Search Results for "cookies vulnerability"
Find videos related to your search query. Browse through our collection of videos matching "cookies vulnerability". Search across titles, descriptions, tags, and channels to discover the content you're looking for.
Search Results for "cookies vulnerability"
51 results found
0:24
What is Vulnerability? Types of Vulnerability in Cybersecurity
a2zOfCloud
2.5K views

0:21
Christmas Cookies 🎄🍪#baking #cookies #easyrecipe #gingerbread #christmas #holiday #xmas #chocolate
Maria Gomez
567.5K views

0:15
Turkey Cookies for Fall! 🦃 #easyrecipe #cookies #momlife #shorts
The Vincent Fam
12.3K views
8:30
Silk Typhoon Member Arrested, Chromium Vulnerability & Call of Duty | cybernews.com
Cybernews
12.6K views
2:26
Unauthorized Access Admin Panel Vulnerability
Ibnu Fachrizal
230 views
0:48
Cryptographic Vulnerability?. #cybersecuritylearning #cyber fundamentals #cyber101
a2zOfCloud
25 views
4:18
Vulnerability Analysis of Cryptographic Modules Against Hardware-Based Attacks
VALU3S Project
146 views

0:16
Secp256k1 DHEC vulnerability
teknopath aka moonshine
374 views

12:12
OSI Security Architecture - Attacks, Services, Mechanisms, Vulnerability, Threats, Risk
Mukesh Chinta
501 views

20:50
The Power of Vulnerability | Brené Brown | TED
TED
23.9M views
47:05
Lecture 2 | Goals of Security, Vulnerability & Threat | Cryptography and System Security
Sridhar Iyer
1.3K views
2:26
Strengthening Cyber Defenses: CISA’s Free Vulnerability Scanning Explained
CISA
4.2K views

10:14
Diffie-Hellman Key Exchange Vulnerability
Mert Özbay
334 views

0:16
Buffer Overflow Explained: Breaking Down the Code Vulnerability! #short #shortvideo #shorts
Aarnaaology
147 views

0:27
Vulnerability Scanning Tools #shorts
ZeroDay Vault
87 views
4:13:07
SOC100 Class 20 - Vulnerability Management, Cryptography, Symmetric & Asymmetric Encryption Part 1
Level Effect
534 views

7:10
Cybergang Shutdown, Linux Vulnerability & Microsoft | Weekly News
Cybernews
9.4K views

0:59
What is Cross Site Scripting (or XSS) Vulnerability in Cybersecurity
Learn with Whiteboard
56.5K views

0:52
Exploiting CSRF Vulnerability
the security vault
109 views

0:58
Orca CEO Insights | Vulnerability Management and Risk Prioritization
Orca Security
112 views

4:50
Stop using Cursor NOW. Major security vulnerability.
Goju Tech Talk
112.7K views
32:41
Your AI Vulnerability: The Psychological Trap of Talking to AI
Verlicity AI
8 views
41:27
OL: Vulnerability
jamesbarber4
178 views

24:51
AI-Enabled Post-Quantum Cryptography Migration: Trust and Vulnerability Discovery - Mark Tehrani
Bill Buchanan OBE
314 views

2:27
Stay advanced with promisec Vulnerability Scanning Tools
Alan Taylor
4 views
4:30
Why Vulnerability Testing Is Important
SURESH sur5031
0 views

0:55
Lizzo: Vulnerability is important
Bang Showbiz Extra
154 views

10:52
Krack Attacks (WiFi WPA2 Vulnerability) - Computerphile
qwak1234
1 views
21:23
Lesson 3 - Vulnerability
azizsaya
190 views

0:58
OpenSSL’s New Fix For Heap Memory Corruption Vulnerability!
Kratikal
0 views
47:45
The Glee Project S01E03 Vulnerability
Glee
2.1K views

48:32
The Glee Project S02E03 Vulnerability 2
Glee
1.3K views

3:37
Women DON'T Want Vulnerability
Teeb TV–Indie Filmmaking | Mental Tips
5.4K views

4:32
what is vulnerability in cyber security
Noor_khan official
30 views

2:56
Taraji P. Henson Says Her Strength Is Her 'Vulnerability': 'I Lean Into' It
US Weekly
2.4K views

2:04
Nicole Kidman on Vulnerability in 'Babygirl' | Academy Museum Gala Red Carpet
Variety
505 views

0:12
Lebron shows vulnerability in heartfelt moment with Bronny
Marca
1.1K views
1:30
'Critical vulnerability': Data reveals very low energy independence across EU
euronews (in English)
1.6K views

41:35
This Michelin-Rated Restaurateur Found Success in Digital Media with Strategic Vulnerability
Entrepreneur
176 views

0:40
Unlocking the Secrets of Vulnerability
CyberGuard
0 views
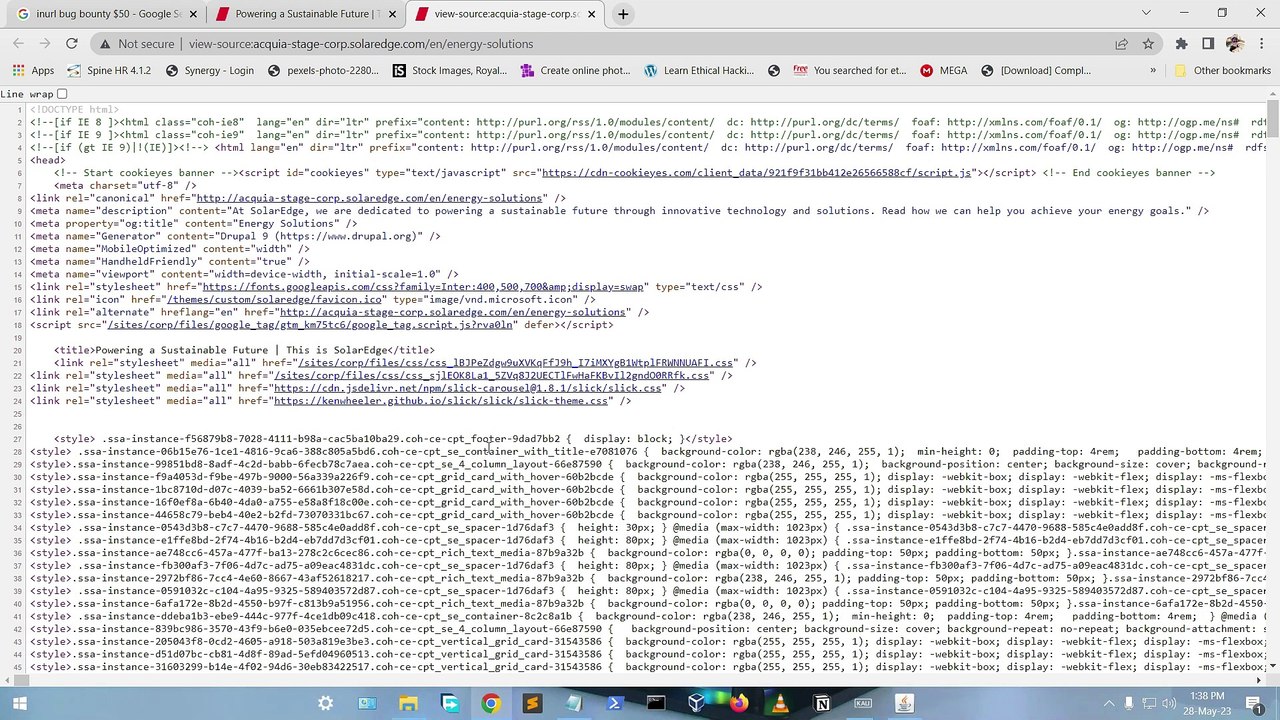
1:15
Google API key vulnerability | Bug Bounty
Arfi Tutorials
20 views
0:44
Data Vulnerability Why Encryption Matters
CyberGuard
1 views

0:37
Vulnerability Assessment and Penetration Testing (VAPT)
apprise-cyber
9 views

2:00
Why is Vulnerability Important?
JasminBalance
25 views

0:59
$20,000 Misconfigured S3 bucket vulnerability #bugbounty #bugbountytips
Bug Bounty Reports Explained
19.9K views

0:57
Women need to know this about men. #fyp #vulnerability
emilywking
3.2M views

8:10
No Bake Thanksgiving Cookies: Oreo Candy Corn Turkeys, Rolo Pilgrim Hats & Nutter Butter Acorns
Cookies Cupcakes and Cardio
189.9K views

2:30
Thanksgiving Cookies - Turkey Oreos - Annual Beck Thanksgiving Tradition
Ranger Press
13 views

0:20
The BEST holiday chocolate chip cookies you'll ever bake!
Little Remy Food 🐭🍝
11.6M views

0:53
Turkey Oreo Cookies #shorts #Thanksgiving
FunFoods
4.3K views

3:37
Women DON'T Want Vulnerability
Teeb TV–Indie Filmmaking | Mental Tips
5.4K views
Page 1 Next