The Protocols v. 1 (Addison-Wesley](/image/s2.dmcdn.net/v/Pt3_y1e9_0lvZvH-V/x720)
0:33
[Read] TCP/IP Illustrated, Volume 1: The Protocols: The Protocols v. 1 (Addison-Wesley
phamza-elhaddars
7 views
0:36
TCP/IP Illustrated, Volume 1: The Protocols: Protocols v. 1 (APC) Review
yoheg
5 views

4:37
Adherence to Covid-19 Protocols: Clamp-down on persons violating protocols begins (10-8-21)
The Multimedia group
3 views
7:14
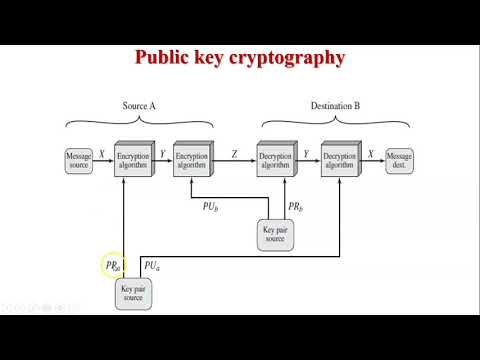
Application of public key cryptography | Authentication | Confidentiality | Digital Signature
Chirag Bhalodia
22.5K views

31:22
23-IP Security (IPSec) Part 1 🔐 | Authentication Header Explained | Network Security
Sundeep Saradhi Kanthety
204.7K views
15:16
5 1 Message Authentication Codes 16 min
Osiris Salazar
2.7K views

51:12
Authentication-1 : MSR VTU CNC
Rohit M
41 views

6:49
Message Authentication Code (MAC)
cipaaa
6 views

1:10:42
B Level - NMIS 5 Public Key Infrastructure & Message Authentication
Online Free Education
13 views
39:03
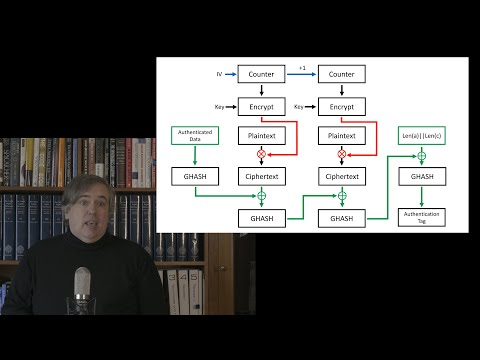
Covid Cryptography 6: Message Authentication Codes and Authenticated Encryption
MathMesh
122 views

12:55
Types of Message Authentication | Message Encryption | Part 1 | Network Security | Hindi Urdu
Ask Faizan
4.3K views

12:48
How Kerberos Authentication Works and Why You Should Use It Detailed Explanation in Telugu
Lucky Tech
7.7K views

7:01
#40 Kerberos - Authentication Protocol, Working with diagram|CNS|
Trouble- Free
304.6K views
2:16:38
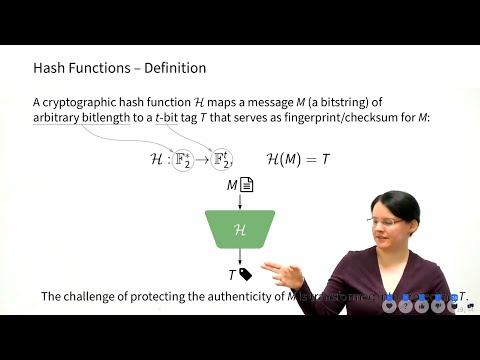
InfoSec L1 - Crypto 1 - Authentication
Maria Eichlseder
4.9K views

0:09
What is Authentication? #cybersecurity #learn #terms #cyber #security #tech
IT and Cyber Security Definitions
750 views

6:23
Secrecy and Authentication using Public-Key/Two-Key Cryptography or Asymmetric Encryption
CSE Adil
86 views

0:26
EKE Authentication - Applied Cryptography
Udacity
1.4K views
7:42
Digital Signature - Asymmetric Key , Why used for Authentication & Non Repudiation (Hindi)
Easy Engineering Classes
177.3K views
8:08
MAC in Hindi - Message Authentication Code Process, Significance, HMAC Concept
Easy Engineering Classes
111.9K views
16:52
Kerberos Authentication Explained | A deep dive
Destination Certification
424.5K views

11:28
Kerberos Version 4 | Kerberos Version 4 using Authentication and Ticket Granting Server
Chirag Bhalodia
27.4K views
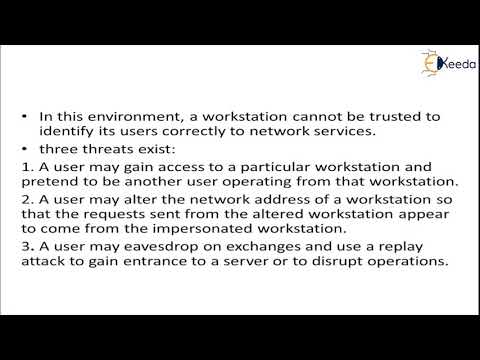
4:49
Kerberos Authentication Protocol | Cryptography and System Security
Ekeeda
56 views
10:28
Module 5.2 Message Authentication Functions
bushara abdulrahim
2.9K views

20:53
Remote User Authentication Using Symmetric Encryption | Needham Shcroeder Protocol
Chirag Bhalodia
33.5K views
31:30
AUTHENTICATION REQUIREMENTS_FUNCTIONS_MAC_HASH FUNCTION
IN TECH
333 views

14:09
Information Security Measures (Authentication, Digital Signature, Firewalls, Steganography)
5-Minute Lessons by Victor
973 views

1:01
What is Kerberos ? #cissptraining #cissp #cybersecurity #authentication #itsecurity #securityconcep
IT Tech Insights
5.6K views
0:44
Kerberos Authentication Explained | How Login Tickets Work in Enterprise Security #CISSPFlashcards
Cyber Security Learning
3.2K views

0:49
Message authentication code (MAC)
Real programming
693 views

5:01
Fix the Authentication Required Problem in Netbeans
ULTIMΔTE DOT
19.3K views
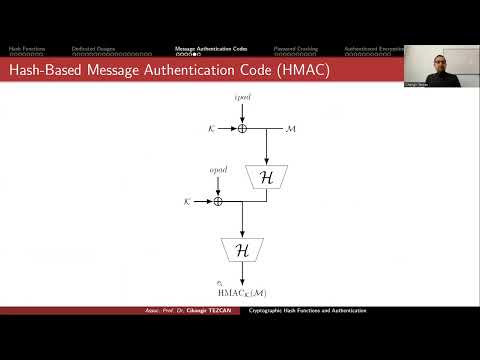
7:13
MACs Message Authentication Codes in Network Security
Cihangir Tezcan
145 views
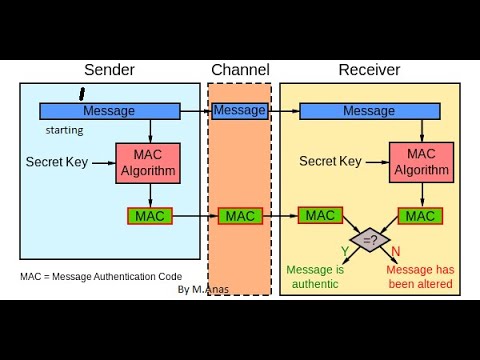
20:53
MAC in Cryptography || Message Authentication Code in Network Security And Cryptography.
Anas Khan
192 views
1:05
Fast Authentication using Chameleon Hashing Key Chain
University of Glasgow Singapore
229 views
1:00:51
CNIT 141: 12. Message Authentication Codes (MACs) and 13. Key Establishment
Sam Bowne
136 views
14:12
Kerberos Authentication
Mervin Pearce
57.5K views
10:48
Module 5.3_Message Authentication Code,Secure communication ktu s8 ec #engineering #ktutuition
bushara abdulrahim
2.3K views
Page 1