Search Results for "Diffie-Hellman vulnerabilities"
Find videos related to your search query. Browse through our collection of videos matching "Diffie-Hellman vulnerabilities". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "Diffie-Hellman vulnerabilities"
44 results found
25:17
CS C S009 Non-Cryptographic Protocol Vulnerabilities
Studio IIT Bombay
539 views

38:56
Nmap Tutorial For Beginners | Nmap Tutorial to find Network Vulnerabilities | Amader Canvas
Amader Canvas
45.1K views

5:45
Threats Vulnerabilities and Exploits
IBM Technology
34.4K views

2:26:01
Virtual Machine Reset Vulnerabilities; Subspace LWE; Cryptography Against Continuous Memory Attacks
Microsoft Research
314 views

20:58
Hackers expose deep cybersecurity vulnerabilities in AI | BBC News
BBC News
524.3K views

1:11:10
Black Hat EU 2010 - Hiding in the Familiar: Steganography & Vulnerabilities in Pop Archives Formats
Black Hat
231 views

29:23
Quantum Threat: Impact of Quantum Computers on Cybersecurity | Threats & Vulnerabilities Summit 2025
Cloud Security Alliance
155 views

10:41
USENIX Security '20 - TeeRex: Discovery and Exploitation of Memory Corruption Vulnerabilities...
USENIX
668 views
10:01
Blackhat Europe 2010: Steganography and Vulnerabilities in Popular Archives Formats 7/8
Christiaan008
148 views

17:37
TWIM Episode 2: Sodinokibi Ransomware Vulnerabilities & Maryland Criminalizes Malware Possession
This Week in Malware
66 views
0:33
SQL Injection 101: Exploiting Vulnerabilities
CyberSquad
354.4K views
0:18
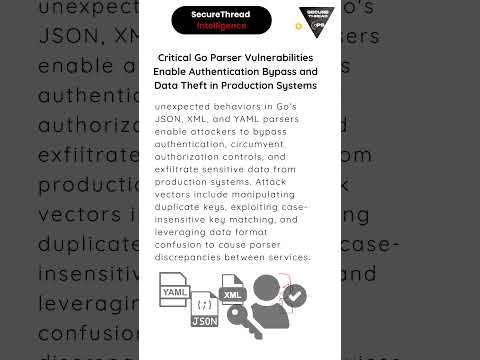
Critical Go Parser Vulnerabilities Enable Authentication Bypass and Data Theft in Production Systems
Secure Thread
122 views

9:35
Data Exfiltration Vulnerabilities in LLM Applications and Chatbots: Bing Chat, ChatGPT and Claude
Embrace The Red
1.9K views

2:56
How Common are Cryptographic Vulnerabilities?
Cryptosense
615 views
4:48
What Are The Biggest Microservices Security Vulnerabilities? - Next LVL Programming
NextLVLProgramming
6 views
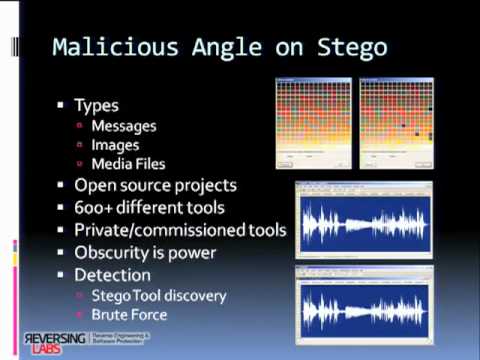
10:01
Blackhat Europe 2010: Steganography and Vulnerabilities in Popular Archives Formats 1/8
Christiaan008
1.8K views

5:35
Cryptography Basics: Symmetric and Asymmetric Cryptography - Identifying Security Vulnerabilities
Petrina Corine
25 views

2:06:36
Cybersecurity Assets, Network Threats & Vulnerabilities | Google Cybersecurity Certificate
Google Career Certificates
153.5K views
34:39
Cryptography careers and IoT vulnerabilities | Cyber Work Podcast
Infosec
4.0K views

0:32
How Attackers Exploit Diameter Protocol Vulnerabilities
Offensive Wireless
523 views

3:27
How Hackers Scan Vulnerabilities of Any Website | Nikto - Kali Linux
HackHunt
30.0K views
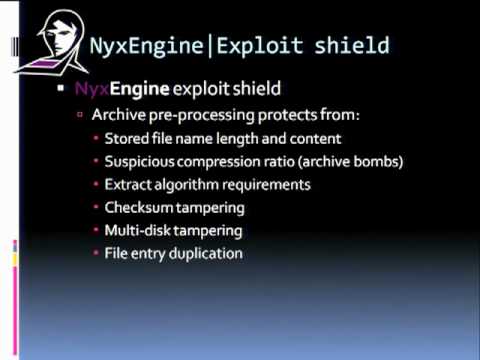
10:01
Blackhat Europe 2010: Steganography and Vulnerabilities in Popular Archives Formats 6/8
Christiaan008
194 views
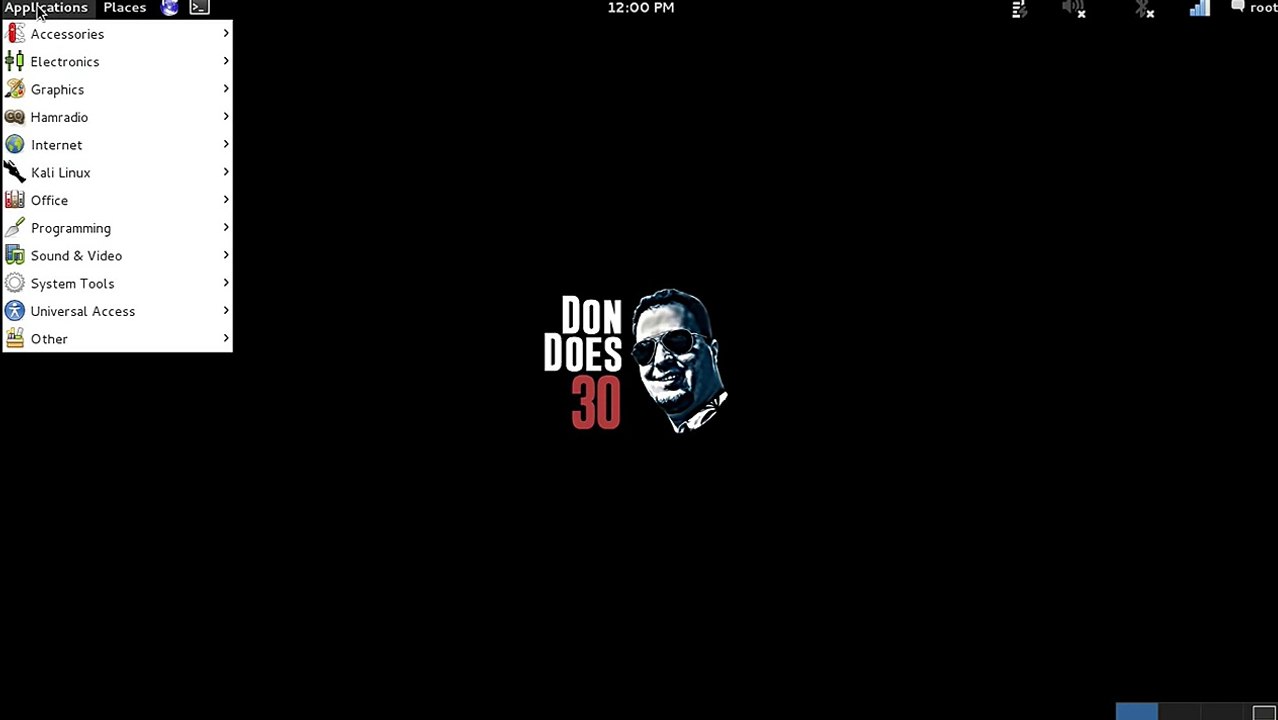
8:44
Armitage- Scanning a network for computers and finding their Vulnerabilities
DonDoes30
19 views

5:10
Exploiting Windows Vulnerabilities with Metasploit
Hak5
831 views

0:47
Researchers Discover New Vulnerabilities In Common Email Encryption Tech
Entertainment (now)
5 views

0:46
Risks Are Accelerating, Yet Traditional Security Vulnerabilities Plague Cryptocurrencies
Benzinga
14 views

1:59
Week 1 Rust And Vulnerabilities: Bengals Vs. Browns
SportsGrid
3.2K views
0:41
911 Outage Sparks Concerns Over Emergency System Vulnerabilities
Benzinga
610 views

1:04
The Weeknd has used music to 'hide' his vulnerabilities
Bang Showbiz
486 views

1:32:49
RWPQC 2024 Session 5: Applied Cryptography, Vulnerabilities, and Countermeasures
SandboxAQ
26.2K views

41:17
CS M S022 Non-Cryptographic Protocol Vulnerabilities
Studio IIT Bombay
429 views
3:21
How Does The Rise Of AI Impact Military Cryptography Vulnerabilities? - Tactical Warfare Experts
Tactical Warfare Experts
17 views
0:57
A Day in the Life of Cryptography Pioneer Whitfield Diffie
Gloves Off!
26 views
3:18
Diffie Hellamn Key Exchange Algorithm with Example in Hindi
Sharif Khan
3.9K views

2:31
2 Minutes with Turing Award Winner Whitfield Diffie
Tom Rocks Maths
9.6K views

20:02
ELLIPTIC CURVE CRYPTOGRAPHY & DIFFIE HELMAN KEY EXCHANGE ||ASYMMETRIC KEY CRYPTOGRAPHY
t v nagaraju Technical
47.6K views
1:16:30
Stanford Seminar - Cryptology and Security: the view from 2016 - Whitfield Diffie
Stanford Online
11.2K views

2:26:40
Whitfield Diffie, 2015 ACM Turing Award Recipient
Association for Computing Machinery (ACM)
9.1K views

0:51
Whitfield Diffie Cryptography Pioneer #shorts #Global #History #News
I'm Zoran
215 views
1:06:14
Whit Diffie's S4x07 Keynote on the History of Cryptology
S4 Events
1.2K views

14:06
Discovery of Public Key Cryptography with Whitfield Diffie (2015 Turing Award)
Tom Rocks Maths
20.0K views
1:14:31
Whitfield Diffie on the History of Cryptography
Peter McCormack
4.1K views

1:01
Country Star Joe Diffie Dies From Coronavirus Complications
Veuer
475 views
2:34
What Is Diffie's Contribution To Public Key Cryptography? - History Icons Channel
History Icons Channel
1 views
Page 1