Search Results for "Protocol Vulnerabilities"
Find videos related to your search query. Browse through our collection of videos matching "Protocol Vulnerabilities". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "Protocol Vulnerabilities"
50 results found

2:06
Virtual Protocol Latest News Today In Hindi | Virtual Protocol Crypto | Virtual Protocol News | BTC
MR KRYPTO
42 views

0:30
Rangers protocol vvip protocol Punjab pakistan | Rangers | protocol vvip | Ghouri4u Official
Ghouri4u official
18 views

25:17
CS C S009 Non-Cryptographic Protocol Vulnerabilities
Studio IIT Bombay
539 views

41:17
CS M S022 Non-Cryptographic Protocol Vulnerabilities
Studio IIT Bombay
429 views

0:32
How Attackers Exploit Diameter Protocol Vulnerabilities
Offensive Wireless
523 views

9:11
TCP/IP Model | Internet protocol suite | Protocol and services of TCP/IP Model
Chirag Bhalodia
1.5K views

8:37
SSH (Secure shell) protocol in Hindi | Secure shell protocol in Network Security
Abhishek Sharma
84.3K views

3:22
Alpha Protocol - Alpha Protocol - Developers Diary
Games2C_INT
9 views

2:05
Ed Protocol Ingredients || Erectile Dysfunction Protocol
Helenaghv
8 views

9:59
Alpha Protocol Walkthrough - Infiltrate Alpha Protocol ...
MahaloGames
1 views

1:32
Massive protocol PM Abbasi Protocol in Karachi
MTV
49 views

5:18
Session 11 : Open RAN Protocol Stack | PDCP Protocol and SDAP Layer
Learn And Grow Community
10 views

1:24
IMAM E KABA PROTOCOL IN PAKISTANIMAM E KABA PROTOCOL IN PAKISTAN
All In one
1 views

2:33
Ed Protocol Review || Erectile Dysfunction Protocol Review
Vernitaw0z
1 views

0:06
Encryption Protocol. #cybersecurity #cyberpunk #viral #protocol #sslcertificate
Infintysec
179 views

1:27
people Bushing Sharif Brothers Because of protocol In jinah hospital because of protocol
harpal.pk
16 views

1:45
erase herpes protocol review - erase herpes protocol
Get rid of hives
24 views

11:00
Web and HTTP protocol tutorial | Hypertext Transfer Protocol explained | World Wide Web | TechTerms
TechTerms
65.6K views

14:31
Network Protocol Explained | Types Of Network Protocol | Fundamentals Of Networking | Simplilearn
Simplilearn
1.4K views

5:35
Cryptography Basics: Symmetric and Asymmetric Cryptography - Identifying Security Vulnerabilities
Petrina Corine
25 views

34:39
Cryptography careers and IoT vulnerabilities | Cyber Work Podcast
Infosec
4.0K views
3:21
How Does The Rise Of AI Impact Military Cryptography Vulnerabilities? - Tactical Warfare Experts
Tactical Warfare Experts
17 views

2:26:01
Virtual Machine Reset Vulnerabilities; Subspace LWE; Cryptography Against Continuous Memory Attacks
Microsoft Research
314 views

2:56
How Common are Cryptographic Vulnerabilities?
Cryptosense
615 views

1:32:49
RWPQC 2024 Session 5: Applied Cryptography, Vulnerabilities, and Countermeasures
SandboxAQ
26.2K views

38:56
Nmap Tutorial For Beginners | Nmap Tutorial to find Network Vulnerabilities | Amader Canvas
Amader Canvas
45.1K views
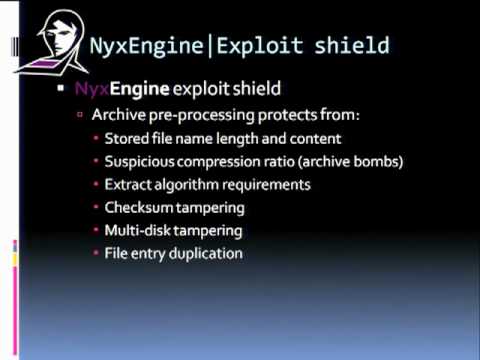
10:01
Blackhat Europe 2010: Steganography and Vulnerabilities in Popular Archives Formats 7/8
Christiaan008
148 views

1:11:10
Black Hat EU 2010 - Hiding in the Familiar: Steganography & Vulnerabilities in Pop Archives Formats
Black Hat
231 views
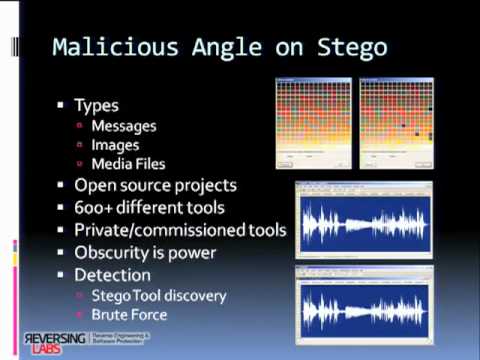
10:01
Blackhat Europe 2010: Steganography and Vulnerabilities in Popular Archives Formats 1/8
Christiaan008
1.8K views
0:47
Researchers Discover New Vulnerabilities In Common Email Encryption Tech
Entertainment (now)
5 views
0:46
Risks Are Accelerating, Yet Traditional Security Vulnerabilities Plague Cryptocurrencies
Benzinga
14 views

10:41
USENIX Security '20 - TeeRex: Discovery and Exploitation of Memory Corruption Vulnerabilities...
USENIX
668 views
8:44
Armitage- Scanning a network for computers and finding their Vulnerabilities
DonDoes30
19 views
10:01
Blackhat Europe 2010: Steganography and Vulnerabilities in Popular Archives Formats 6/8
Christiaan008
194 views

5:45
Threats Vulnerabilities and Exploits
IBM Technology
34.4K views

17:37
TWIM Episode 2: Sodinokibi Ransomware Vulnerabilities & Maryland Criminalizes Malware Possession
This Week in Malware
66 views

29:23
Quantum Threat: Impact of Quantum Computers on Cybersecurity | Threats & Vulnerabilities Summit 2025
Cloud Security Alliance
155 views

20:58
Hackers expose deep cybersecurity vulnerabilities in AI | BBC News
BBC News
524.3K views
0:33
SQL Injection 101: Exploiting Vulnerabilities
CyberSquad
354.4K views

0:18
Critical Go Parser Vulnerabilities Enable Authentication Bypass and Data Theft in Production Systems
Secure Thread
122 views

5:10
Exploiting Windows Vulnerabilities with Metasploit
Hak5
831 views
9:35
Data Exfiltration Vulnerabilities in LLM Applications and Chatbots: Bing Chat, ChatGPT and Claude
Embrace The Red
1.9K views
4:48
What Are The Biggest Microservices Security Vulnerabilities? - Next LVL Programming
NextLVLProgramming
6 views
3:27
How Hackers Scan Vulnerabilities of Any Website | Nikto - Kali Linux
HackHunt
30.0K views

2:06:36
Cybersecurity Assets, Network Threats & Vulnerabilities | Google Cybersecurity Certificate
Google Career Certificates
153.5K views
0:41
911 Outage Sparks Concerns Over Emergency System Vulnerabilities
Benzinga
610 views
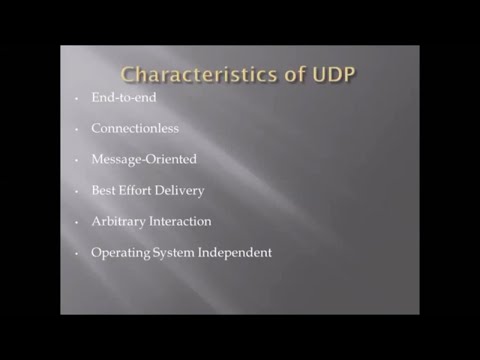
2:30
Briefly describe on characteristics of the UDP(User datagram protocol)
Informative Tutorials
159 views

17:02
9 - Cryptography Basics - SSH Protocol Explained
CBTVid
43.1K views
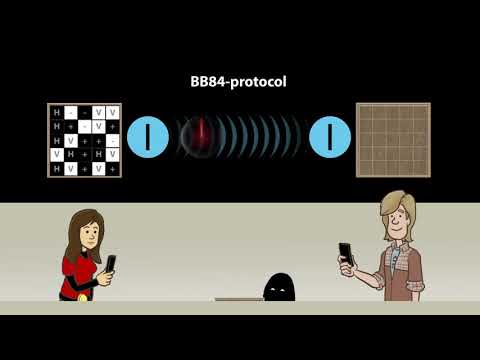
3:45
Quantum cryptography: The BB 84 protocol (U3-02-03)
QuantumVisions
32.1K views

0:11
Which protocol is used to securely transfer files over the internet?
KrofekSecurity
38 views
Page 1